# Stratosphere
## Stratosphere - 10.10.10.64
### Target Enumeration:
OS: Linux
IP: 10.10.10.64
User: e610b298611fa732fca1665a1c02336b
Root: d41d8cd98f00b204e9800998ecf8427e
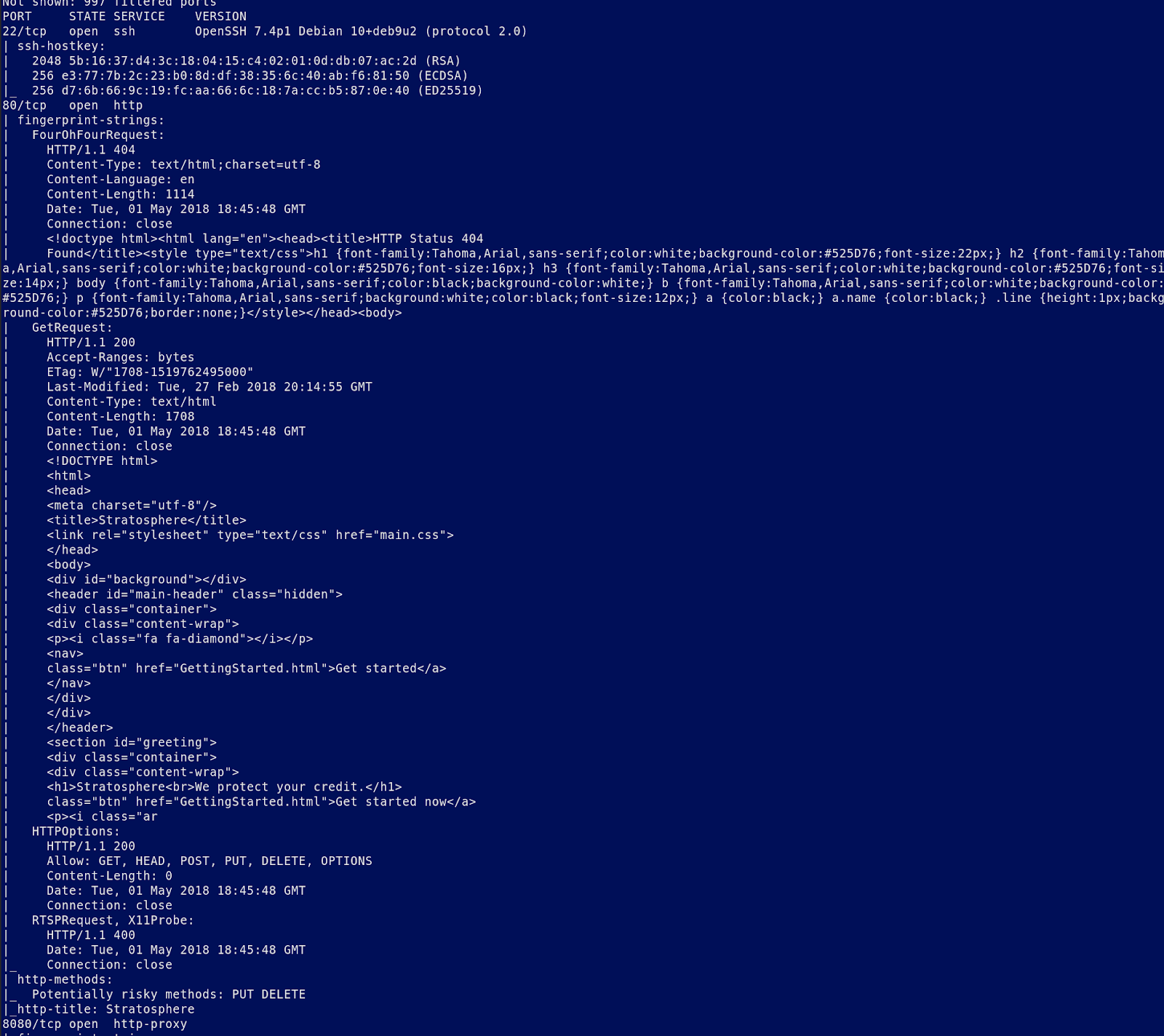
### Ports / Services / Software Versions Running
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u2 (protocol 2.0)
80/tcp open http
8080/tcp open http-proxy
### Vulnerability Exploited:
Apache Struts vulnerability to read mysql database gives ssh password for user richard
### Privilege Escalation:
User allowed to run python as sudoer
Python input() vulnerability allows root command execution
### Exploiting the host:
Nmap (8080 is not included in screenshot)