# October
## October - 10.10.10.16
### Target Enumeration:
OS: Linux
IP: 10.10.10.16
User: 29161ca87aa3d34929dc46efc40c89c0
Root: 6bcb9cff749c9318d2a6e71bbcf30318
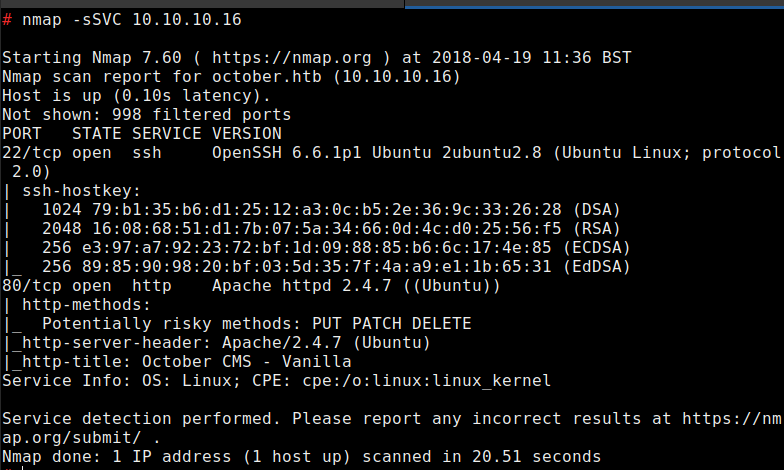
### Ports / Services / Software Versions Running
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.8 (Ubuntu Linux; protocol 2.0)\
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))\
Vulnerability Exploited:
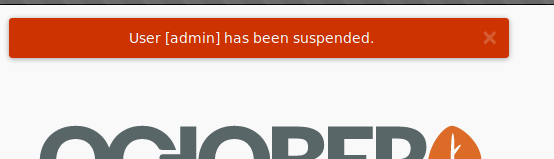
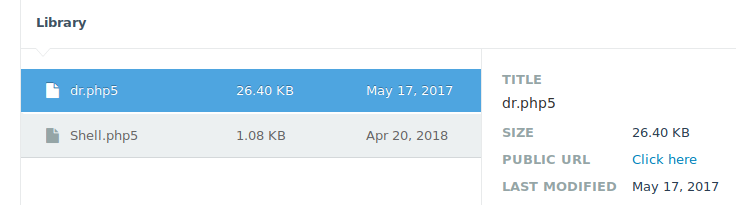
Weak password on CMS
### Privilege Escalation:
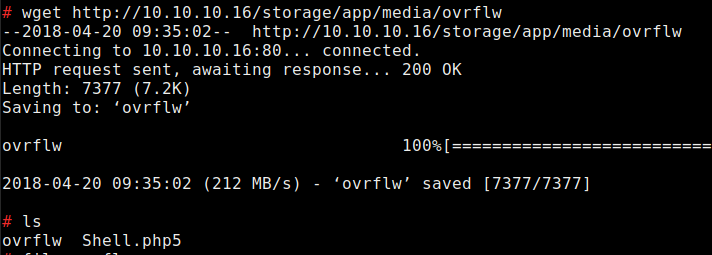
Buffer overflow on /usr/local/bin/ovrflw
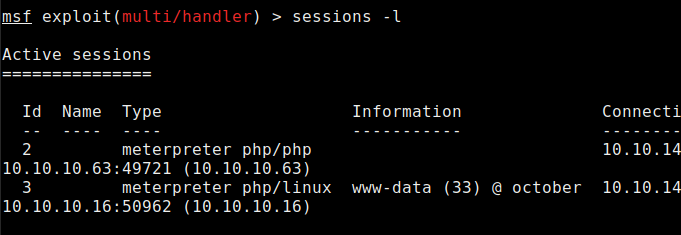
### Exploiting the host:
Nmap
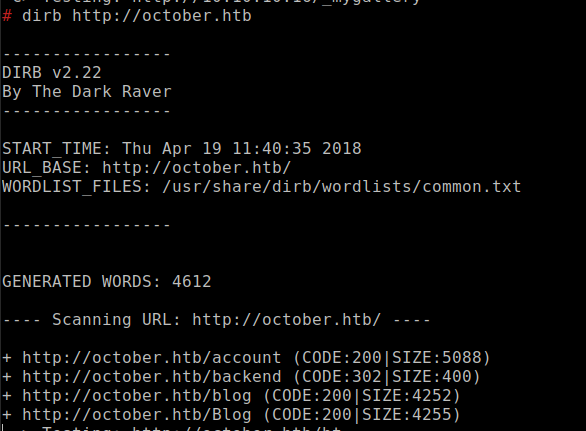
Dirb