# Olympus
## Olympus - 10.10.10.83
### Target Enumeration:
OS: Linux
IP: 10.10.10.83
User: 8aa18519aff3c528c46bf675d6e88719
Root: aba486990e2e849e25c23f6e41e5e303
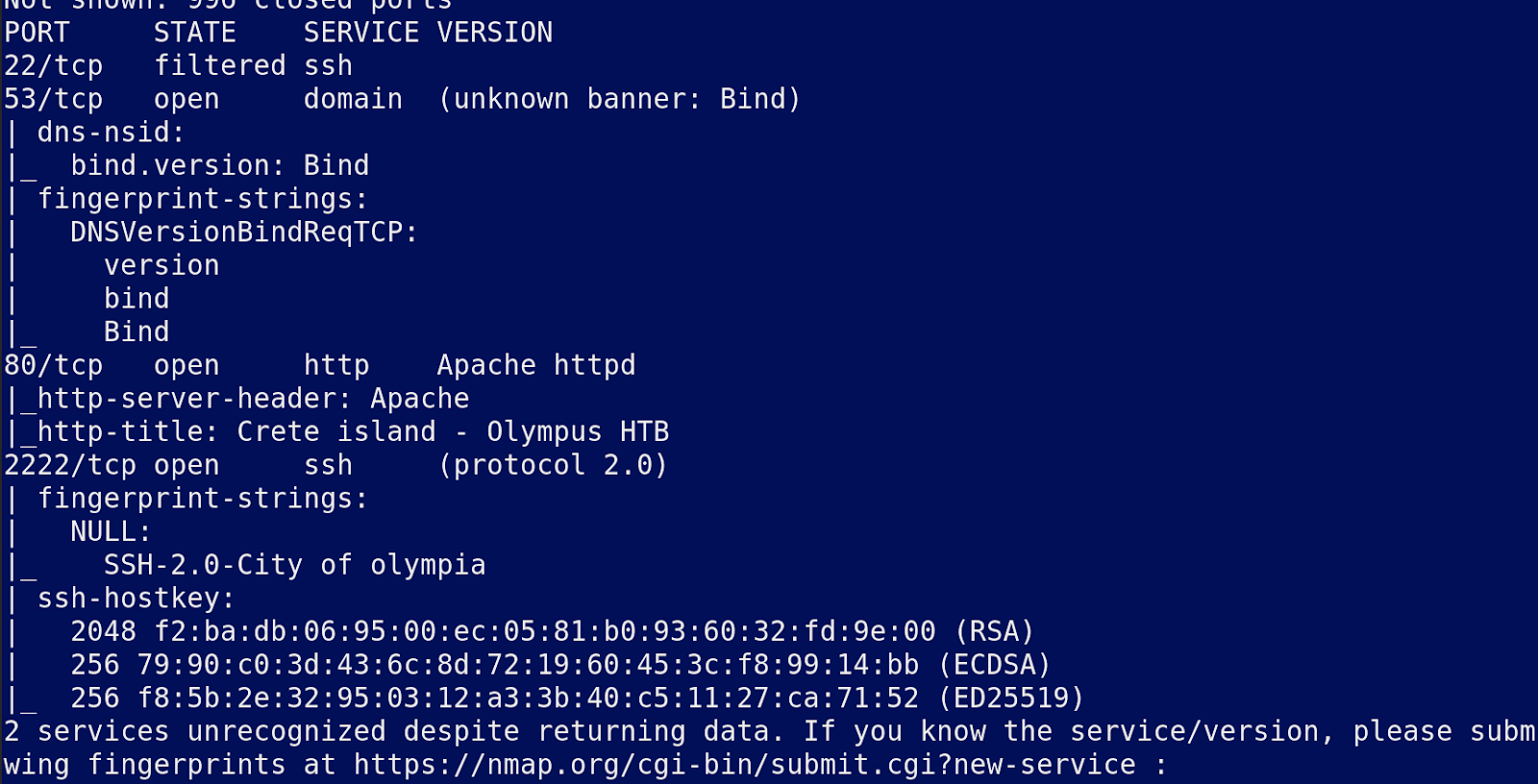
### Ports / Services / Software Versions Running
22/tcp filtered ssh
53/tcp open domain (unknown banner: Bind)
80/tcp open http Apache httpd
2222/tcp open ssh (protocol 2.0)
### Vulnerability Exploited:
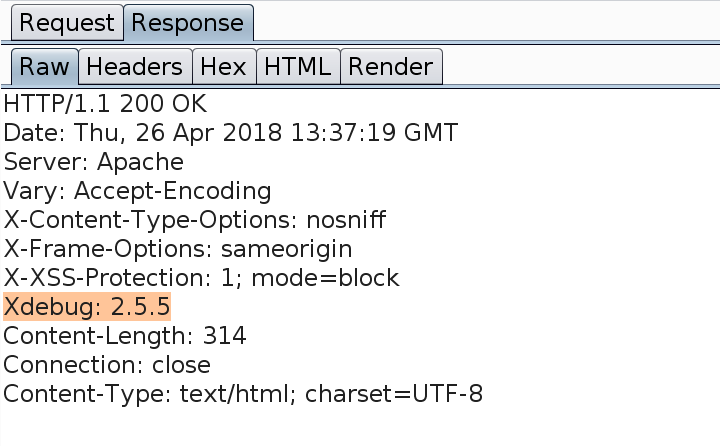
XDebug running on web server allows remote code execution.
### Privilege Escalation:
Vulnerable docker container allows user to execute commands as the root user.
### Exploiting the host:
Nmap
Nothing found on the webapp
One interesting header