# Blocky
## Blocky - 10.10.10.37
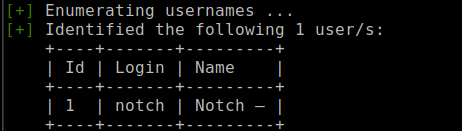
### Target Enumeration:
OS: Linux
IP: 10.10.10.37
User: 59fee0977fb60b8a0bc6e41e751f3cd5
Root: 0a9694a5b4d272c694679f7860f1cd5f
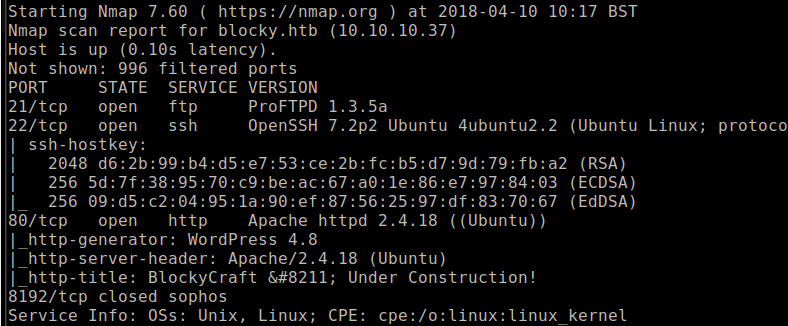
### Ports / Services / Software Versions Running
21/tcp open ftp ProFTPD 1.3.5a
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
8192/tcp closed sophos
### Vulnerability Exploited:
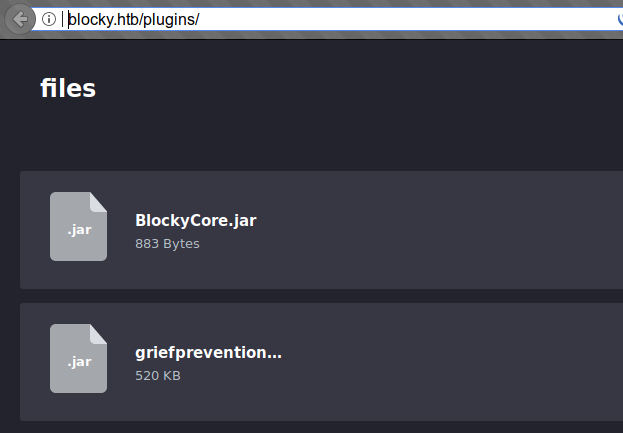
Password was stored in a .jar file which was valid for ssh and phpmyadmin.
### Privilege escalation:
User was in sudoers group
### Exploiting the host:
Nmap
Port 80 appears to be running wordpress.