# Jeeves
## Jeeves - 10.10.10.63
### Target Enumeration:
OS: Windows
IP: 10.10.10.63
User Hash: e3232272596fb47950d59c4cf1e7066a
Root Hash: afbc5bd4b615a60648cec41c6ac92530
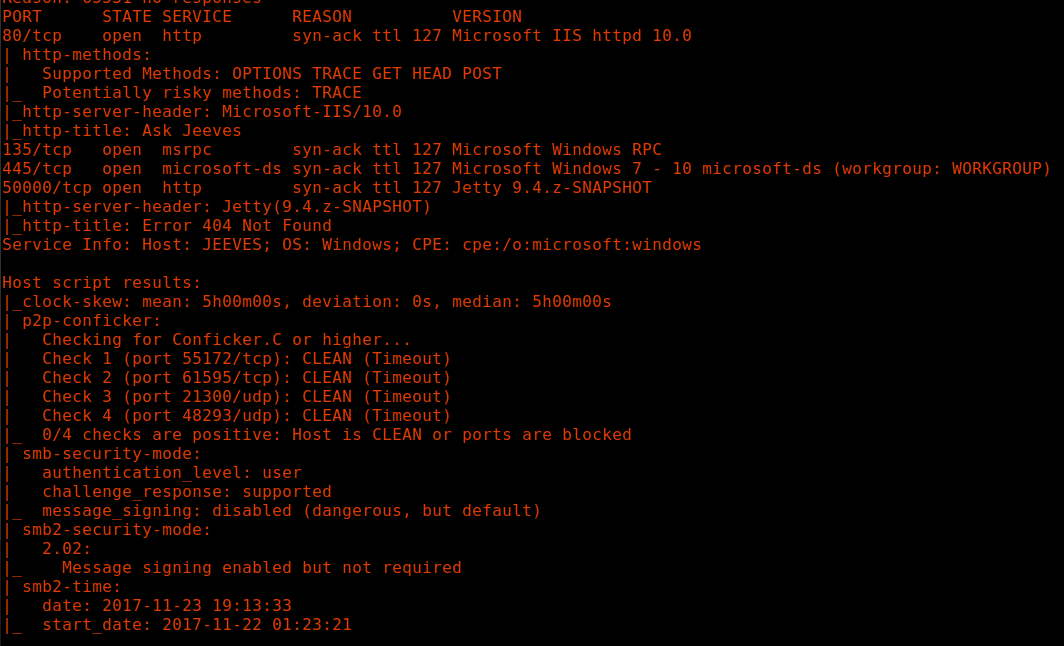
### Ports / Services / Software Versions Running
80/tcp open http syn-ack ttl 127 Microsoft IIS httpd 10.0
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
445/tcp open microsoft-ds syn-ack ttl 127 Microsoft Windows 7 - 10 microsoft-ds (workgroup: WORKGROUP)
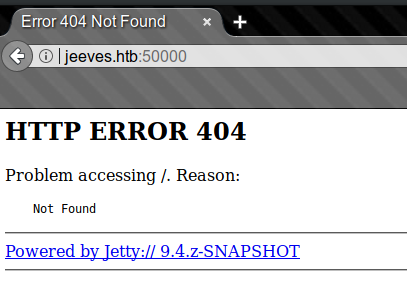
50000/tcp open http syn-ack ttl 127 Jetty 9.4.z-SNAPSHOT
Service Info: Host: JEEVES; OS: Windows; CPE: cpe:/o:microsoft:windows
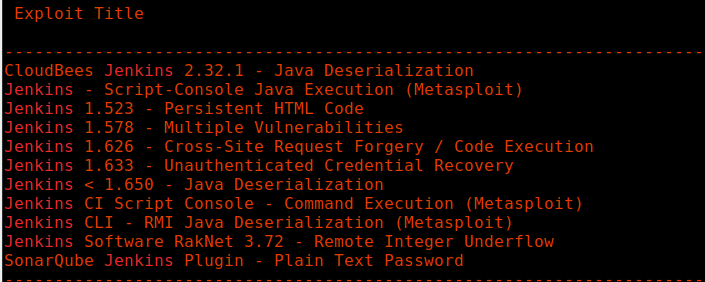
### Vulnerability Exploited:
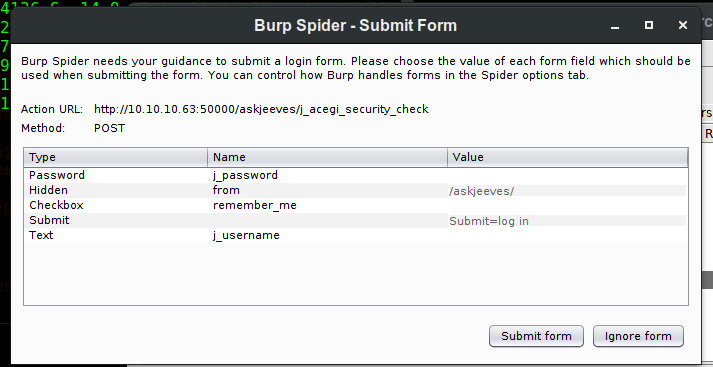
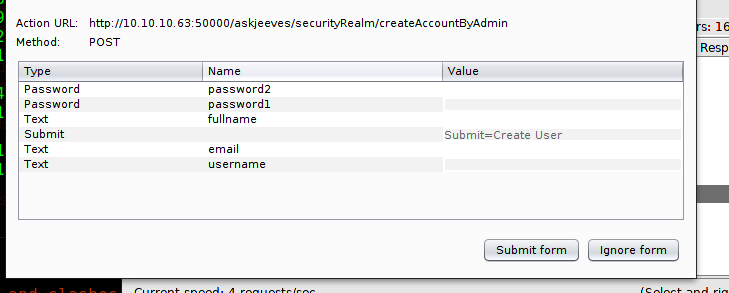
Jenkins /script enabled unauthenticated on port 50000
### Privilege Escalation
Administrator hash stored in keepass file with weak password.
### Replicating the exploit:
Nmap TCP
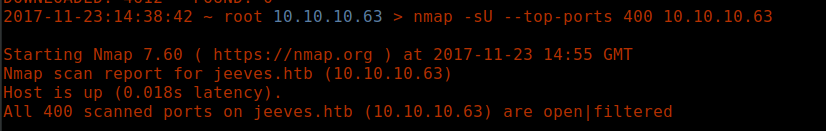
Nmap UDP:
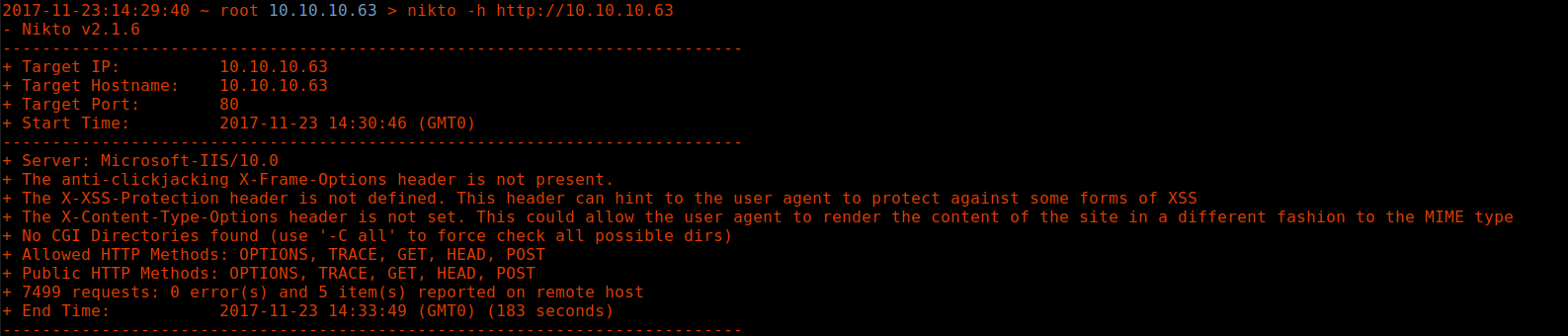
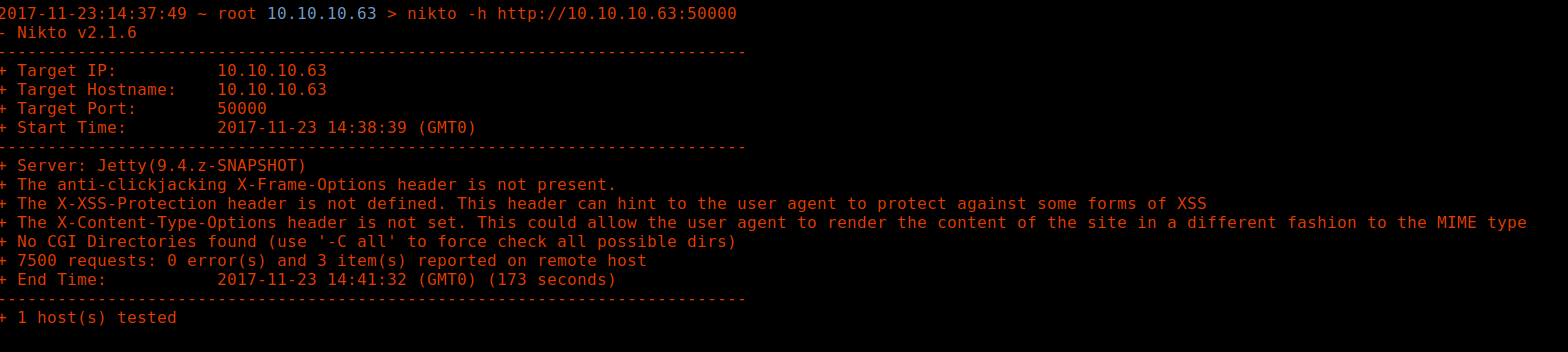
Nikto:
Port 80
Port 50000
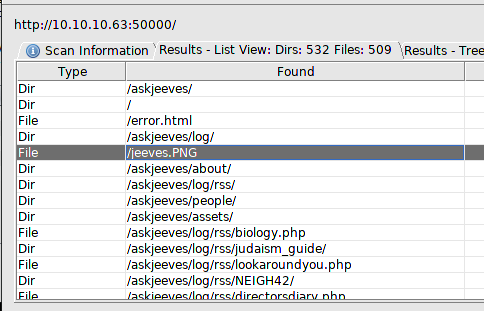
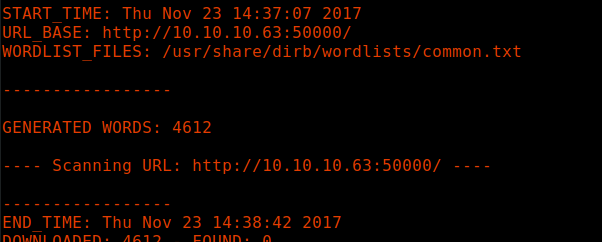
Dirb:
Port 80
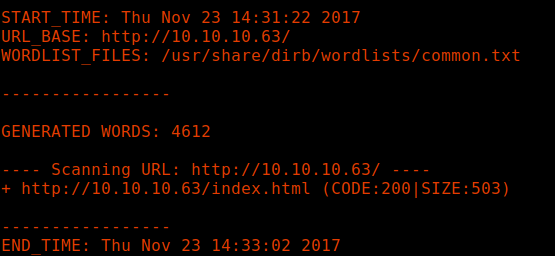
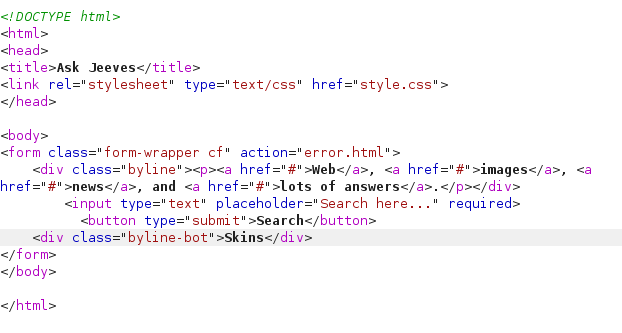
Come back to this.
Finally found some dirs